go-shellcode: Windows Shellcode runners and supporting utilities
go-shellcode
go-shellcode is a repository of Windows Shellcode runners and supporting utilities. The applications load and execute Shellcode using various API calls or techniques.
The available Shellcode runners include:
- CreateFiber: This application leverages the Windows CreateFiber function from the Kernel32.dll to execute shellcode within this application’s process. This is usefull when you want to avoid remote process injection and want to avoid calling CreateThread. This application DOES NOT leverage functions from the golang.org/x/sys/windows package. The most significant difference is that this application loads all the necessary DLLs and Procedures itself and uses the procedure’s Call() function.
- CreateProcess: This application leverages the Windows CreateProcess function from Kernel32.dll. The process is created in a suspended state, the AddressOfEntryPoint in the IMAGE_OPTIONAL_HEADER structure is updated to execute shellcode in the childprocess, and then the process is resumed. This is a type of process hollowing but the existing PE is NOT unmapped and the ThreadContext is NOT updated. The provided shellcode architecture (i.e. x86 or x64) must match the architecture of the child process.
- CreateProcessWithPipe:This application leverages the Windows CreateProcess function from Kernel32.dll. The process is created in a suspended state, the AddressOfEntryPoint in the IMAGE_OPTIONAL_HEADER structure is updated to execute shellcode in the childprocess, and then the process is resumed. This is a type of process hollowing but the existing PE is NOT unmapped and the ThreadContext is NOT updated. The provided shellcode architecture (i.e. x86 or x64) must match the architecture of the child process.This application differs from CreateProcess because it will collect any data written to STDOUT or STDERR in the child process and return it to the parent process. Data is collected by using the CreatePipe function to create an anonymous pipe that the parent and child process communicate over. This is usefull when using tools like Donut to execute a .NET assembly in a child process as shellcode and to retrieve the output of the executed program.
- CreateRemoteThread: This application leverages the Windows CreateRemoteThread function from Kernel32.dll to execute shellcode in a remote process. The application requires that the target process to inject into is already running. The targe Process Identifier (PID) can be provided at runtime for testing using the -pid command line flag.
- CreateRemoteThreadNative: This application leverages the Windows CreateRemoteThread function from Kernel32.dll to execute shellcode in a remote process. The application requires that the target process to inject into is already running. The targe Process Identifier (PID) can be provided at runtime for testing using the -pid command line flag.
- CreateThread: This application leverages the Windows CreateThread function from Kernel32.dll to execute shellcode within this application’s process. This is usefull when you want to avoid remote process injection. This application leverages functions from the golang.org/x/sys/windows package, where feasible, like the windows.VirtualAlloc()`.
- CreateThreadNative: This application leverages the Windows CreateThread function from the Kernel32.dll to execute shellcode within this application’s process. This is usefull when you want to avoid remote process injection. This application DOES NOT leverage functions from the golang.org/x/sys/windows package. The most significant difference is that this application loads all the necessary DLLs and Procedures itself and uses the procedure’s Call() function.
- EarlyBird: The application leverages the Windows CreateProcess function to create a process in a suspended state. Once the child process is suspended, the Windows QueueUserAPC function is used to add a UserAPC to the child process that points to the allocated shellcode. Next, ResumeThread is called, which subsequently calls the undocumented NtTestAlert function that will execute the created UserAPC and in turn the shellcode. This is usefull because the shellcode will execute before AV/EDR can hook functions to support detection.
- EtwpCreateEtwThread: This application leverages the Windows EtwpCreateEtwThread function from ntdll.dll to execute shellcode within this application’s process. Original work by TheWover. This is usefull when you want to avoid remote process injection. This application DOES NOT leverage functions from the golang.org/x/sys/windows package. The most significant difference is that this application loads all the necessary DLLs and Procedures itself and uses the procedure’s Call() function.
- RtlCreateUserThread: This application leverages the Windows RtlCreateUserThread function from ntdll.dll to execute shellcode in a remote process. The application requires that the target process to inject into is already running. The targe Process Identifier (PID) can be provided at runtime for testing using the -pid command line flag.
