dvca: Damn Vulnerable Cloud Application
Damn Vulnerable Cloud Application
This is a demonstration project to show how to do privilege escalation on AWS. DO NOT deploy this on an AWS account unless you know very well what you are doing!
Prerequisites
- A domain name managed by AWS
- The ACM Certificate ID associated to this domain
- A Wildcard Certificate associated to this domain
- The Hosted Zone ID associated to this domain
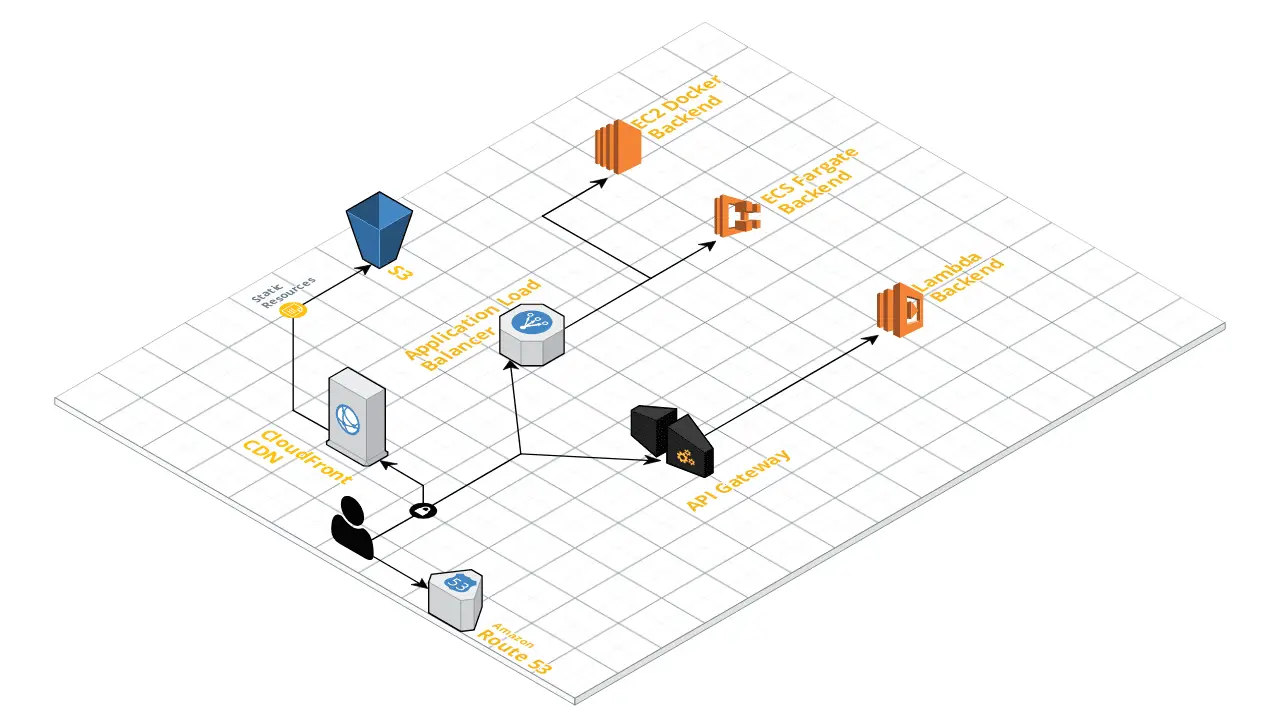
The Damn Vulnerable Cloud Application architecture
Download
git clone https://github.com/m6a-UdS/dvca.git
Deployment
In theory, you should be able to deploy the Damn Vulnerable Cloud Application with a simple command:
