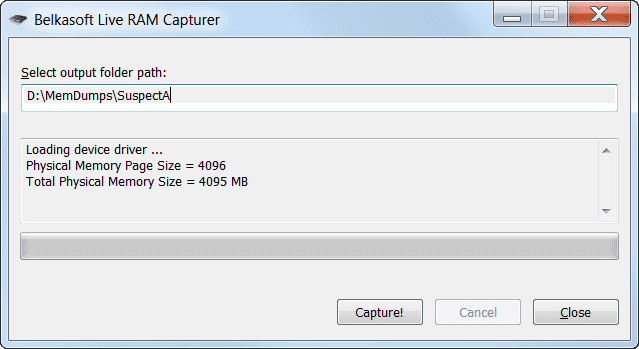
Belkasoft Live RAM Capturer is a small, free forensic tool that allows you to securely retrieve absolutely all the contents of the computer’s volatile memory, even if it is protected by an active anti-debugging and nti-dumping system. Also available are separate 32-bit and 64-bit assembly, whose task is to leave the instrument as small as possible traces. Memory dumps discovered by Belkasoft Live RAM Capturer can be analyzed in Live RAM Analysis Belkasoft Evidence Center. compatible with all versions and editions of Windows, including XP, Vista, Windows 7, 8 and 10, 2003 and 2008 Server.
Why Memory Dump Is the First Thing To Do During the Acquisition
Memory dumps are a valuable source of ephemeral evidence and volatile information. Memory dumps may contain passwords to encrypted volumes (TrueCrypt, BitLocker, PGP Disk), account login credentials for many webmail and social network services such as Gmail, Yahoo Mail, Hotmail; Facebook, Twitter, Google Plus; file sharing services such as Dropbox, Flickr, SkyDrive, etc.
In order to extract ephemeral evidence out of already captured memory dumps, forensic experts must use proper analysis software such as Belkasoft Evidence Center. Besides, some other tools can be used to extract passwords to encrypted volumes (e.g. Elcomsoft Forensic Disk Decryptor).
Designed to Bypass Active Anti-Debugging and Anti-Dumping Protection
Acquiring volatile memory from a computer running a debugging protection or anti-dumping system is tricky. Most memory acquisition tools run in the system’s user mode and are unable to bypass the defense of such protection system (which run in the systems’ most privileged kernel mode).