singularity: A DNS rebinding attack framework
Singularity of Origin
Singularity of Origin is a tool to perform DNS rebinding attacks. It includes the necessary components to rebind the IP address of the attack server DNS name to the target machine’s IP address and to serve attack payloads to exploit vulnerable software on the target machine.
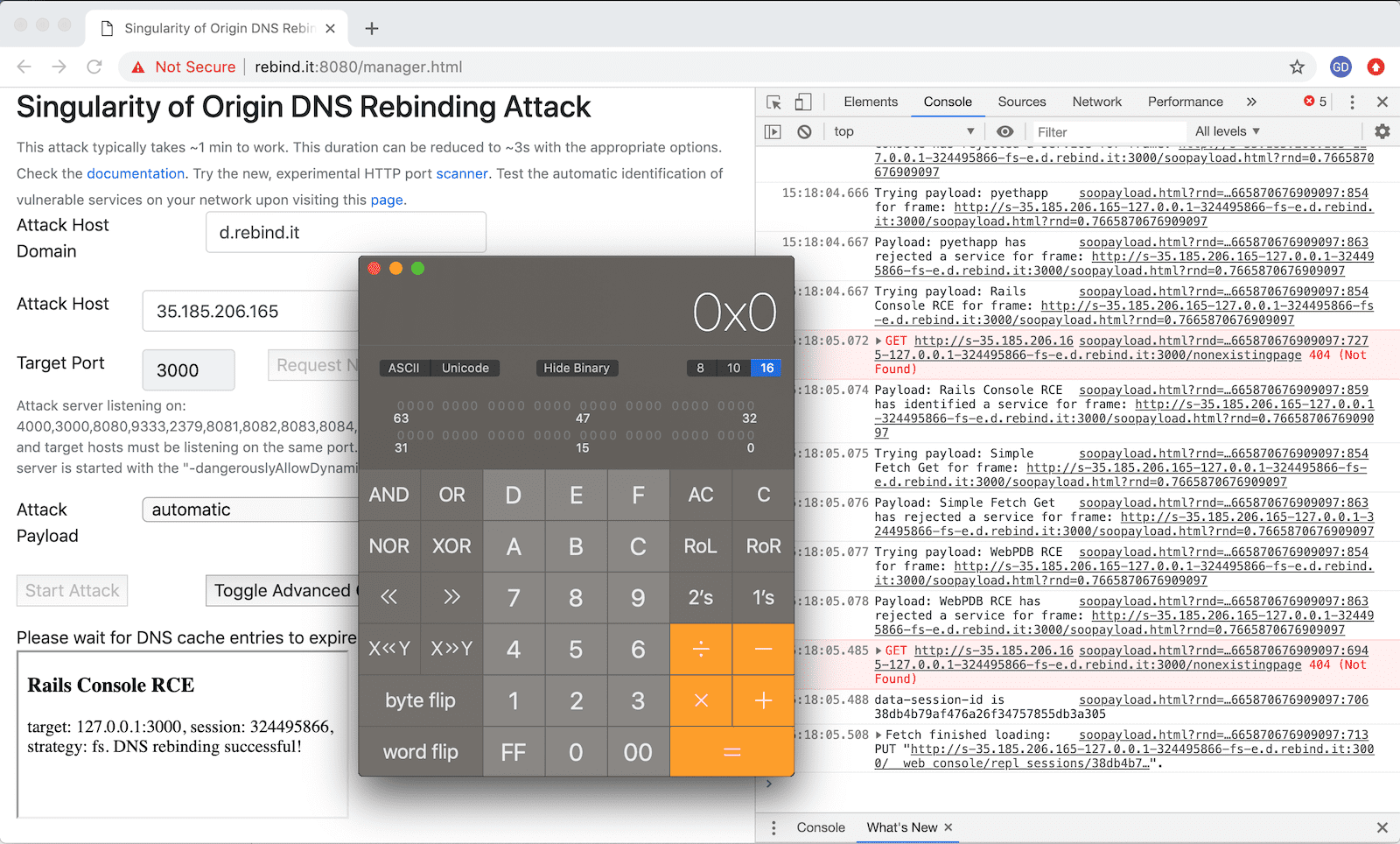
It also ships with sample payloads to exploit several vulnerable software versions, from the simple capture of a home page to performing remote code execution. It aims at providing a framework to facilitate the exploitation of software vulnerable to DNS rebinding attacks and to raise awareness on how they work and how to protect from them.
