KeeFarce Reborn: exports databases in cleartext once injected in the KeePass process
KeeFarce Reborn
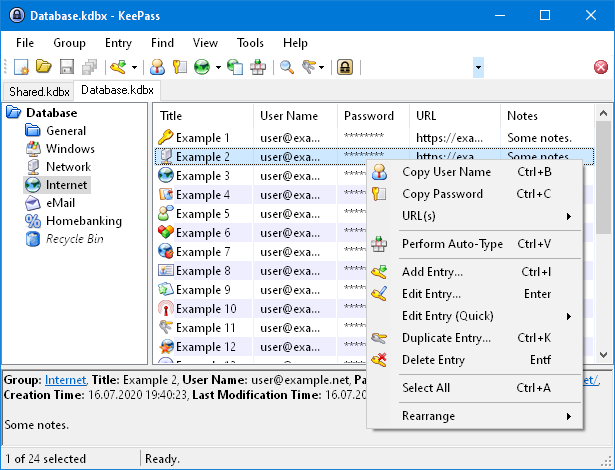
A standalone DLL that exports databases in cleartext once injected in the KeePass process.
Yet another KeePass extraction tool, why?
A few years ago, @denandz released KeeFarce, the first offensive tool designed to extract KeePass databases in cleartext. It works by injecting a DLL into the running process, then walks the heap using ClrMD to find the necessary objects and invoke KeePass’s builtin export method using reflection. Its only downside at the time was that multiple files needed to be dropped on the target (the extraction DLL + ClrMD DLL + the injector + a bootstrap DLL).
A year later, @tifkin_ and @harmj0y released an in-depth review of offensive techniques targeting KeePass (while not available on harmj0y’s blog anymore, the articles can be found on Wayback Machine: part 1, part 2). It resulted in the release of KeeThief, a tool able to decrypt KeePass’ masterkey (including when alternative authentication methods are used). It worked so well that KeePass developers added a parameter to mitigate this technique (it can be disabled by editing the KeePass configuration file if the user has enough rights, which is pretty common).
These tools quickly became my go-to during penetration testing, but they soon became obsolete as their injection techniques (namely, the famous Win32 APIs gang of VirtualAllocEx, WriteProcessMemory, CreateRemoteThread, WriteProcessMemory, etc) now immediately triggers the detection. @snovvcrash addressed this issue by forking KeeThief (now in a private repo, but still accessible here) to improve the injection mechanism with D/Invoke, writing a great article detailing the process he followed. As this demonstrated the feasibility of maintaining KeeThief, I find it difficult to implement with other injection techniques, as KeeThief’s code is tightly linked to its injector.
@holly-cracker also released KeePassHax, which comes as a single DLL and only uses reflection to decrypt KeePass’ masterkey. Inspired by this work, I decided to do the same with KeeFarce and write my own KeePass extraction tool with the following features:
- Self-sufficient ⇒ no interaction is needed with the injector’s code to work.
- Only uses built-in .NET libraries (in particular, no ClrMD) ⇒ better compatibility + single-file to make the injection easier.
- Exports the database ⇒ same as KeeFarce, no need to retrieve the .kdbx nor use a custom KeePass built to input the recovered masterkey.
Install & Use
Copyright (c) 2022, Julien Bedel
All rights reserved.






