commix v3.9 releases: Automated All-in-One OS command injection and exploitation tool
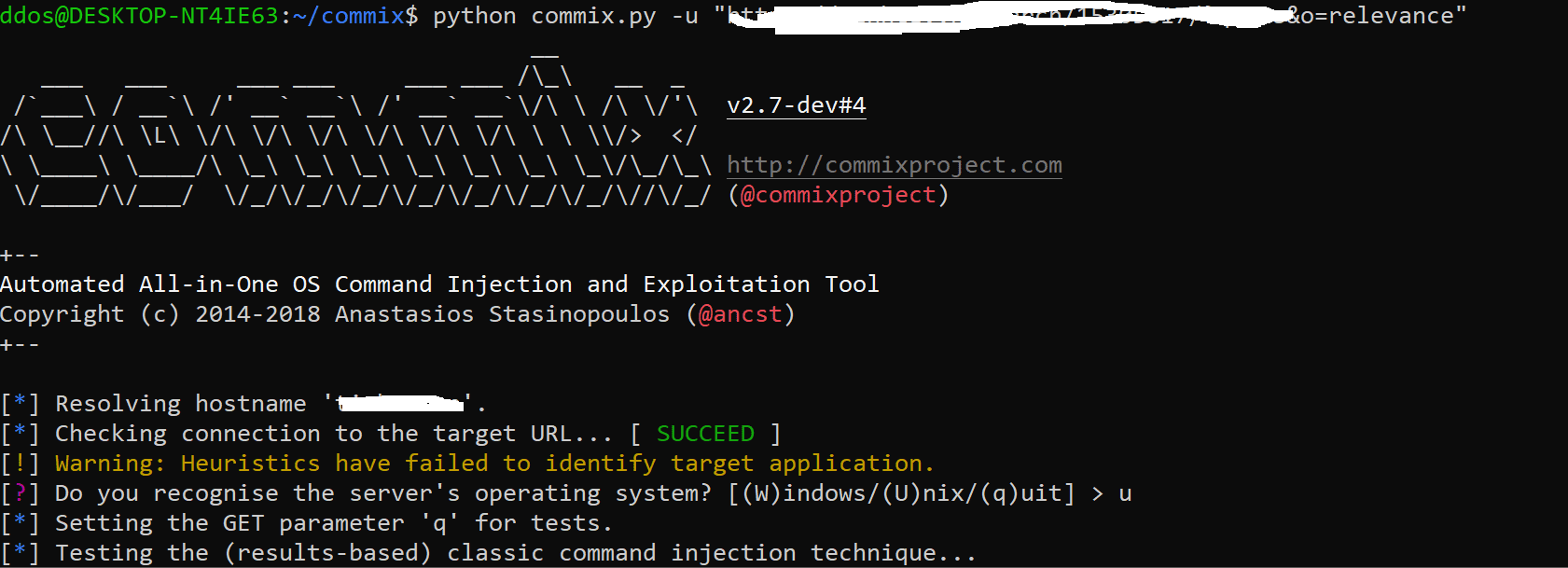
Commix (short for [comm]and [i]njection e[x]ploiter) is an automated tool written by Anastasios Stasinopoulos (@ancst) that can be used from web developers, penetration testers or even security researchers in order to test web-based applications with the view to find bugs, errors or vulnerabilities related to command injection attacks. By using this tool, it is very easy to find and exploit a command injection vulnerability in a certain vulnerable parameter or HTTP header.
Changelog v3.9
- Fixed: Multiple bug-fixes regarding several reported unhandled exceptions.
- Revised: Minor improvement regarding logging user-supplied command(s) (i.e.
--os-cmdoption) to a file. - Revised: Improvement regarding parsing HTTP requests through Tor HTTP proxy (i.e.
--torswitch). - Added: New (hidden) option
--ignore-stdinregarding ignoring STDIN input. (via @n00b-bot) - Revised: Minor improvement regarding successfully completing the scanning process (i.e. in case that parameters with anti-CSRF tokens are omitted). (via @xerxoria)
- Revised: Minor improvement regarding Windows-based payloads for semiblind (i.e. “file-based”) technique (i.e. command execution output).
