Category: Maintaining Access
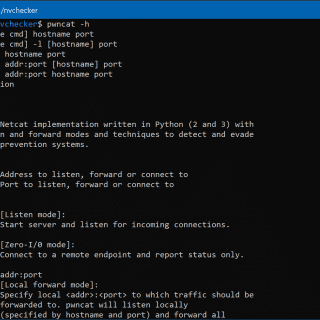
pwncat Netcat with Firewall and IPS evasion, bind and reverse shell, local and remote port-forward. Motivation Ever accidentally hit Ctrl+c on your reverse shell and it was gone for good? Ever waited forever for your client...
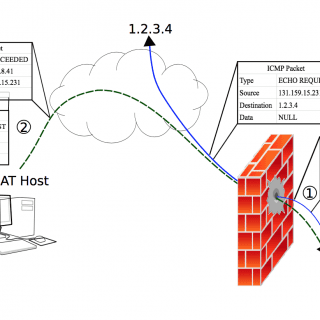
NAT Tunnel If you have access to a server with public IP and unfiltered ports you can run NAT Tunnel (NT) server on the server, and NT client on your box behind NAT. the...
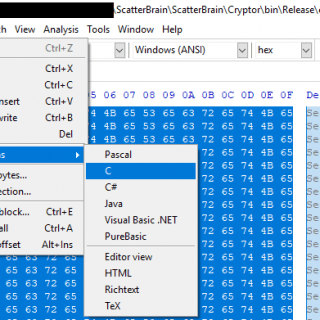
ScatterBrain Suite ScatterBrain is a shellcode runner with a variety of execution and elevation options. Given unencoded shellcode, it will then be encoded with the XOR key SecretKey (found in Cryptor/Program.cs and ScatterBrain/Headers/RawData.h) using the Cryptor binary. Cryptor.exe...
baboossh BabooSSH allows you, from a simple SSH connection to a compromised host, to quickly gather info on other SSH endpoints to pivot and compromise them. Install git clone https://github.com/cybiere/baboossh.git cd baboossh pip3 install...
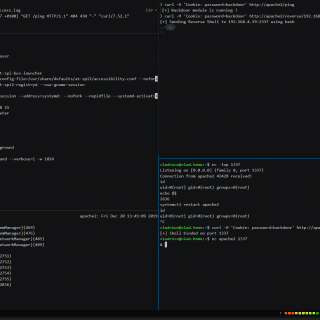
Apache2 mod_backdoor mod_backdoor is a stealth backdoor using an Apache2 module. The main idea is to fork() the primary Apache2 process just after it has loaded its config. Since it’s forked before the root...
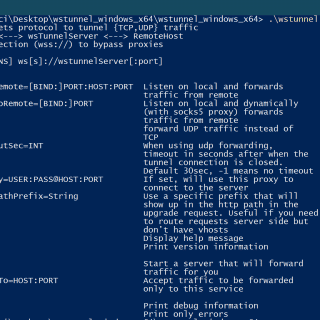
wstunnel Most of the time when you are using a public network, you are behind some kind of firewall or proxy. One of their purposes is to constrain you to only use certain kinds...
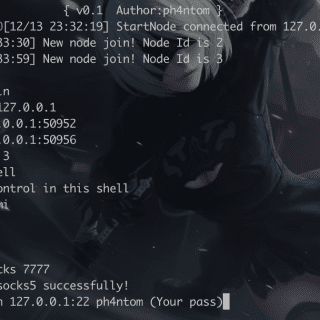
Stowaway Stowaway is a Multi-hop proxy tool for security researchers and pentesters Users can easily proxy their network traffic to intranet nodes (multi-layer) PS: The files under the demo folder are Stowaway’s beta version,...
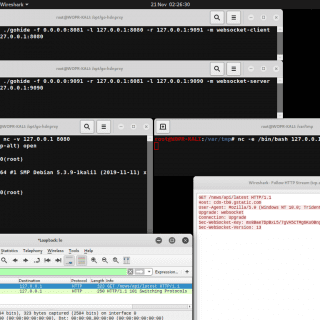
gohide The tunnel TCP port to port traffic via an obfuscated channel with AES-GCM encryption. Obfuscation Modes Session Cookie HTTP GET (http-client) Set-Cookie Session Cookie HTTP/2 200 OK (http-server) WebSocket Handshake “Sec-WebSocket-Key” (websocket-client) WebSocket...
