Get-bADpasswords: Get insights into the actual strength and quality of passwords in Active Directory
Get-bADpasswords
Get insights into the actual strength and quality of passwords in Active Directory.
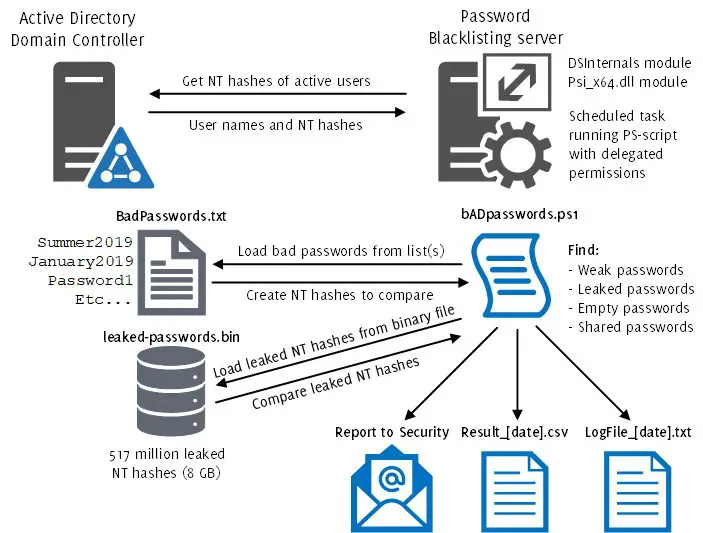
This module is able to compare password hashes of enabled Active Directory users against bad/weak/non-compliant passwords (e.g. hackers first guess in brute-force attacks).
- Performs a comparison against one or multiple wordlists (s).
- This script does not transform input from the wordlists (such as transforming between upper/lower case). Each input from the wordlist is used as-is. Use other tools to generate more specialized wordlists if necessary. A PoC-script has been included (New-bADpasswordLists_EN.ps1) for basic wordlist generation.
- Performs additional comparison against publicly leaked passwords, see acknowledgments below.
- Performs password comparison against ‘null’ in the Active Directory (i.e. finds empty/null passwords).
- Performs password comparison between users in the Active Directory (i.e. finds shared passwords).
- Requires ‘Domain Admin’ privileges or similar, e.g. ‘Domain Controller’ or delegated Domain-level permissions for both “Replicating Directory Changes All” and “Replicating Directory Changes All”, to successfully fetch passwords from the Active Directory database.
- Choose a Domain Controller or a member server (will become a Tier 0 system) for executing the script, e.g. as a Scheduled Task.
Download && Use
Copyright (c) 2018, Improsec ApS All rights reserved.