Laika BOSS: Object Scanning System
Laika boss is an object scanner and intrusion detection system that strives to achieve the following goals:
- Scalable
- Work across multiple systems
- High volume of input from many sources
- Flexible
- Modular architecture
- Highly configurable dispatching and dispositioning logic
- Tactical code insertion (without needing restart)
- Verbose
- Generate more metadata than you know what to do with
Each scan does three main actions on each object:
- Extract child objects Some objects are archives, some are wrappers, and others are obfuscators. Whatever the case may be, find children objects that should be scanned recursively by extracting them out.
- Mark flags Flags provide a means for dispositioning objects and for pivoting on future analysis.
- Add metadata Discover as much information describing the object for future analysis.
Feel free to read the whitepaper!
Components
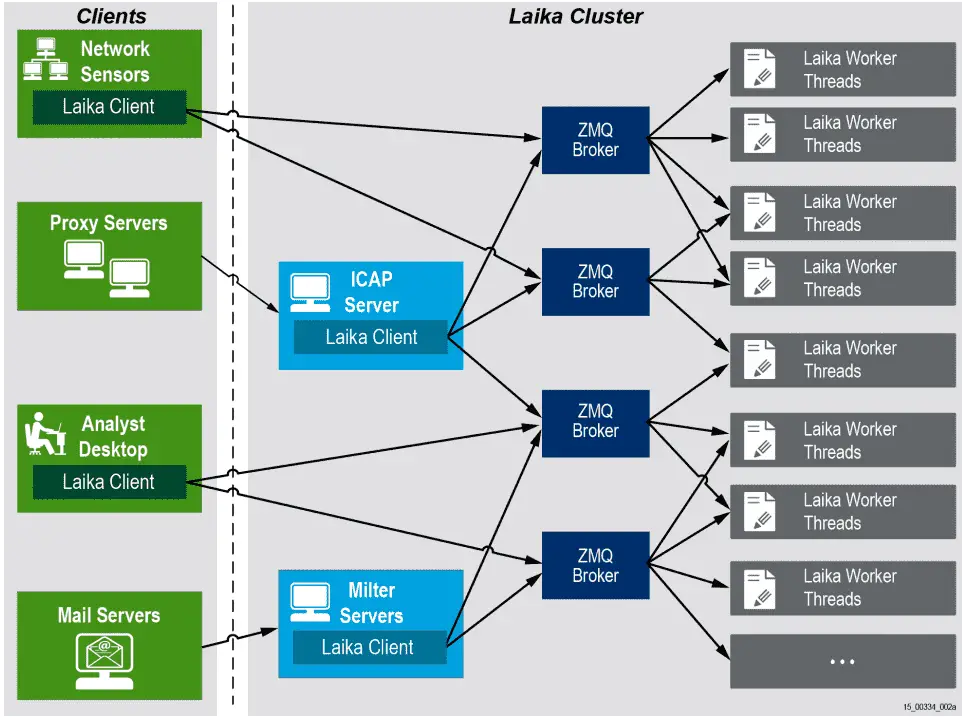
Laika is composed of the following pieces:
- Framework (laika.py) This is the core of Laika BOSS. It includes the object model and the dispatching logic.
- laikad This piece contains the code for running Laika as a daemonized, networked service using the ZeroMQ broker.
- cloudscan A command-line client for sending a local system file to a running service instance of Laika (laikad).
- modules The scan itself is composed of the running of modules. Each module is its own program that focuses on a particular sub-component of the overall file analysis.
Getting Started
Laika BOSS has been tested on the latest versions of CentOS and Ubuntu LTS
Installing on Ubuntu
- Install framework dependencies:
- Install network client and server dependencies:
- Install module dependencies:
- Clone the repo
Milter
The Laika BOSS milter server allows you to integrate Laika BOSS with mail transfer agents such as Sendmail or Postfix. This enables better visibility (passive visibility can be hampered by TLS) and provides a means to block email according to Laika BOSS disposition.
The Laika BOSS milter server requires the python-milter module and the Laika BOSS client library. Check out the comments in the source code for more details.
Suricata Integration Prototype
We have released a proof of concept feature for Suricata that allows it to store extracted files and their associated metadata in a Redis database. You will find this code under a new branch in our Suricata fork. We hope to refine the implementation and eventually have it accepted by the project.
Once you’ve enabled file extraction and the optional Redis integration in Suricata, you can extract these files from Redis and submit them to Laika BOSS for scanning by using the middleware script laika_redis_client.py as shown below. Note that it requires the python-redis module.
First, start laikad.py in async mode:
Then launch the middleware script and give it the address of the laikad broker and Redis database (defaults shown below):
Note that you will need to use a logging module such as LOG_FLUENT to export the full scan result of these file scans from laikad.
Copyright 2015 Lockheed Martin Corporation
Source: https://github.com/lmco/






