InQL Scanner v5.02 releases: Burp Extension for GraphQL Security Testing
InQL Scanner
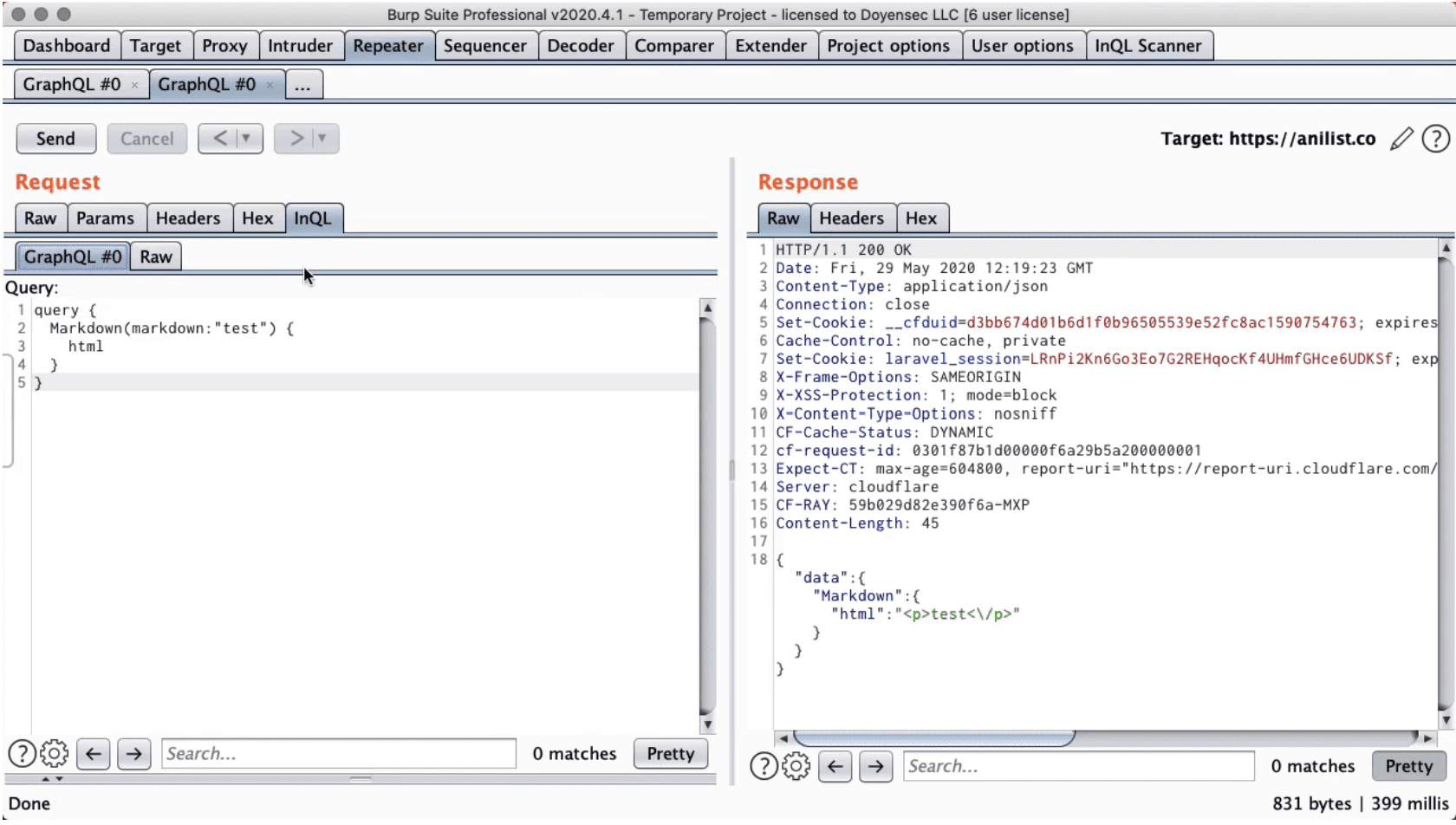
InQL Scanner is a security testing tool to facilitate GraphQL technology security auditing efforts. InQL can be used as a stand-alone script or as a Burp Suite extension.
Changelog v5.02
A minor release to fix two bugs:
- InQL duplicating headers in an unrelated traffic
- Burp’s internal headers added during ‘Generate queries with InQL Scanner’ menu action (only from GraphQL editor tab)
Refer to v.5.0.0 release notes for the list of major changes since v4.
Download
git clone https://github.com/doyensec/inql.git
Use
InQL Stand-Alone CLI
Running inql from Python will issue an Introspection query to the target GraphQL endpoint in order to fetch metadata information for:
- Queries, mutations, subscriptions
- Its fields and arguments
- Objects and custom object types
- Cycles inside the graphql definition
InQL can inspect the introspection query results and generate clean documentation in different formats such as HTML and JSON schema. InQL is also able to generate templates (with optional placeholders) for all known basic data types.
InQL Burp Suite Extension
To use inql in Burp Suite, import the Python extension:
- Download the Jython Jar
- Start Burp Suite
- Extender Tab > Options > Python Enviroment > Set the location of Jython standalone JAR
- Extender Tab > Extension > Add > Extension Type > Select Python
- Download the latest inql_burp.py release here
- Extension File > Set the location of inql_burp.py > Next
- The output should now show the following message: InQL Scanner Started!
In this mode, the tool will retain all the stand-alone script capabilities and add a handy user interface for manipulating queries.
Using the inql extension for Burp Suite, you can:
- Search for known GraphQL URL paths; the tool will grep and match known values to detect GraphQL endpoints within the target website
- Search for exposed GraphQL development consoles (GraphiQL, GraphQL Playground, and other standard consoles)
- Use a custom GraphQL tab displayed on each HTTP request/response containing GraphQL
- Leverage the templates generation by sending those requests to Burp’s Repeater tool (“Send to Repeater”)
- Leverage the templates generation and editor support by sending those requests to embedded GraphIQL (“Send to GraphiQL”)
- Configure the tool by using a custom settings tab
Copyright 2020 Doyensec LLC.