- Revised: Minor improvement in semiblind (i.e. “file-based”) technique, regarding defining the URL where the execution output of an injected payload is shown.
- Added: New switch
--ignore-proxyto ignore the system default HTTP proxy. - Revised: Minor improvement regarding parsing HTTP requests through HTTP proxy (i.e.
--proxyoption). - Added: New switch
--smartfor conducting through tests only in case of positive heuristic(s). - Added: Translation for README.md in Turkish (via @Kazgangap)
- Revised: Minor improvement regarding parsing SOAP/XML POST data.
Techniques
1. Results-based command injections.
In results-based command injection attacks the attacker can directly infer the result of the injected command through the response of the web application. We divide results-based command injection attacks into the following two techniques.
1.1 Classic results-based command injection.
The classic results-based technique is the simplest and most common command injection attack. More specifically, the attacker makes use of several common operators, which either concatenate the initial genuine commands with the injected ones or exclude the initial genuine commands executing only the injected ones.
1.1.2 Shellshock.
The popular Shellshock bug which was discovered in a tool known as Bash that is widely used by the Unix operating system and many of its variants, including Linux open source software and Apple’s OSX. [1]
1.1.3 ICMP exfiltration.
The ICMP exfiltration technique, exfiltrates data using the ping utility. [1][2]
1.1.4 DNS exfiltration.
The DNS exfiltration technique, exfiltrates data using DNS requests. [1]
1.2 Dynamic code evaluation (aka eval-based) technique.
Command injections through dynamic code evaluation take place when the vulnerable application uses the eval() function, which is used to dynamically execute code that is passed (to the eval() function) at runtime. Thus, the dynamic code evaluation can also characterized as “executing code, which executes code”, since the eval() function is used to interpret a given string as code. Note that the eval() function is provided by many interpreted languages such as Java, Javascript, Python, Perl, PHP and Ruby.
2. Blind Command Injections.
The main difference between results-based command injection attacks and blind command injection attacks lies to the way that the data is retrieved after the execution of the injected shell command. More specifically, we have observed that there are cases where an application, after the execution of the injected command does not return any result back to the attacker. In these cases, the attacker can indirectly infer the output of theinjected command using the following two techniques.We divide blind command injection attacks into two different techniques:
- Time-based (Blind)
- File-based (Semiblind)
2.1 Time-based technique (Blind).
Through this technique, an attacker injects and executes commands that introduce time delay. By measuring the time it took the application to respond, the attacker is able to identify if the command executed successfully or failed. Note that the function in Bash shell that can introduce time delays is sleep. Thus, by observing time delays the attacker is capable of deducing the result of the injected command.
2.2 File-based technique (Semiblind).
The rationale behind this technique is based on a very simple logic: when the attacker is not able to observe the results of the execution of an injected command, then he/she can write them to a file, which is accessible to the attacker. This command injection technique follows exactly the same methodology as the Classic results-based technique with the main difference that, after the execution of the injected command, an output redirection is performed using the > operator, in order to save the output of the command to a text file. Due to the logic of this technique, the file-based can be also classified as semiblind command injection technique, as the random text file containing the results of the desired shell command execution is visible to everyone.
2.2.1 Tempfile-based technique (Semiblind).
An essential prerequisite to achieve this, is that the root directory on the web server (i.e., /var/www/) should be writable by the user that is running the web server (i.e. www-data). In case the root directory of the web server is not writable, an alternative solution for the attacker is to use temporary directories, such as /tmp or /var/tmp to store in a text file the output of the injected command. The limitation in this solution is that the attacker cannot read files located in these temporary directories through the web application, due to his/her limited privileges. To bypass this limitation, the attacker can apply the time-based command injection technique to read the contents of the text file. For example, the attacker can use the following HTTP GET request, in order to store the output of whoami command to a random file (i.e /tmp/UvlLSE5S.txt) and subsequently how many characters there are in this file.
Tutorial
Copyright (c) 2014-2018 Anastasios Stasinopoulos






