htcap: web application scanner
HTCAP
Htcap is a web application scanner able to crawl single page application (SPA) in a recursive manner by intercepting ajax calls and DOM changes.
Htcap is not just another vulnerability scanner since it’s focused mainly on the crawling process and uses external tools to discover vulnerabilities. It’s designed to be a tool for both manual and automated penetration test of modern web applications.
This is the very first release that uses headless chrome instead of phantomjs. Htcap’s Javascript crawling engine has been rewritten to take advantage of the new async/await features of ECMAScript and has been converted to a nodjes module build on top of Puppetteer.
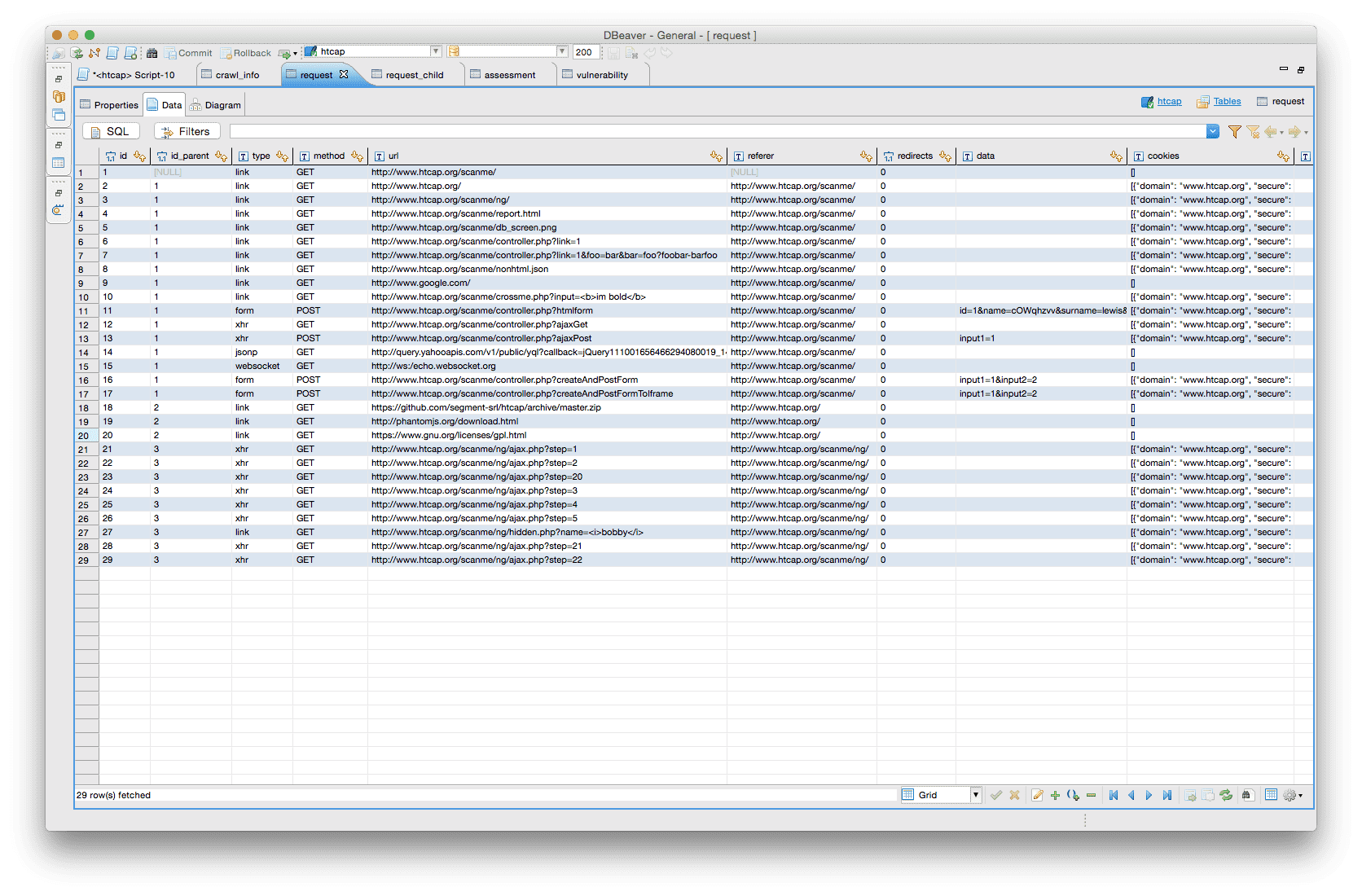
The scan process is divided into two parts, the first htcap crawls the target and collects as many requests as possible (urls, forms, ajax ecc..) and saves them to an sql-lite database. When the crawling is done it is possible to launch several security scanners against the saved requests and save the scan results to the same database.
When the database is populated (at least with crawling data), it’s possible to explore it with ready-available tools such as sqlite3 or DBEaver or export the results in various formats using the built-in utilities.
SETUP
Requirements
- Python 2.7
- PhantomJS v2
- Sqlmap (for sqlmap scanner module)
- Arachni (for arachni scanner module)
Download and Run
PhantomJs can be downloaded here. It comes as a self-contained executable with all libraries linked statically, so there is no need to install or compile anything else.
DOCUMENTATION
Documentation, examples, and demos can be found at the official website http://htcap.org.
Copyright (C) 2017
Source: https://github.com/segment-srl/






