5 ways to hack Blockchain in the enterprise
Blockchain Development Technology is a hot topic not only in the finance, cryptocurrency, etc. industries but also in the cybersecurity industry. This technology is still in an initial phase, you know like ‘work in progress’. Hence, I think it would be too early to call it a 100 percent secure technology.
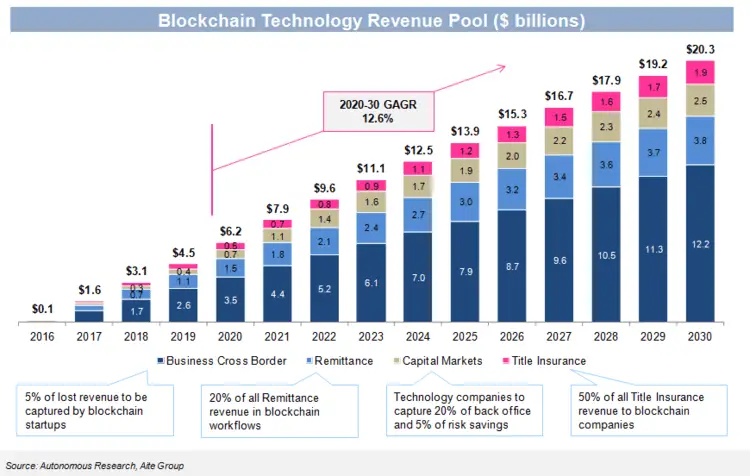
It is estimated, that the blockchain-centered technology companies are expecting their revenue to rise beyond $6 billion by 2020.
Well, this is the good news, isn’t it? But unfortunately, that’s not all. Yes, there’s a flip side too, that the actual profits may be paralyzed or bumped, if the security vulnerabilities of blockchain remain neglected in the discussion on this distributed ledger technology.
The blockchain application development is a security technology itself but it is stranded in security values. Hacks of Bitcoin exchanges are possible in open and public networks where anyone can create a node, but with enterprise blockchain applications, they are different from the public ones. They are private and permission networks and not accessible to everyone.
Although blockchain may be a hard target for hackers but it is not invincible. Blockchain specialists have warned that blockchain developments can bring vulnerabilities with them which organizations need to be aware of.
Is your organization, too, working on enterprise blockchain applications? Are you aware of the security susceptibilities that can turn into hacks? Following is a list of the top 5 (such) security weaknesses that can lead to enterprise hacks.
The blockchain access – public or private key:
One of the most probable exposure originates outside the blockchain implementation itself. Terminus or technically termed ‘endpoint’ is the point of contact of humans and the blockchain technology.
Blockchain can be entered via both public or private keys. These keys are encrypted strings of characters of appropriate length to make the possibilities of guessing them nearly exorbitant. Since it is impossible to access any data on the blockchain without the exact combination of the private and public keys, this shows both the strength and weakness of this technology.
Strength as in no hacker can access the data without the key. But on the contrary, all a hacker will need to access the information is the right key and then they can do anything with your data. Owning the keys is as good as owning the complete blockchain. The best way to get these keys is to hack the device of the user – the laptop or mobile.
Risk around the vendors:
As blockchain gains more acceptance, the market for third-party solutions will grow. The top areas of blockchain implementation in which we can expect the biggest third-party solutions include blockchain integration platforms, wallets, payment platforms, etc. This urgency of blockchain solutions will create a burgeoning market for blockchain developments.
Along with this, the potential for exposure through vendor risks also surfaces; organizations can have secure blockchain solutions if they have trustworthy vendors. Feeble security on their own platforms, erroneous code and also personnel weaknesses can expose a customers’ blockchain credentials and information to the illegal entity. This threat holds more risks in terms of ‘smart contracts’.
On the beam ‘full scale’ scenario:
The blockchain architecture is inherently scalable but no one knows what will happen at full scale? When certain changes are made, it scales up by one node. The growth of a blockchain poses two major risks as per FSOC (Financial Stability Oversight Council) – a US-based federal organization.
Firstly, today’s blockchain is limited and hence we are accustomed to handling and resolving problems only in this ‘limited’ territory. But with every GB expansion, the experience will come with its price, which is till now not high enough to need any major change in the complete system.
Secondly, we may be susceptible to the so-called 51% problems, a fraud in which a majority of participants may not be legitimate and may conspire against the other participants. This threat could be real if a large number of mining firms are created in nations where electricity is easily affordable.
The absence of Principles and Statute:
Forbs ad reported that one of the main security weakness of blockchain is the absence of principles and law. The mere reference of laws and standards put blockchain radicals on a vigilance. The absence of standard procedures and protocols means that the blockchain developers can’t learn from the mistakes of others.
If each company, each association, and each application is working and following rules that are apples and oranges, the risks that arise from a custom-built technology of any kind are at hand. Further, sometime, chains may be needed to be integrated. The absence of standards will result in security threats from merging diverse technology implementations.
Hypothetical code:
Despite its existence for 8 years with Bitcoin, blockchain not related to cryptocurrency remains experimental and hypothetical. Just to advertise themselves some organizations are eager to deploy their untested code on live blockchains or an altogether new blockchain. An awful example of such activity is the DAO attack.
The background – A DAO is a Decentralized Autonomous Organization developed on the blockchain, its purpose is to execute code for enterprise principal smart contracts. One such DAO was created in 2016 by the Ethereum team which was hacked while it was creating history by raising $150 million crowdfunds.
The hacker was aware of the weaknesses of the DAO code and he created a child DAO account and made repetitive requests to transfer the money from the first account in the chain. Since the code didn’t reduce the original balance after each transfer, nothing could stop the tokens from being replicated almost 40 times. After transferring $55 million from Ether, the hacker ended the theft. The reason behind why the hack was stopped in between is still unknown.
Ending Thoughts:
Blockchain, on one hand, has an extreme potential to change the world but on the other hand, it is in its initial stage with its own vulnerabilities. Hence, organizations have to think about the business use cases, the risks, the platform weaknesses, etc. and then implement their solutions with high security and an in and out testing.






