Brute Shark v1.2.5 releases: Network Analysis Tool
Brute Shark
Brute Shark is a Network Forensic Analysis Tool (NFAT) that performs deep processing and inspection of network traffic (mainly PCAP files). It includes: password extracting, building a network map, reconstruct TCP sessions, extract hashes of encrypted passwords, and even convert them to a Hashcat format in order to perform an offline Brute Force attack.
The main goal of the project is to provide a solution to security researchers and network administrators with the task of network traffic analysis while they try to identify weaknesses that can be used by a potential attacker to gain access to critical points on the network.
Two Brute Shark versions are available, A GUI-based application (Windows) and a Command Line Interface tool (Windows and Linux).
The various projects in the solution can also be used independently as infrastructure for analyzing network traffic on Linux or Windows machines. For further details see the Architecture section.
The project was developed in my spare time to address two main passions of mine: software architecture and analyzing network data.
What it can do
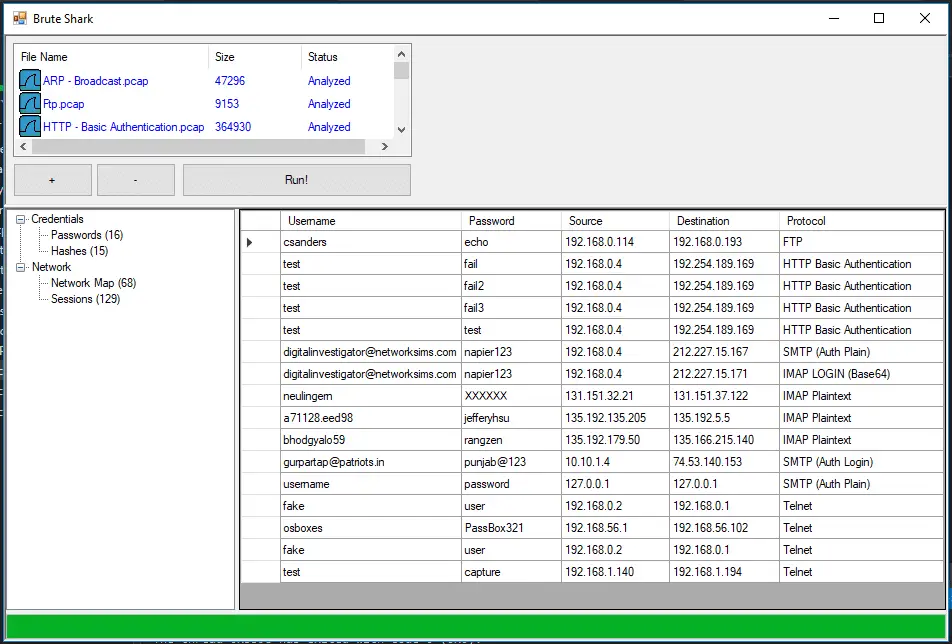
- Extracting and encoding user credentials
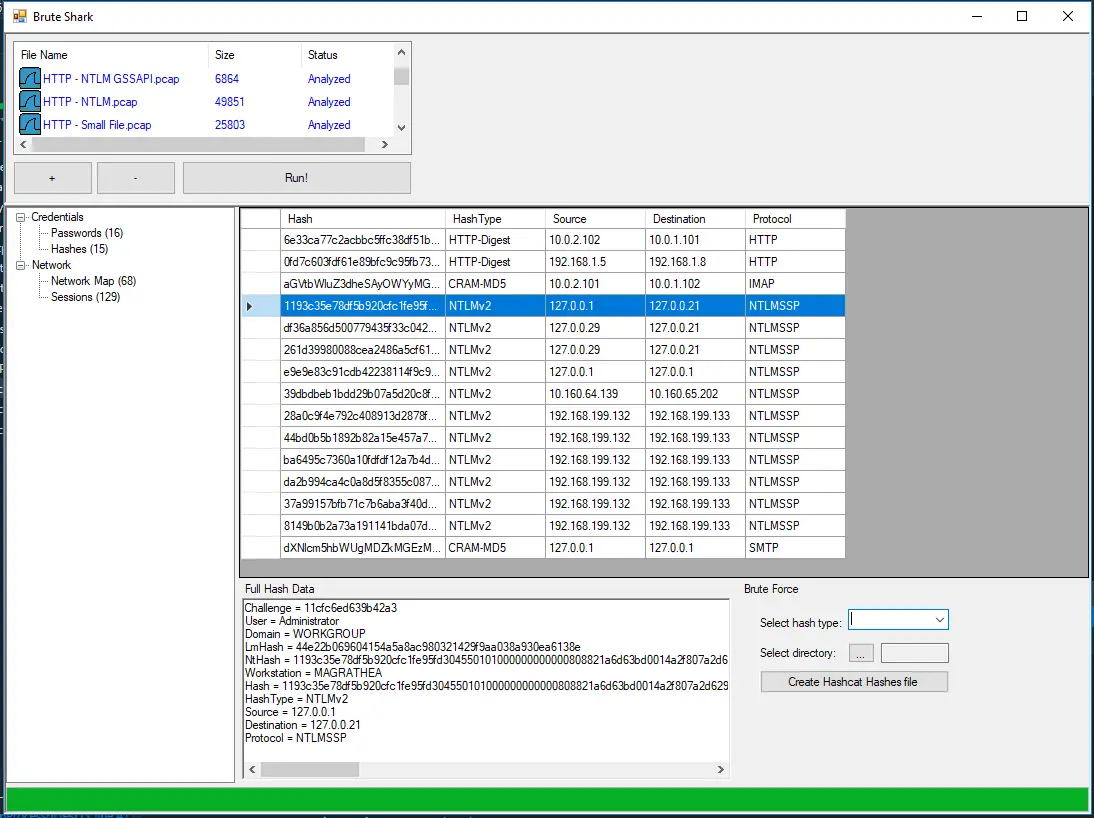
- Extract authentication hashes and crack them using Hashcat
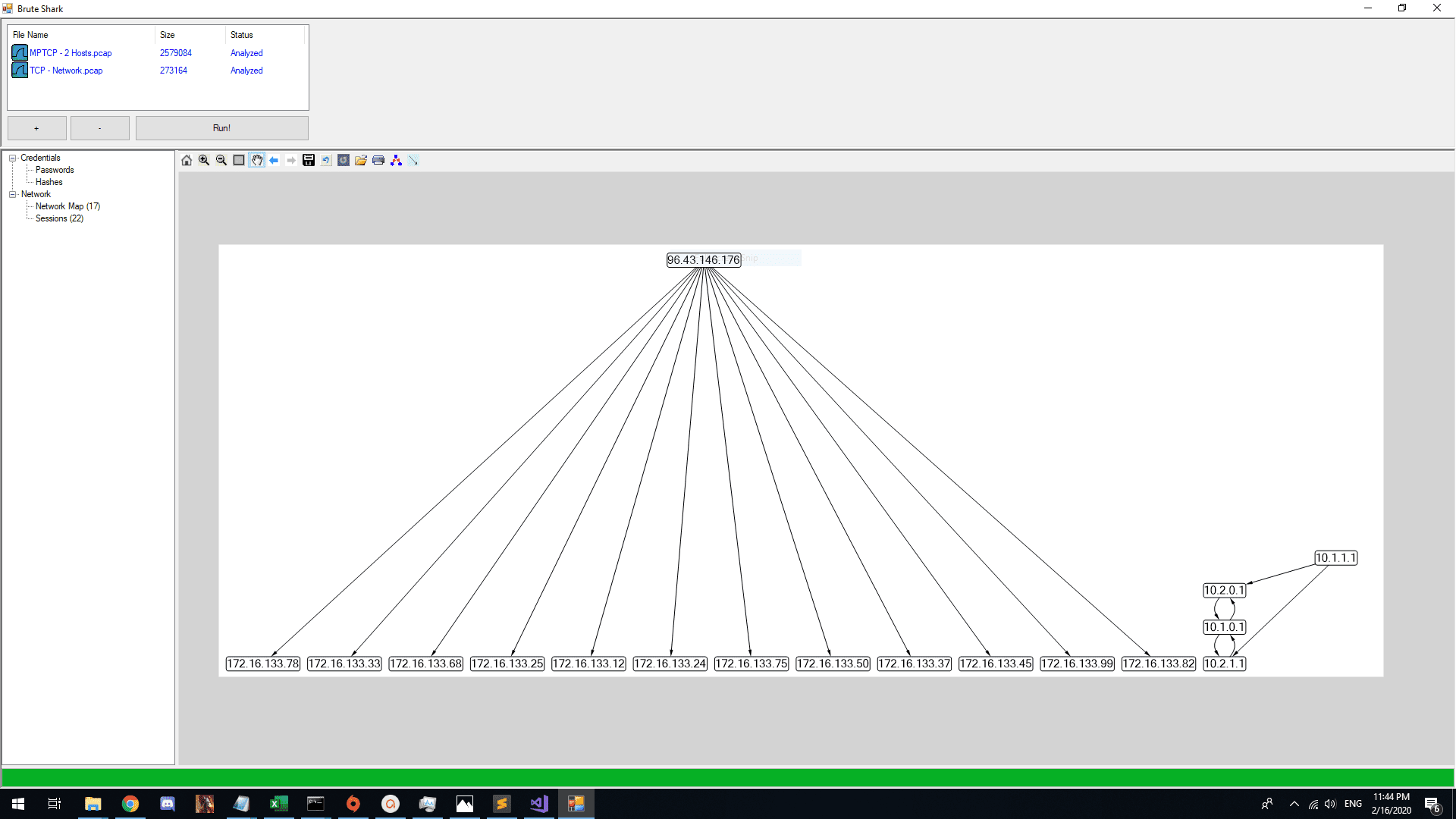
- Build visual network diagram
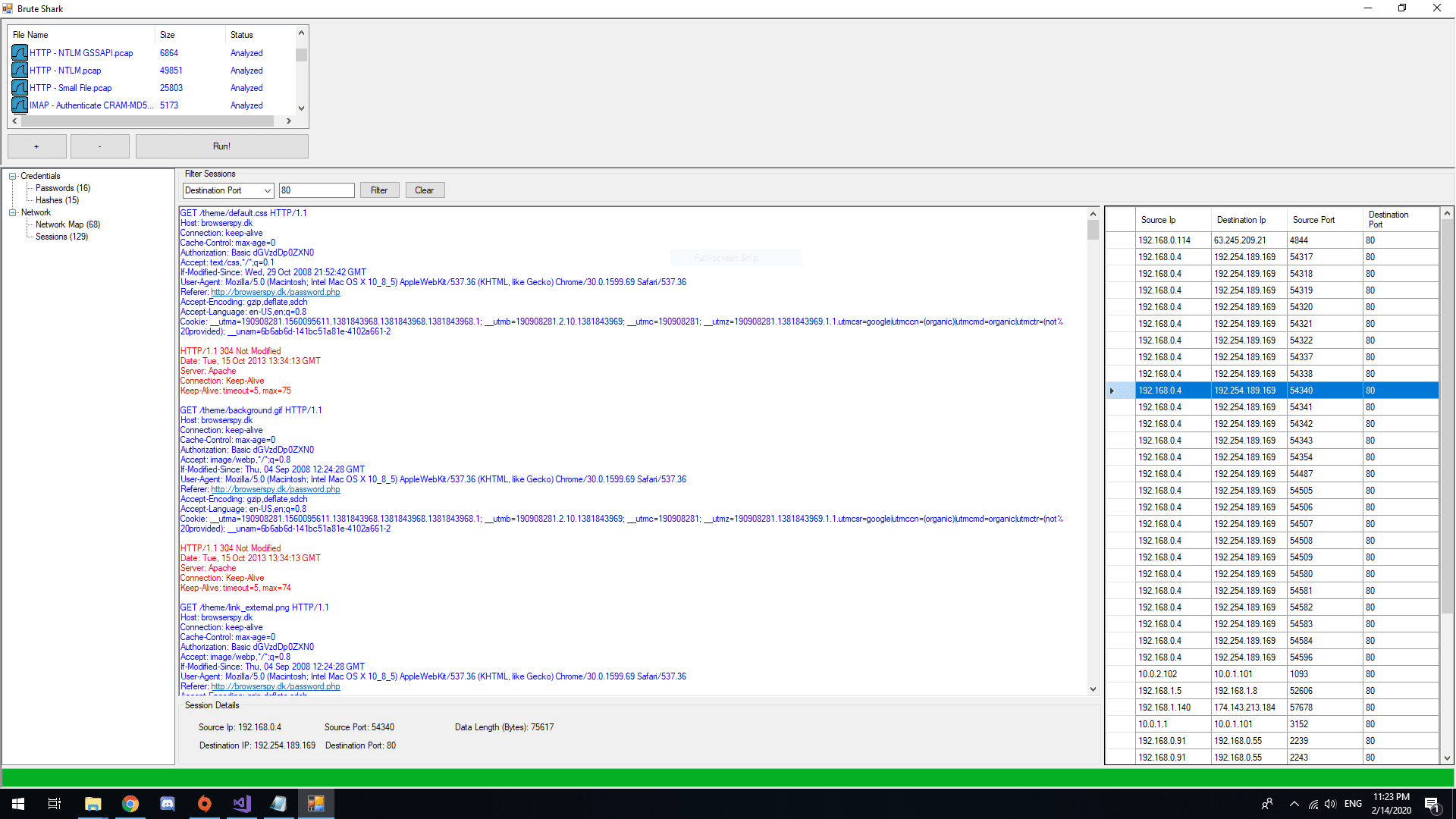
- Reconstruct all TCP Sessions
Password Extracting (HTTP, TELNET, IMAP, FTP, SMTP)
Hashes Extracting (HTTP-Digest, NTLM, CRAM-MD5)
Building a Network Diagram
Reconstruct all TCP Sessions
Changelog v1.2.5
This version contains few improvements and features:
First, the network map had upgraded by adding additional fields that enables to get insights about domain users and the amount of data transferred from each point in the network:
- Sent data – The amount of data (bytes) sent by the host.
- Received data – The amount of data received (bytes) by the host.
- Domains – the domains that the host is a member of.
- Domain users – domain users that logged into the host.
This fields will also appear at the “BruteShark Network Nodes Data.json” file that holds all the nodes details.
Secondly, the BruteSharkDesktop installer file was upgraded:
- Allow to upgrade existing version of BruteSharkDesktop without the need to manually remove the old version.
- Set the license also at the installer prompt.
This version of BruteSharkDesktop also includes a feature of notifying about new versions released.
Download && Use
Copyright (C) 2020 odedshimon