Features
- Singularity provides a complete DNS rebinding attack delivery stack:
- The custom DNS server to rebind DNS name and IP address mapping from the attacker web server address to the target machine address
- HTTP server to serve HTML pages and JavaScript code to targets and to manage the attacks
- Several sample attack payloads, ranging from grabbing the home page of a target application to performing remote code execution. These payloads can be easily adapted to perform new and custom attacks.
- Supports concurrent users.
- Provides several DNS rebinding strategies, including sequential mapping from the attacker to the target IP address and random mapping, to minimize the impact of IDS/IPS interfering with the attack.
- A number of technical controls to maximize the reliability and speed of attacks:
- Disabling HTTP keep-alive, caching, DNS prefetching
- Aggressive DNS response TTLs
- Option to use DNS CNAME instead of A records to evade several DNS filtering solutions or to target internal resources for which the IP address is unknown.
- Near-instant rebinding for several browsers and OS combinations, using multiple DNS answers and dynamic HTTP port blocking.
- Ability to allocate HTTP servers at startup or dynamically thereafter
- A convenience feature to avoid restarting Singularity to listen on a different HTTP port.
- To lay the groundwork to attack vulnerable ports discovered after a scan.
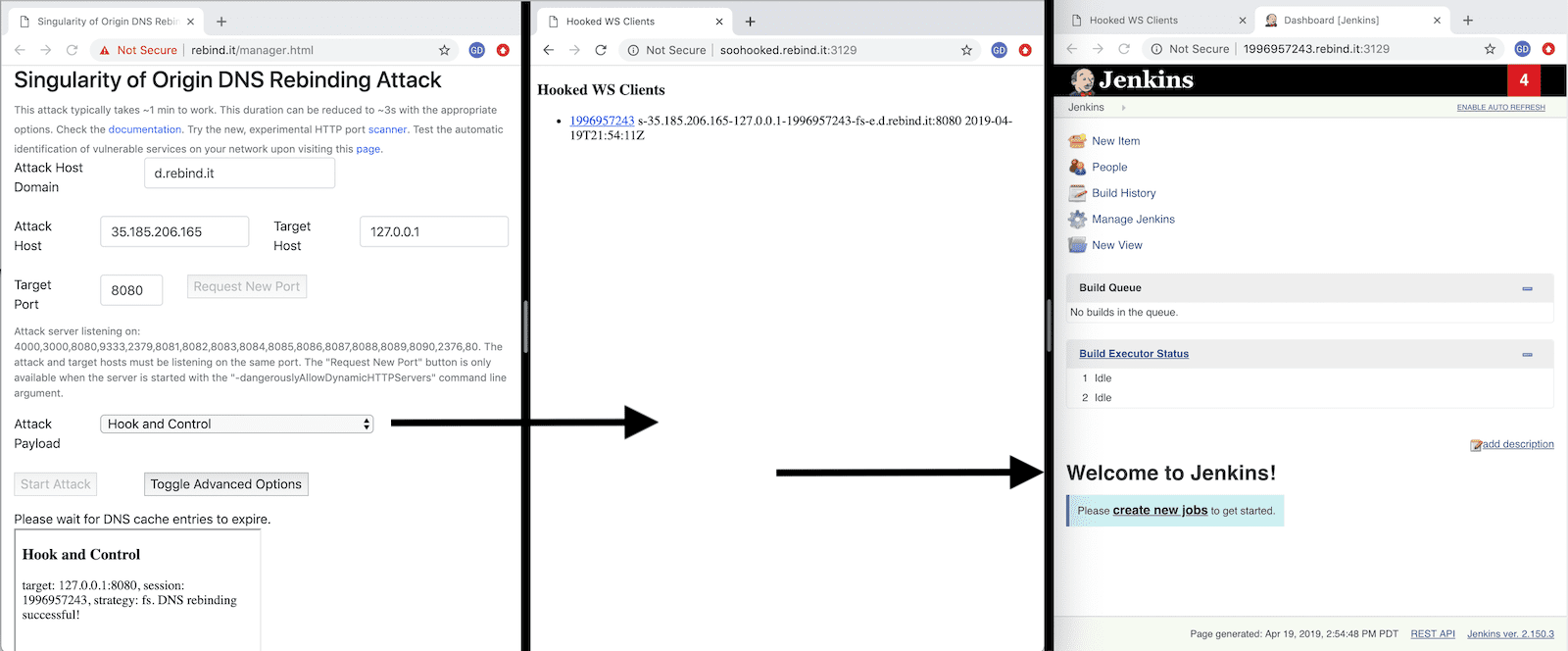
- Permits using target web browsers as HTTP proxies to internal network resources, to explore and exploit otherwise inaccessible applications with your own browser or tools such as curl.
