jackdaw v0.3.1 releases: collect all information in your domain
jackdaw
Jackdaw is here to collect all information in your domain, store it in a SQL database and show you nice graphs on how your domain objects interact with each-other a how a potential attacker may exploit these interactions. It also comes with a handy feature to help you in a password-cracking project by storing/looking up/reporting hashes/passwords/users.
Features
Data acquisition
via LDAP
LDAP enumeration phase acquires data on AD info, User, Machine, OU, Group objects which will be represented as a node in the graph, and as a separate table in the DB. Additionally, all aforementioned objects’ Security Description will be parsed and the ACLs for the DACL added to the DB. This, together with the membership information will be represented as edges in the graph. Additionally, custom SQL queries can be performed on any of the aforementioned data types when needed.
via SMB
SMB enumeration phase acquires data on shares, localgroups, sessions, NTLM data via connecting to each machine in the domain (which is acquired via LDAP)
via LSASS dumps (optional)
The framework allows users to upload LSASS memory dumps to store credentials and extend the session information table. Both will be used as additional edges in the graph (shared password and session respectively). The framework also uses this information to create a password report on weak/shared/cracked credentials.
via DCSYNC results (optional)
The framework allows users to upload impacket’s DCSYNC files to store credentials. This is used as additional edges in the graph (shared password). The framework also uses this information to create a password report on weak/shared/cracked credentials.
via manual upload (optional)
The framework allows manually extending the available DB in every aspect. Example: when user-session information on a given computer is discovered (outside of the automatic enumeration) there is a possibility to manually upload these sessions, which will populate the DB and also the resulting graph
Graph
The framework can generate a graph using the available information in the database and plot it via the web UI (nest). Furthermore, the graph generation and path calculations can be invoked programmatically, either by using the web API (/ui endpoint) or the graph object’s functions.
Anomalies detection
The framework can identify common AD misconfigurations without graph generation. Currently only via the web API.
User
User anomalies detection involves the detection of insecure UAC permissions and extensive user description values. This feature set is expected to grow in the future as new features will be implemented.
Machine
Machine anomalies detection involves detection of insecure UAC permissions, non-mandatory SMB singing, outdated OS version, out-of-domain machines. This feature set is expected to grow in the future as new features will be implemented.
Password cracking
The framework is not performing any cracking, only organizing the hashes and the cracking results
currently main focus is on impacket and aiosmb’s dcsync results !NT and LM hashes only!
Sample process is the following:
- Harvesting credentials as a text file via impacket/aiosmb or as memory dumps of the LSASS process via whatever tool you see fit.
- Upload the harvested credentials via the API
- Poll uncracked hashes via the API
- Crack them (hashcat?)
- Upload the results to the framework via the API
- Generate a report on the cracked/uncracked users and password strength and password sharing
note from the author: This feature was implemented for both attackers and defenders. Personally, I don’t see much-added value on either side since at the point one obtained the NT hash of a user it’s just as good as the password… Nonetheless, more and more companies are performing password strength exercises, and this feature would help them. As for attackers: it is just showing off at this point, but be my guest. Maybe scare management for extra points.
Changelog v0.3.1
- Cleaning up the codebase. Some fixes in the UI and minor speedup in path calculation.