- Syscall: This application executes Shellcode in the current running process by making a Syscall on the Shellcode’s entry point. This application DOES NOT leverage functions from the golang.org/x/sys/windows package.
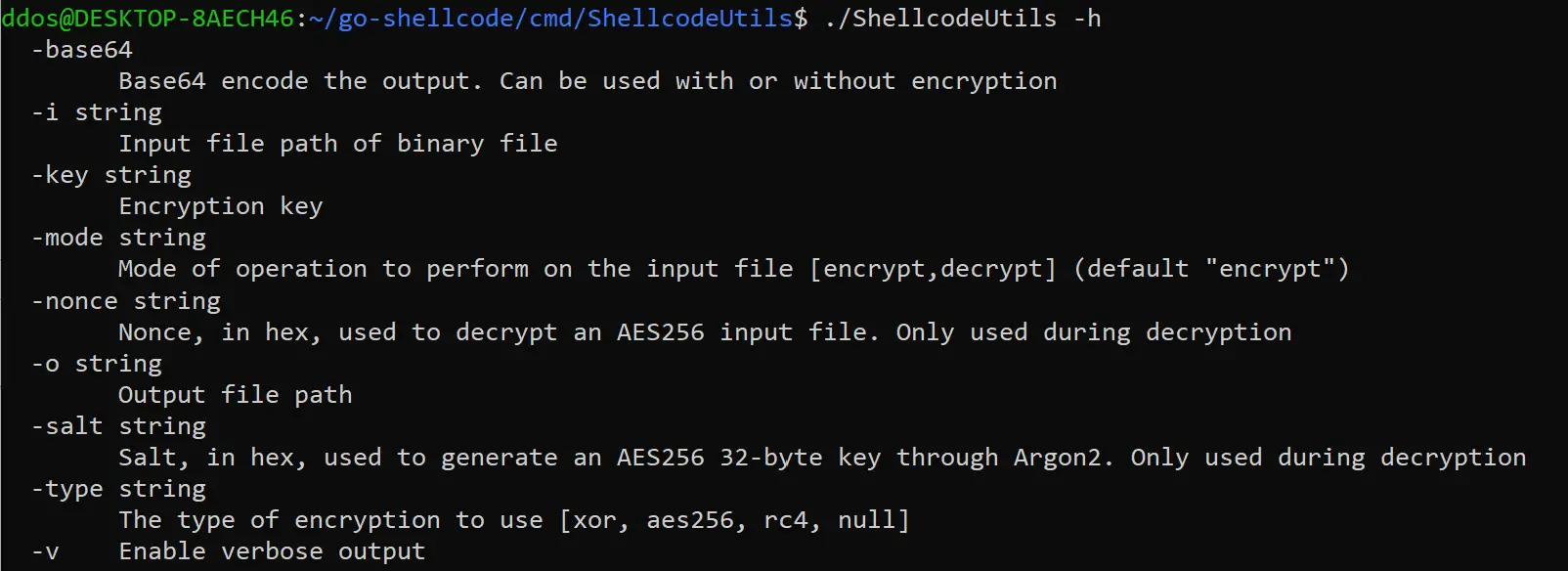
- Shellcode Utils: This application leverages the Windows UuidFromStringA function to load shellcode to a memory address and then calls the EnumSystemLocalesA function to execute the shellcode. This method of loading and executing shellcode was derived from nccgroup’s RIFT: Analysing a Lazarus Shellcode Execution Method. For this application, memory is allocated on the heap and it does not use VirtualAlloc.
- UuidFromStringA: This application is used to transform shellcode binary files. The program depends that the input file is a binary file (.bin) that contains the hex bytes of the shellcode. ShellcodeUtils can just base64 encode your input file or it can XOR, RC4, or AES256-GCM encrypt it. The tools can also be used to decrypt files as well.
Download
Copyright (C) 2021 Ne0nd0g