But the project is modular, so you could also deploy it in multiple steps. Typical make resources would be: prerequisites, frontend and a backend of your choice
Just be careful: The frontend needs your root domain Certificate ID for the CloudFront distribution, while the rest just needs your wildcard Certificate ID
In the end, you should end up with something like this 🙂
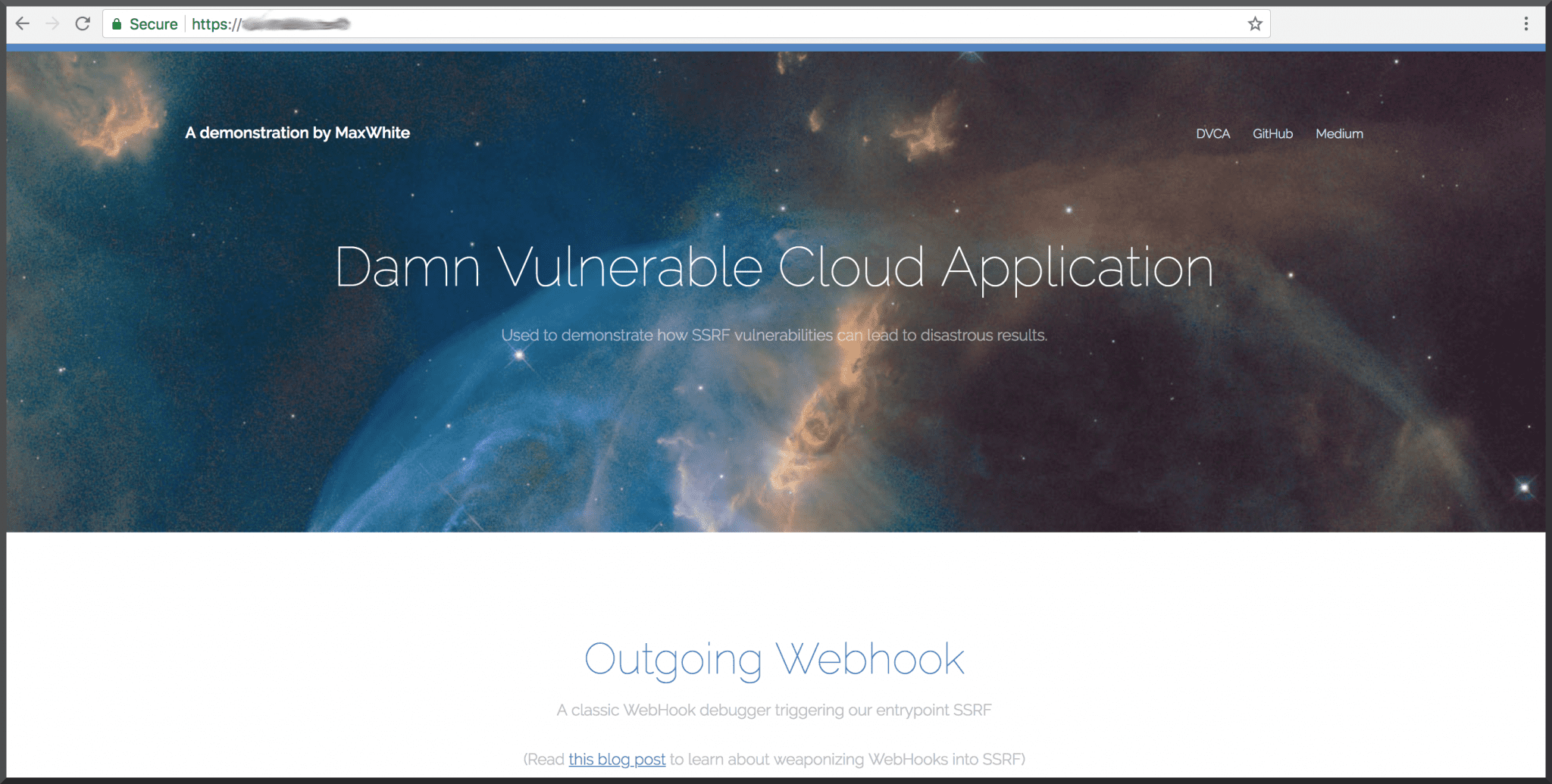
More details about how to use it are available on this blog. For now, it’s very AWS-centric, but the frontend is completely agnostic to the backend’s technology, so if you want to contribute with a backend using other Cloud providers, I gladly accept PRs.
Source: https://github.com/m6a-UdS/






