django-defender v0.9.7 releases: blocks people from brute forcing login attempts
django-defender
A simple Django reusable app that blocks people from brute forcing login attempts. The goal is to make this as fast as possible so that we do not slow down the login attempts.
We will use a cache so that it doesn’t have to hit the database in order to check the database on each login attempt. The first version will be based on Redis, but the goal is to make this configurable so that people can use whatever backend best fits their needs.
Features
-
Log all login attempts to the database
-
Support for reverse proxies with different headers for IP addresses
-
Rate limit based on
- Username
- IP address
-
Use Redis for the blacklist
-
Configuration
-
Redis server
- Host
- Port
- Database
- Password
- Key prefix
-
Block length
-
Number of incorrect attempts before block
-
-
95% code coverage
-
Full documentation
-
Ability to store login attempts to the database
-
Management command to clean up login attempts database table
-
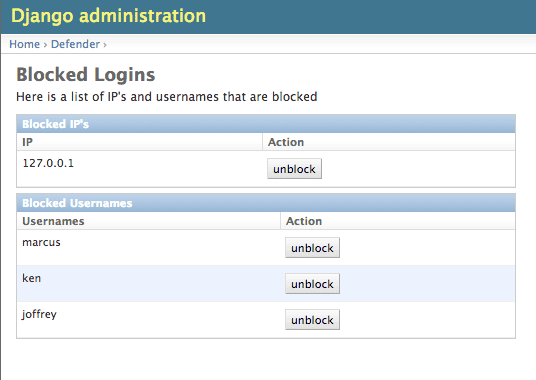
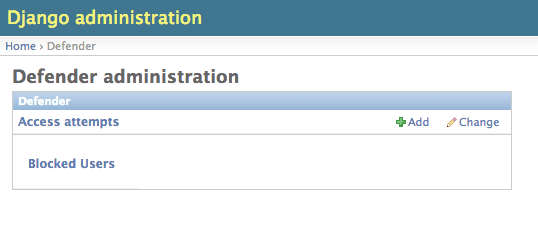
Admin pages
- List of blocked usernames and IP addresses
- List of recent login attempts
- Ability to unblock people
-
Can be easily adapted to custom authentication methods.
-
Signals are sent when blocking username or IP
How django-defender works
- When someone tries to login, we first check to see if they are currently blocked. We check the username they are trying to use, as well as the IP address. If they are blocked, goto step 5. If not blocked go to step 2.
- They are not blocked, so we check to see if the login was valid. If valid go to step 6. If not valid go to step 3.
- Login attempt wasn’t valid. Add their username and IP address for this attempt to the cache. If this brings them over the limit, add them to the blocked list, and then goto step 5. If not over the limit goto step 4.
- Login was invalid, but not over the limit. Send them back to the login screen to try again.
- User is blocked: Send them to the blocked page, telling them they are blocked, and give an estimate on when they will be unblocked.
- Login is valid. Reset any failed login attempts, and forward to their destination.
Changelog 0.9.7
- Fix bug related to using a redis version less than 6 and not having a password. [@kencochrane]
- Fix bug in remove_prefix method [@dashgin]
Install & Use
Copyright (C) 2022 jazzband