checkpot: Checkpot Honeypot Checker
Checkpot is a honeypot checker: a tool meant to detect mistakes in the configuration of honeypots. It is aimed at security researchers who wish to check that their honeypots are properly set up, so they can be as hard to detect as possible and attract high-quality traffic. According to recent studies, honeypots using default or incorrect settings are surprisingly widespread all over the internet so we consider Checkpot to be very relevant.
“Many researchers fail deploying honeypots that are easily detectable. There are trivial mistakes people can make when deploying a honeypot like leaving the default settings or templates. On the other hand there are some non-direct indicators of a honeypot including but not limited to running both Windows and Linux services on the same box or having two different ssh servers listening on the same IP. The goal of this project would be to create a simple and open source honeypot detection tool that would scan an IP looking for any traces of a honeypot and create a report with findings and their severity. Using this tool a researcher can scan their system before putting it online or in production and based on the report perform the necessary tuning.” – Honeynet GSoC 2018 project proposal
Disclaimer
As this software is PROVIDED WITH ABSOLUTELY NO WARRANTY OF ANY KIND,
YOU USE THIS SOFTWARE AT YOUR OWN RISK!
By using this tool YOU TAKE FULL LEGAL RESPONSIBILITY FOR ANY POSSIBLE OUTCOME!
Keep in mind that this tool is based on port scanning and interacts with services on the target system in most cases. Even a simple port scan can be illegal in some jurisdictions. Please consult all laws that apply to your use case and make sure you understand exactly how the app works before you use it.
Install
- Read the Disclaimer above very carefully. Remember to USE CHECKPOT AT YOUR OWN RISK!
- If you do not understand the disclaimer stop now!
- Clone this repository locally:git clone https://www.github.com/honeynet/checkpot.git
- Install python3 (recommended version 3.5 or greater) and pip (pip3) using apt-get or tools like virtualenv or conda
- Install nmap using apt-get (or your distribution’s default package manager) or build it from source using archives provided on their site
- Install mercurial using apt-get (or your distribution’s default package manager). Mercurial is required for the download of a modified version of python-nmap (that displays progress bars while scanning) during the next step. Alternatively, you can pip install python-nmap from the official channels but you will not see any progress bars.
- Install all required packages from requirements.txt:pip install -r requirements.txt
- Optional: If you wish to run the automated tests or use the containers framework for development purposes install docker.io:sudo apt-get install docker.io
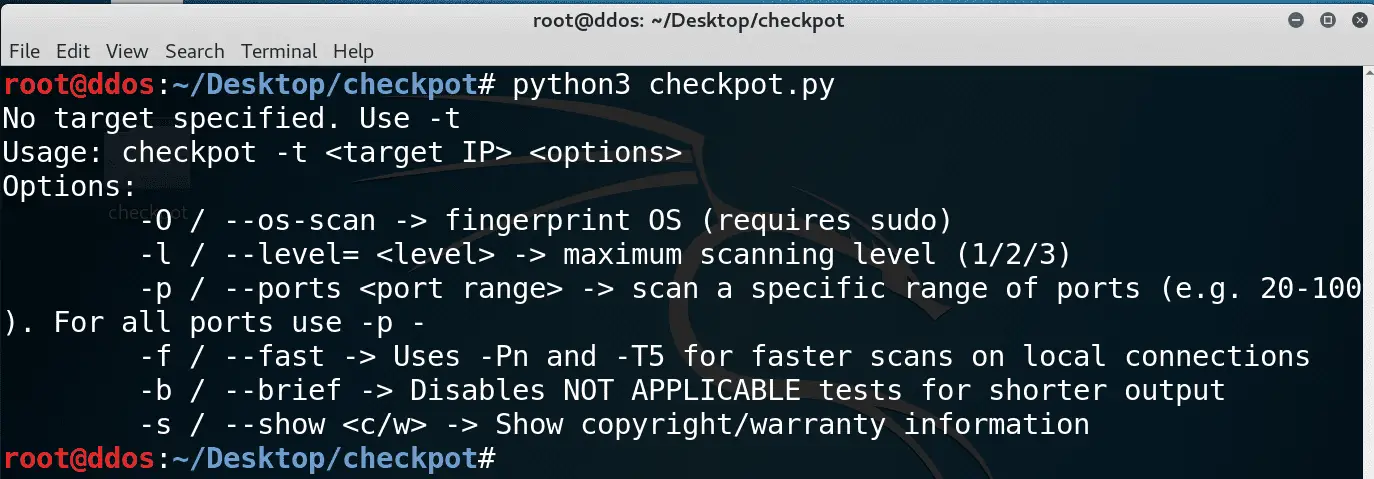
Use
python checkpot.py
Copyright (C) 2018 Vlad Florea
Source: https://github.com/honeynet/