cypherhound: 260+ Neo4j cyphers for BloodHound data sets
cypherhound
A Python3 terminal application that contains 260+ Neo4j cyphers for BloodHound data sets.
Why?
BloodHound is a staple tool for every red teamer. However, there are some negative side effects based on its design. I will cover the biggest pain points I’ve experienced and what this tool aims to address:
- My tools think in lists – until my tools parse exported JSON graphs, I need graph results in a line-by-line format .txt file
- Copy/pasting graph results – this plays into the first but do we need to explain this one?
- Graphs can be too large to draw – the information contained in any graph can aid our goals as the attacker and we need to be able to view all data efficiently
- Manually running custom cyphers is time-consuming – let’s automate it 🙂
This tool can also help blue teams to reveal detailed information about their Active Directory environments as well.
Features
Take back control of your BloodHound data with cypherhound !
- 264 cyphers as of date
- Set cyphers to search based on user input (user, group, and computer-specific)
- User-defined regex cyphers
- User-defined exporting of all results
- Default export will be just end object to be used as target list with tools
- Raw export option available in grep/cut/awk-friendly format
Install
git clone https://github.com/fin3ss3g0d/cypherhound.git
python3 -m pip install -r requirements.txt
Use
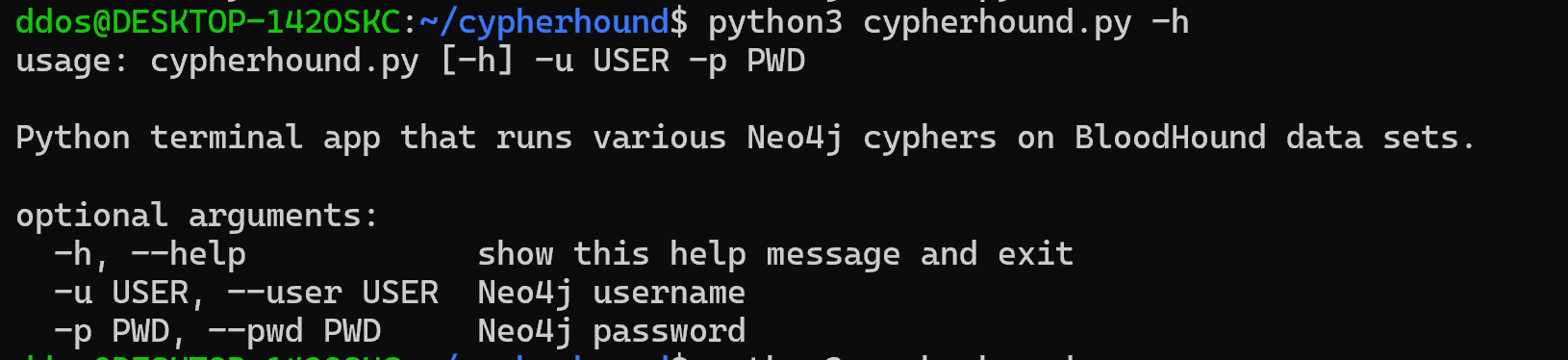
Start the program with: python3 cypherhound.py -u <neo4j_username> -p <neo4j_password>
Important Notes
- The program is configured to use the default Neo4j database and URI
- Built for BloodHound 4.2.0, certain edges will not work for previous versions
- Windows users must run pip3 install pyreadline3
- Shortest paths exports are all the same (raw or not) due to their unpredictable number of nodes
Copyright (C) 2022 Dylan Evans|fin3ss3g0d
Source: https://github.com/fin3ss3g0d/






