Category: Tips and Tricks
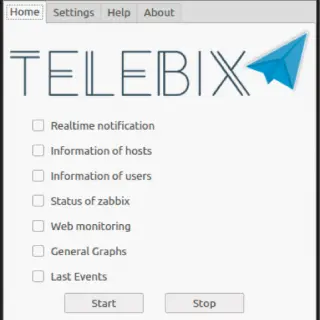
Telebix Telebix is an application that communicates with a Bot on the Telegram to receive commands and send information from an infrastructure monitored by Zabbix, which also sends messages in real time if any...
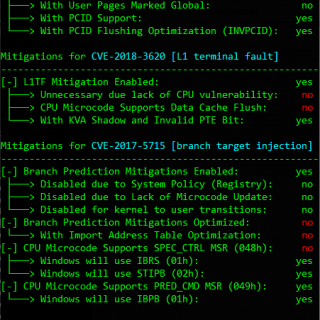
SpecuCheck is a Windows utility for checking the state of the software and hardware mitigations against CVE-2017-5754 (Meltdown), CVE-2017-5715 (Spectre v2), CVE-2018-3260 (Foreshadow), and CVE-2018-3639 (Spectre v4). It uses two new information classes that...
GhostInTheChaos Chaotic Crypto Stealth VPN for Anonymity and Untraceable Hacking Attacks with Linux and Android. Properties: Protects client from sniffing and tracing Protects server from attacks and scanning Bypasses censorship and network filtering Transparent...
Linux has long been used as an operating system, powering everything from supercomputers to smartphones. For those who have been in the Microsoft or Apple systems for a long time, it can be intimidating....
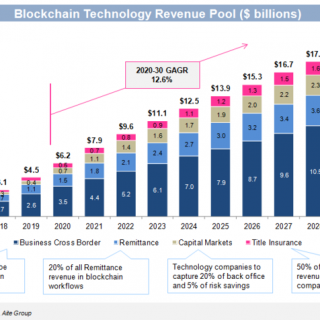
Blockchain Development Technology is a hot topic not only in the finance, cryptocurrency, etc. industries but also in the cybersecurity industry. This technology is still in an initial phase, you know like ‘work in...
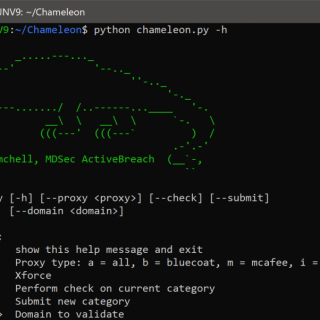
Chameleon is a tool which assists red teams in categorising their infrastructure under arbitrary categories. Currently, the tool supports arbitrary categorisation for Bluecoat, McAfee Trustedsource and IBM X-Force. However, the tool is designed in...
PowerShdll Run PowerShell with dlls only. Does not require access to powershell.exe as it uses powershell automation dlls. Does not require access to powershell.exe as it uses powershell automation dlls. PowerShdll can be run...
Security Scenario Generator (SecGen) Summary SecGen creates vulnerable virtual machines so students can learn security penetration testing techniques. Boxes like Metasploitable2 are always the same, this project uses Vagrant, Puppet, and Ruby to quickly...
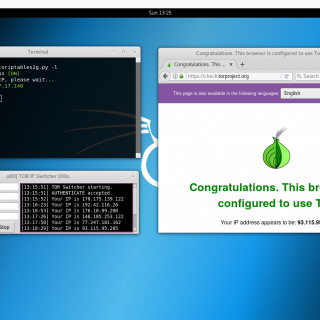
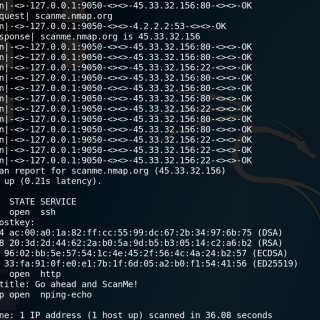
toriptables2 Tor Iptables script is an anonymizer that sets up iptables and tor to route all services and traffic including DNS through the Tor network. Download git clone https://github.com/ruped24/toriptables2.git Use toriptables2.py -h To test: Check...
takeover.sh A script to completely take over a running Linux system remotely, allowing you to log into an in-memory rescue environment, unmount the original root filesystem, and do anything you want, all without rebooting....
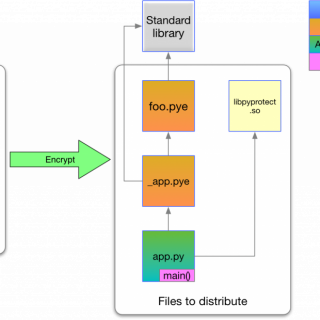
pyprotect pyprotect is a lightweight python code protector, makes your python project harder to reverse engineer. Features Cross-platform No need to install any extra dependents Very easy to use Only python3.x is supported by current...
sshnotify A script to notify you when others login your server via ssh. install Debian/ubuntu supported wget -N –no-check-certificate https://raw.githubusercontent.com/Green-m/sshnotify/master/install.sh && chmod +x install.sh && bash install.sh Use whitelist config vim /etc/sshnotify/whitelist.config white_user=(root test)...
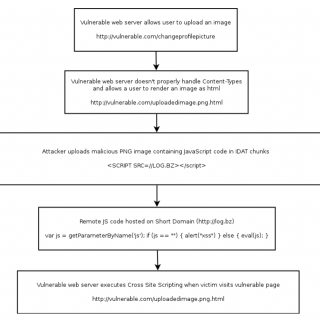
PNG-IDAT-Payload-Generator Generate a PNG with a payload embedded in the IDAT chunk (Based off of previous concepts and code — credit given below) Additionally, bruteforce payloads matching a regex pattern ##Based Off of Previous...
Tor is a connection-based low-latency anonymous communication system. Clients choose a source-routed path through a set of relays and negotiate a “virtual circuit” through the network, in which each relay knows its predecessor and...
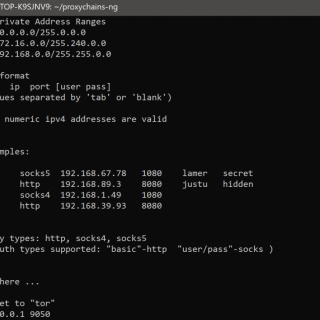
proxychains-ng (new generation) – a preloader which hooks calls to sockets in dynamically linked programs and redirects it through one or more socks/http proxies. continuation of the unmaintained proxychains project. ProxyChains is a UNIX...