Download
git clone https://github.com/skelsec/jackdaw
cd jackdaw
python setup.py install
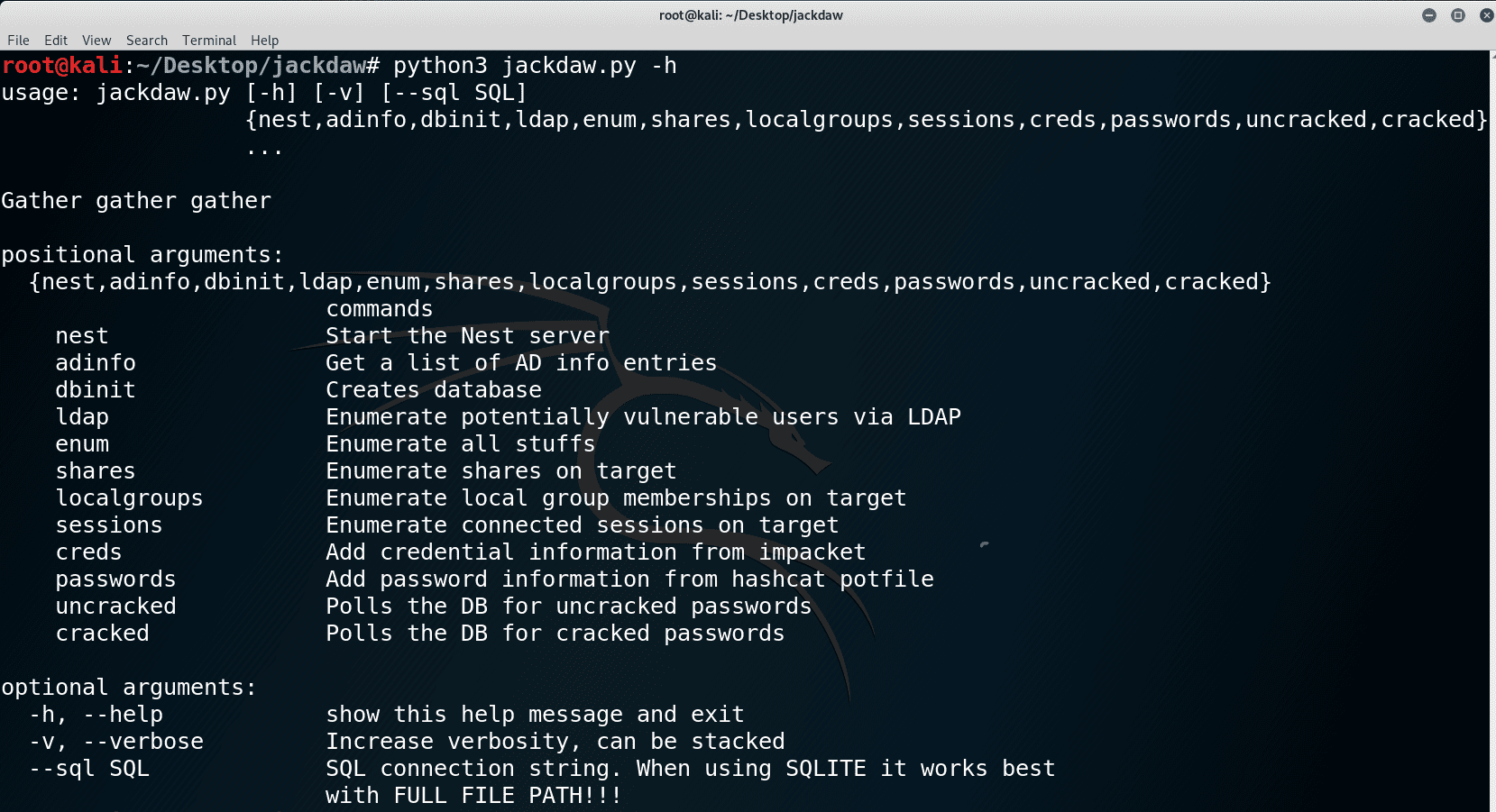
Use
Example
Most of these commands are available already from the webapi, except for the database init.
DB init
jackdaw –sql sqlite:///<full path here>/test.db dbinit
Enumeration
Full enumeration with integrated sspi – windows only
jackdaw –sql sqlite:///test.db enum ‘ldap+sspi://10.10.10.2’ ‘smb+sspi-ntlm://10.10.10.2’
Full enumeration with username and password – platform-independent
The password is Passw0rd!
jackdaw –sql sqlite:///test.db ldap ‘ldap://TEST\victim:Passw0rd!@10.10.10.2’ ‘smb+ntlm-password://TEST\victim:Passw0rd!@10.10.10.2’
LDAP-only enumeration with username and password – platform-independent
The password is Passw0rd!
jackdaw –sql sqlite:///test.db ldap ‘ldap://TEST\victim:Passw0rd!@10.10.10.2’
Start an interactive web interface to plot graph and access additional features
jackdaw –sql sqlite:///<FULL PATH TO DB> nest
Open http://127.0.0.1:5000/ui for the API
Open http://127.0.0.1:5000/nest for the graph interface (shows the graph, but far from working)
Source: https://github.com/skelsec/