dhcpwn v1.1.0 releases: DHCP IP exhaustion attacks tool
DHCPwn is a tool used for testing DHCP IP exhaustion attacks. It can also be used to sniff local DHCP traffic.
Useful links:
Overview
The DHCP protocol is connectionless and implemented via UDP. These two characteristics allow this attack to be performed. Since there is no actual connection being made between the client and server we can quickly send many spoofed requests.
DHCP servers rely on the senders MAC address to allocate IP addresses. We can easily spoof many requests with different, fake MAC addresses. This will eventually exhaust the server’s ability to assign new IP addresses. Depending on the server’s method of releasing IP addresses associated with a given MAC address this attack will either be more, or less effective. For example, if a server quickly releases allocations that it doesn’t receive responses from, the attack will be less effective.
This attack is typically considered to be a form of DoS.
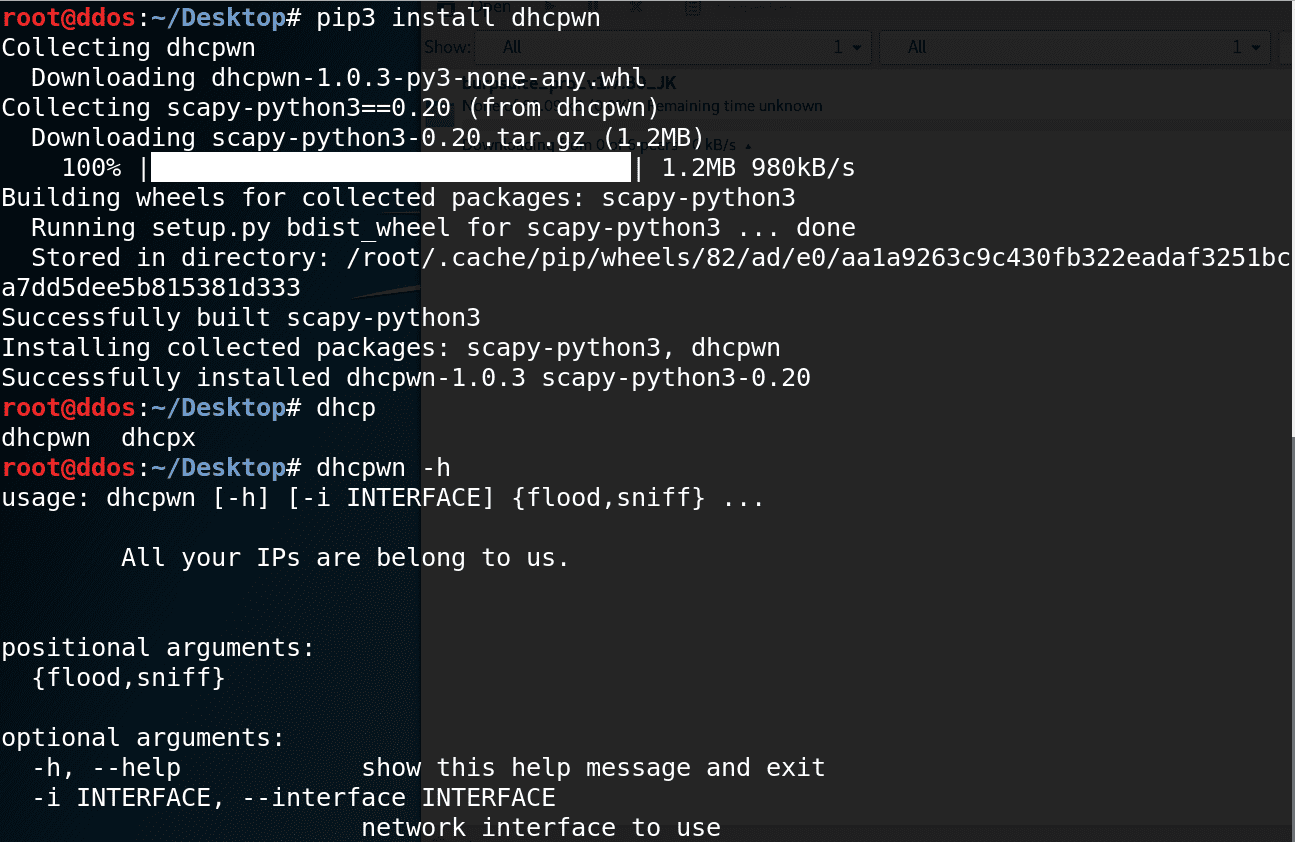
Installing
$ pip3 install dhcpwn
$ dhcpwn -h
OR
$ git clone https://github.com/mschwager/dhcpwn.git
$ cd dhcpwn
$ pip3 install -r requirements.txt
$ python3 dhcpwn.py -h
Using
Flood:
$ dhcpwn --interface wlan0 flood --count 256
Sniff:
$ dhcpwn --interface wlan0 sniff
Help:
$ dhcpwn -h
Copyright (C) 2016 mschwager
Source: https://github.com/mschwager/






