harpoon: open source and threat intelligence
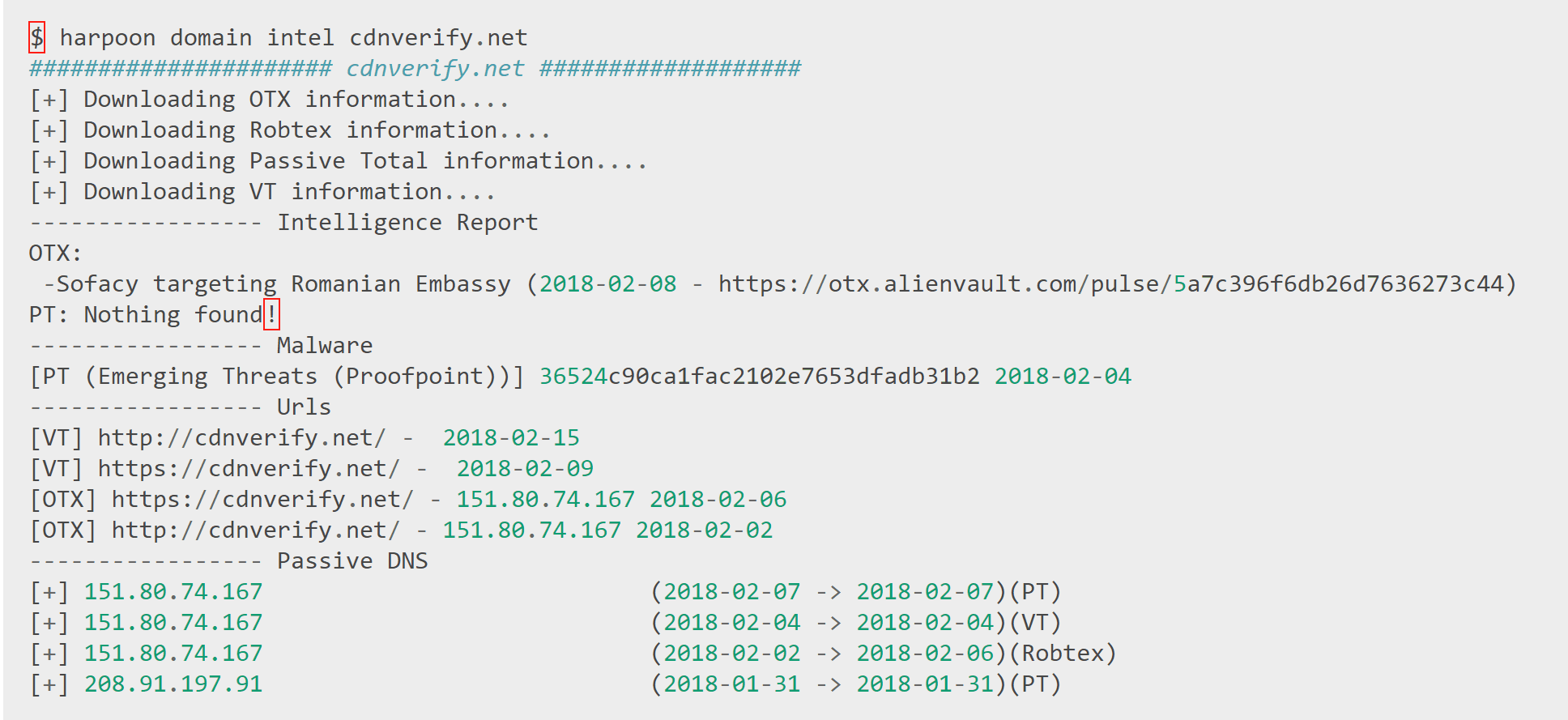
Harpoon is a tool to automate threat intelligence and open source intelligence tasks. It is written in Python 3 and organized in plugins so the idea is to have one plugin per platform or task.
Some notes on the principles behind this tool :
- Python 3 only, python 2 is dead, I am not even trying to support it
- Many OSINT tools try to gather as much information as possible from an indicator (domain or email) without really any interest in where it comes from. Harpoon does not follow this philosophy. It mostly allows you to realize a single task per command (with a couple of more general commmands using several tools). I think it is really important during an investigation to understand where an information comes from and how reliable it is.
- In many cases, I also wanted to explore APIs to see what was possible with them, and I ended up rewriting some libraries (like SpyOnWeb) just because I wanted to understand exactly what it did and how. So I reinvented the wheel many times and I am totally fine with it.
- Harpoon is organized into subcommands that are easy to implement, these commands rely on internal or external libraries. These commands also use a single configuration file that you need to complete manually when an API key is needed.
- This tool is not perfect, it only does what I needed to automate, it is likely buggy and has a long list of things I would like to implement one day (but it may never happen). Feel free to open issues or propose Pull Requests.
Install
To configure harpoon, run harpoon config and fill in the needed API keys. Then run harpoon config -u to download needed files. Check what plugins are configured with harpoon config -c.
Usage
Tutorial
Copyright (C) 2018 Te-k
Source: https://github.com/Te-k/