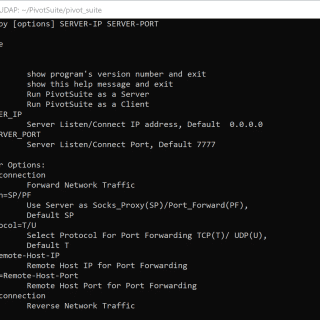
PivotSuite PivotSuite: Hack The Hidden Network – A Network Pivoting Toolkit It is a portable, platform-independent and powerful network pivoting toolkit, Which helps Red Teamers / Penetration Testers to use a compromised system to...
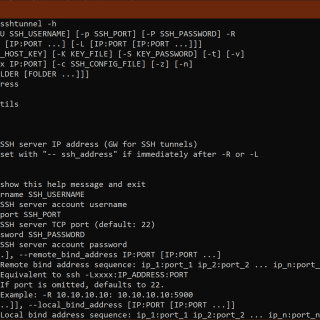
ssh tunnel SSH tunnels to a remote server.API allows either initializing the tunnel and starting it or using a with context, which will take care of starting and stopping the tunnel. Usage scenarios One of...
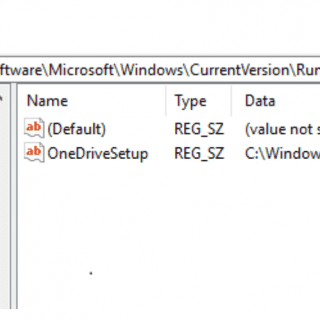
SharpHide Just a nice persistence trick to confuse DFIR investigation. Uses NtSetValueKey native API to create a hidden (null-terminated) registry key. This works by adding a null byte in front of the UNICODE_STRING key...
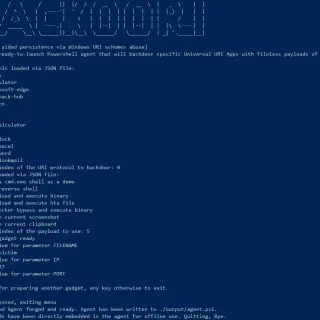
backoori Backoori (“Backdoor the URIs”) is a Proof of Concept tool aimed to automate the fileless URI persistence technique in Windows 10 targets. Abstract of the Research behind the tool The widespread adoption of...
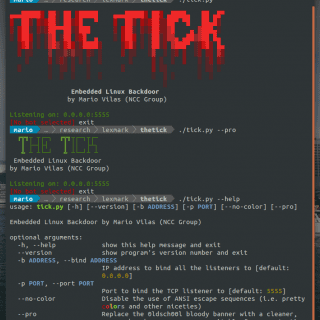
The Tick A simple embedded Linux backdoor. Compiling The Tick depends only on libcurl, so make sure you have the corresponding development package. For example on Debian based distributions you would do the following:...
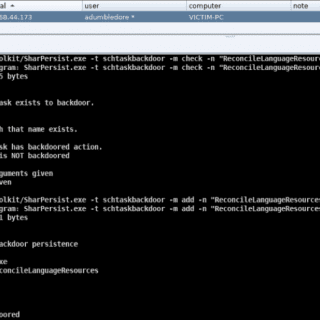
SharPersist Windows persistence toolkit is written in C#. Overview SharPersist was created in order to assist with establishing persistence on Windows operating systems using a multitude of different techniques. It is a command-line tool...
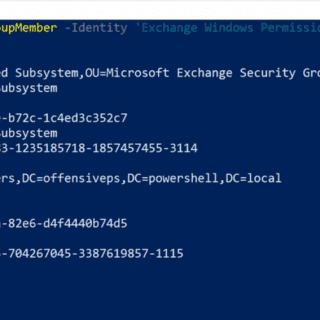
RACE RACE is a PowerShell module for executing ACL attacks against Windows targets and Active Directory. RACE can be used for persistence and on-demand privilege escalation on Windows machines. Functions Set-RemotePSRemoting Use this function...