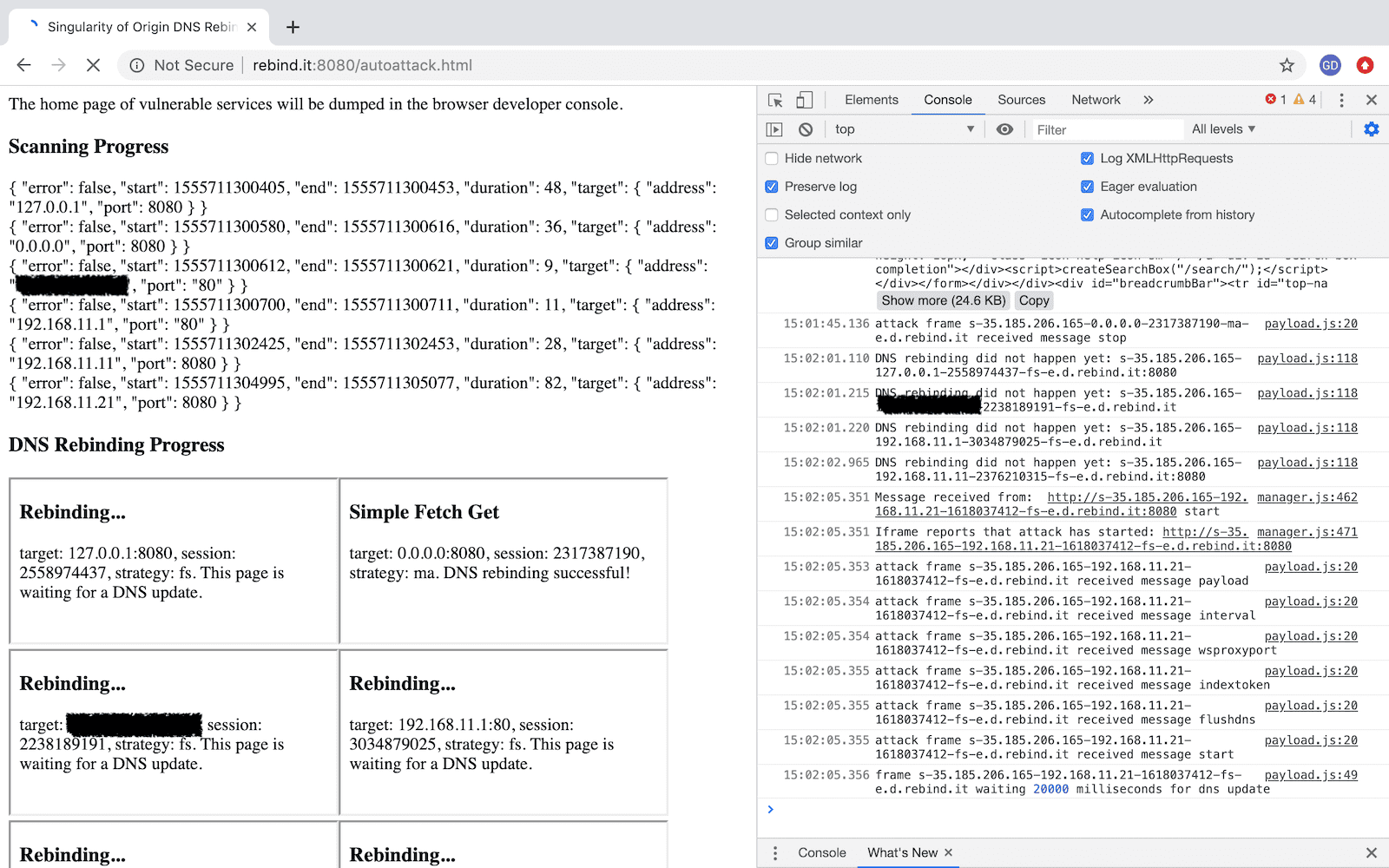
- A simple, fast and efficient HTTP port scanner to identify vulnerable services.
- Provides both user interface is driven and scripted attacks.
- Attack Automation allows to completely automate the scanning and exploitation of vulnerable services on a network.
Singularity Manager Interface
Hook and Control a Vulnerable Application on Localhost
Automate the Scan and Compromise of All Vulnerable Applications
Install && Use
Copyright (c) 2018 NCC Group Plc