chkrootkit v0.53 releases: detection rootkits & malware on Linux
Although the Linux system can be protected from the spread of most malware, it is not absolutely safe. If your data center erected a Linux server, especially the Web server, you should be on the rootkit Trojans and malicious software to prevent, because some of the data destruction class Rootkit is very dangerous, and the attacker once the invasion may be used after the site server malicious Software dissemination. How to eliminate such risks? One way is to use the correct security check tool.
chkrootkit
chkrootkit is a tool to locally check for signs of a rootkit, Worms and LKMs. It contains:
* chkrootkit: a shell script that checks system binaries forrootkit modification.
* ifpromisc.c: checks if the network interface is in promiscuous mode.
* chklastlog.c: checks for lastlog deletions.
* chkwtmp.c: checks for wtmp deletions.
* check_wtmpx.c: checks for wtmpx deletions. (Solaris only)
* chkproc.c: checks for signs of LKM trojans.
* chkdirs.c: checks for signs of LKM trojans.
* strings.c: quick and dirty strings replacement.
* chkutmp.c: checks for utmp deletions.
chkwtmp and chklastlog *try* to check for deleted entries in the wtmp and lastlog files, but it is *not* guaranteed that any modification will be detected.
Aliens tries to find sniffer logs and rootkit config files. It looks for some default file locations — so it is also not guaranteed it will succeed in all cases.
chkproc checks if /proc entries are hidden from ps and the readdir system call. This could be the indication of a LKM trojan. You can
also run this command with the -v option (verbose).
Changelog v0.53
- Rocke Monero Miner detection
- Added ss (netstat update comand) support
- ifconfig.c bug fix
- Minor bug fixes
Installation
On Debian/Ubuntu, you simply type a command
Usage
Open terminal, and type command
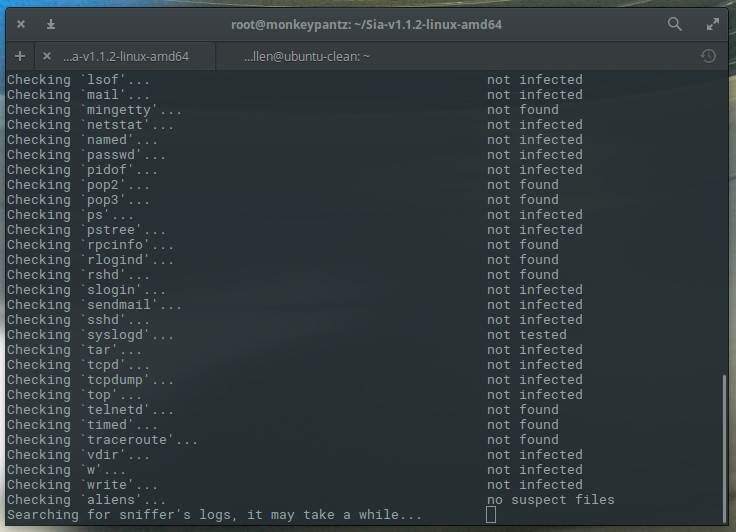
If there are some Rookit signs after the test, you can try to analyze the same, because some may be false positives. If there are other Rookit suspected reports, you will need to pay attention, carefully control the chkrootkit report analysis, find a solution problem, because the chkrootkit tool only provides detection, does not provide a solution or delete method.
Author
Copyright 1996-2009 – Pangeia Informatica, All rights reserved.
- Nelson Murilo <nelson@pangeia.com.br> (main author)
- Klaus Steding-Jessen <jessen@cert.br> (co-author)






