LazyRecon: automated approach to performing recon for bug bounty hunting
LazyRecon
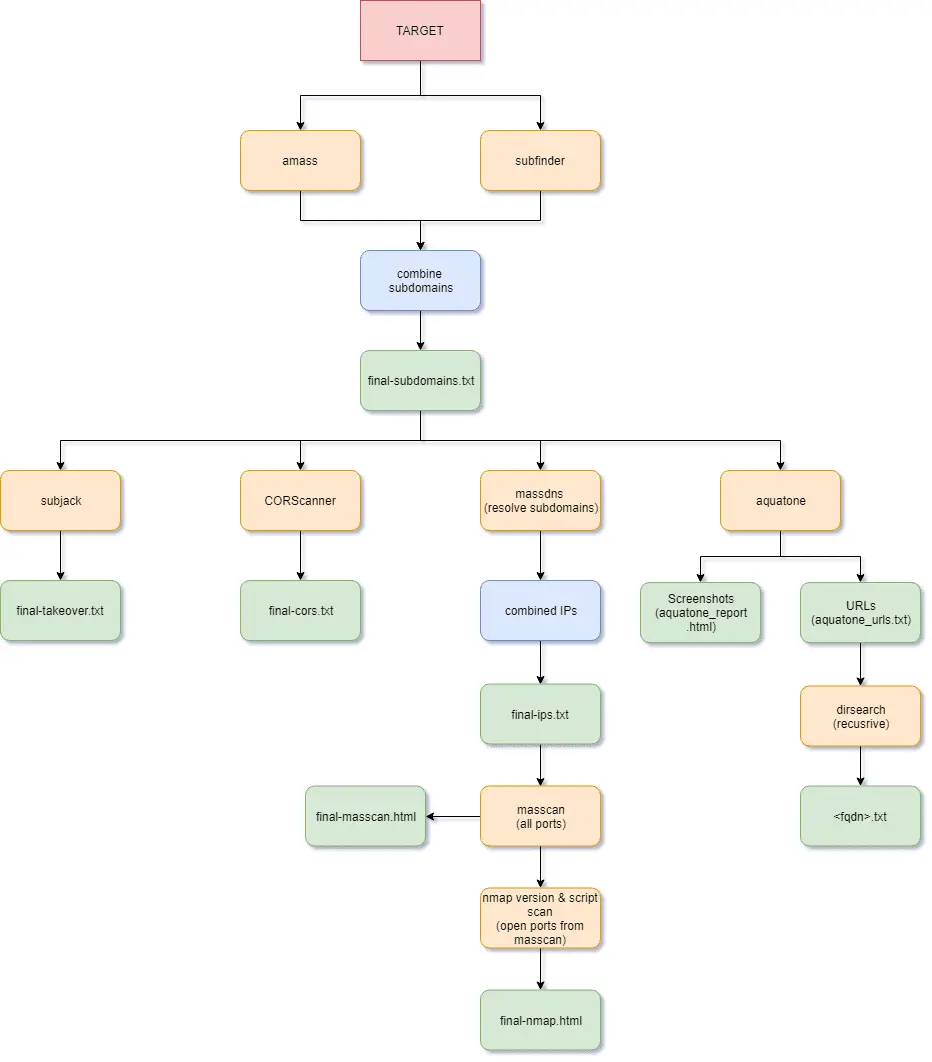
LazyRecon is a wrapper of various scripts that automates the tedious and redundant process of reconnaissance of a target domain.
LazyRecon utilizes the following tools:
- Subdomain Enumeration:
- Subdomain Takeover:
- CORS Configuration:
- IP Discovery:
- Port Scanning:
- Visual Recon:
- Content Discovery:
- Wordlists:
Workflow
Installation
First, run the following commands to install the latest version of Go.
git clone https://github.com/capt-meelo/LazyRecon.git cd LazyRecon source get-go.sh
Then, modify the subEnumTools() function of install.sh by placing your Virustotal, Passivetotal, SecurityTrails, Censys, Riddler, and Shodan API keys. This will give better results during the subdomain enumeration.
~/go/bin/subfinder --set-config VirustotalAPIKey=<API-KEY-HERE> ~/go/bin/subfinder --set-config PassivetotalUsername=<API-KEY-HERE>,PassivetotalKey=<API-KEY-HERE> ~/go/bin/subfinder --set-config SecurityTrailsKey=<API-KEY-HERE> ~/go/bin/subfinder --set-config RiddlerEmail=<API-KEY-HERE>,RiddlerPassword=<API-KEY-HERE> ~/go/bin/subfinder --set-config CensysUsername=<API-KEY-HERE>,CensysSecret=<API-KEY-HERE> ~/go/bin/subfinder --set-config ShodanAPIKey=<API-KEY-HERE>
Finally, run the following to install the required tools.
chmod +x install.sh ./install.sh
How to Use
cd LazyRecon chmod +x LazyRecon.sh ./LazyRecon.sh <target_domain>
Notes
- It’s suggested to run this tool in a VPS, such as DigitalOcean, for better speed & accuracy.
- Running this tool takes time, thus it’s recommended to run it under a screen or tmux session.
- The tool runs masscan with the option –rate 10000 for more accurate results. Based on experiments, masscan misses some open ports when scanning large port ranges. Depending on your environment, you could do the following to have a good balance between speed and accuracy:
- Increase the rate, and/or reduce the number of ports. For example, use the options –top-ports 1000 & –rate 100000.
- If you feel masscan and nmap are slow, you can run them in the background by changing the command portScan to portScan > /dev/null 2>&1 &.
Copyright (c) 2019 Capt. Meelo
Source: https://github.com/capt-meelo/