Kardon Loader Malware for $50 allows customers to build their botnets
Netscout Arbor’s security researchers recently discovered in the underground forum that a piece of malware called “Kardon Loader” is being sold at a low price of $50. Advertising claims that this is just a public beta, but its functionality is enough to make the purchase. And a buyer can build their botnets.
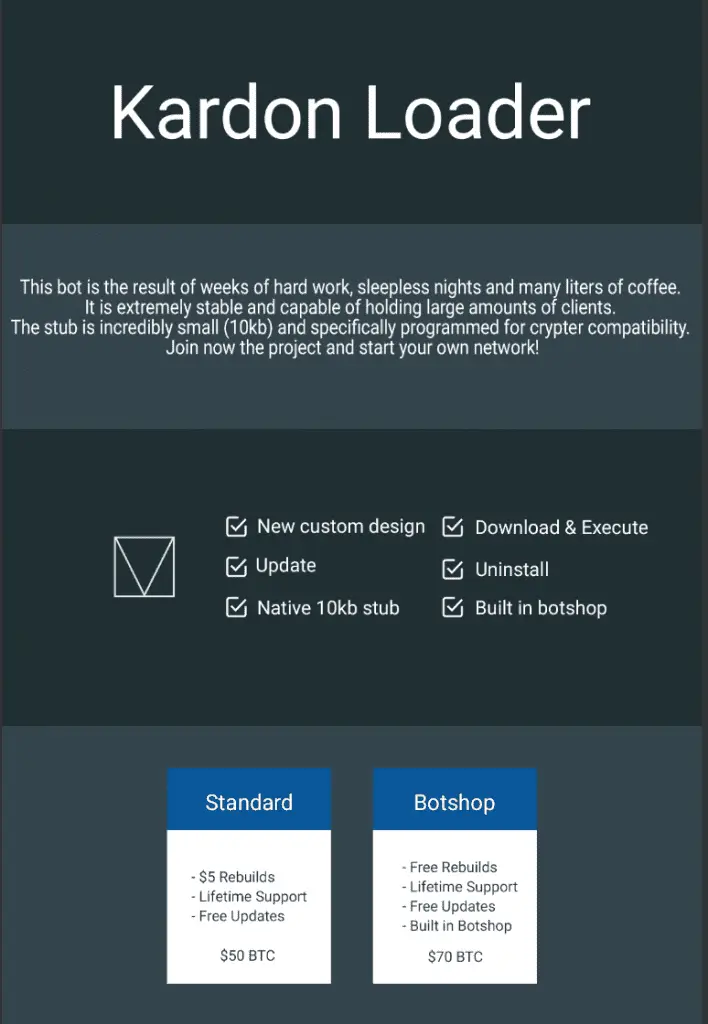
Image: arbornetworks
Researchers said that Kardon Loader is essentially a malware downloader and was sold by underground forum users code-named “Yattaze” at the end of April this year. It not only allows buyers to build their botnets but also will enable buyers to create their operating networks to expand their customer base further.
In promotional ads, Kardon Loader was described as being renamed from the ZeroCool botnet, and the creator also uploaded a YouTube video showing the features of the admin panel.
Interestingly, there is a statement attached to the advertisement saying that the software should not use for malicious purposes. Also, comments in the ad also indicate that this malware is not currently widely distributed. According to the test screenshots, only 124 devices were infected.
The ad claims that Kardon Loader provides the following features:
- Bot Functionality
- Download and Execute Task
- Update Task
- Uninstall Task
- Usermode Rootkit
- RC4 Encryption (Not Yet Implemented)
- Debug and Analysis Protection
- TOR Support
- Domain Generation Algorithm (DGA)
However, security researchers at Netscout Arbor stated that they do not have so many features in the samples they get. All examples use hard-coded Command and Control (C&C) URLs instead of DGA. There is also no TOR support or user mode Rootkit functionality in the binary file.
Although Kardon Loader is still in the early stages of development, the open beta phase, it has indeed achieved some functional capabilities, such as allowing buyers to build their botnets and establish their operational networks.
Overall, Kardon Loader should still be considered a multi-functional malware downloader. Such malware is often used by cybercriminals to create botnets to distribute other types of malware, such as credential theft software, ransomware, bank Trojans, and so on.






