FinalRecon v1.1.6 releases: OSINT Tool for All-In-One Web Reconnaissance
FinalRecon
FinalRecon is a fast and simple python script for web reconnaissance. It follows a modular structure so in the future new modules can be added with ease.
Features
FinalRecon provides detailed information such as :
FinalRecon provides detailed information such as :
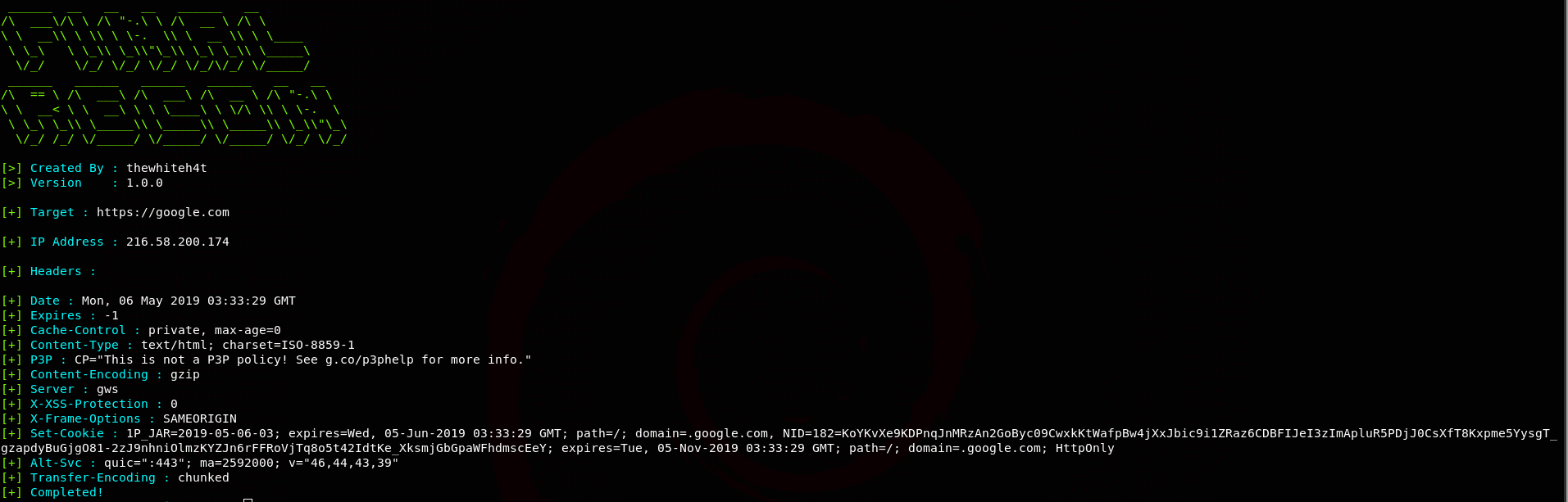
- Header Information
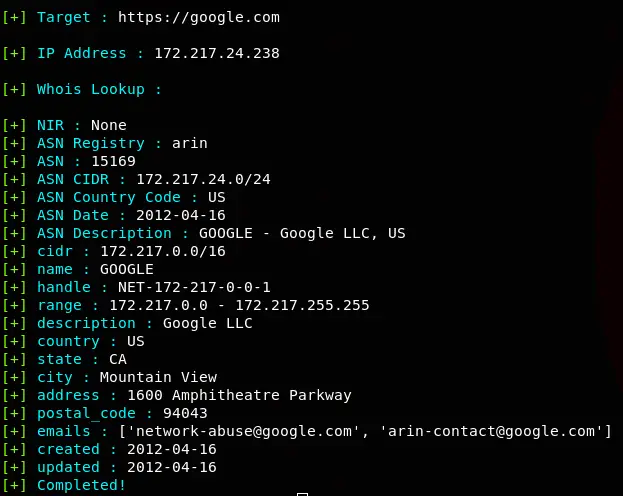
- Whois
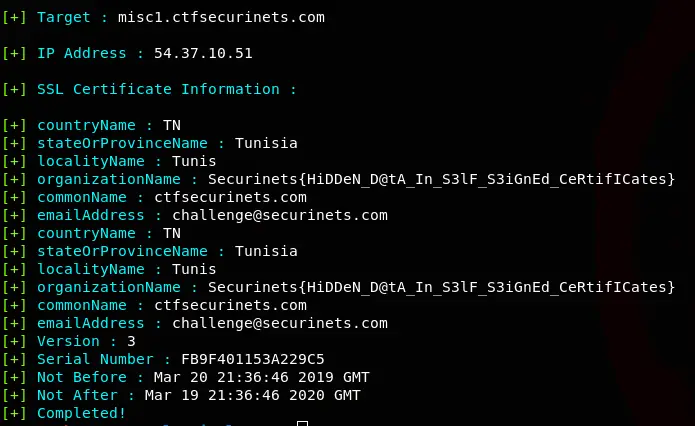
- SSL Certificate Information
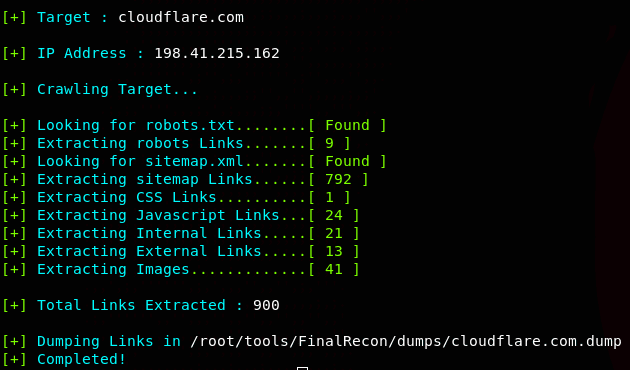
- Crawler
- DNS Enumeration
- A, AAAA, ANY, CNAME, MX, NS, SOA, TXT Records
- DMARC Records
- Subdomain Enumeration
- Data Sources
- BuffOver
- crt.sh
- ThreatCrowd
- AnubisDB
- ThreatMiner
- Data Sources
- Traceroute
- Protocols
- UDP
- TCP
- ICMP
- Protocols
- Directory Searching
- Port Scan
- Fast
- Top 1000 Ports
- Open Ports with Standard Services
- Export
- Formats
- txt
- xml
- csv
- Formats
Changelog v1.1.6
- dependencies reduced
- logger added
- adjusted for new tldextract version
- bevigil added for sub-domain enum
- refactored
- sonar sub-domain query disabled
- improved exception handling in dns enum
Installation
git clone https://github.com/thewhiteh4t/FinalRecon.git
cd FinalRecon
pip3 install -r requirements.txt
Configuration
API Keys
Some Modules Use API Keys to fetch data from different resources, these are optional, if you are not using an API key, they will be simply skipped. If you are interested in using these resources you can store your API key in keys.json file.
Path –> finalrecon/conf/keys.json
If you dont want to use a key for a certain data source just set its value to null, by default values of all available data sources are null.
Facebook Developers API
This data source is used to fetch Certificate Transparency data which is used in Subdomain Enumeration
Key Format : APP-ID|APP-SECRET
Read More: https://developers.facebook.com/docs/facebook-login/access-tokens
Usage
Copyright (c) 2019 thewhiteh4t
Source: https://github.com/thewhiteh4t/