Lil Pwny v2.0 releases: auditing Active Directory passwords using Python
Lil Pwny
Lil Pwny is a Python application to perform an offline audit of NTLM hashes of users’ passwords, recovered from Active Directory, against known compromised passwords from Have I Been Pwned. The usernames of any accounts matching HIBP will be returned in a .txt file
There are also additional features:
- Ability to provide a list of your own passwords to check AD users against. This allows you to check user passwords against passwords relevant to your organisation that you suspect people might be using. These are NTLM hashed, and AD hashes are then compared with this as well as the HIBP hashes.
- Return a list of accounts using the same passwords. Useful for finding users using the same password for their administrative and standard accounts.
Changelog v2.0
Added
- Massive enhancements to make much better use of multiprocessing for the large HIBP password file, as well as more efficient importing and handling of Active Directory user hashes.
- Updated directory structure to play more nicely with more OS versions and flavours, rather than installing in the
srcdirectory. - Logging: Removed outdated text file output and implemented JSON formatted logging to either stdout or to .log file
- New option to obfuscate genuine password NTLM hashes in logging output. This is achieved by further hashing the hash with a randomly generated salt.
- Active Directory computer accounts are now not imported with AD user hashes. There is little value in assessing these, so no point importing them.
Installation
pip install lil-pwny
Use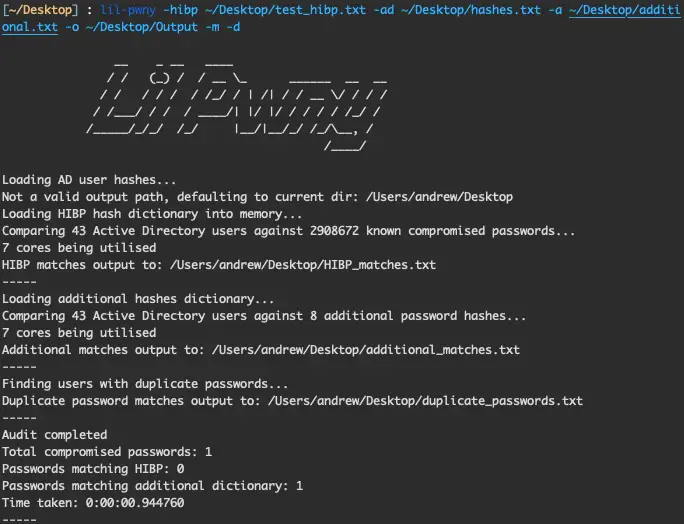
Example:
lil-pwny -hibp ~/hibp_hashes.txt -ad ~/ad_ntlm_hashes.txt -a ~/additional_passwords.txt -o ~/Desktop/Output -m -d
use of the -m flag will load the HIBP hashes into memory, which will allow for faster searching. Note this will require at least 24GB of available memory.
Getting input files
Step 1: Get an IFM AD database dump
On a domain controller use ntdsutil to generate an IFM dump of your AD domain. Run the following in an elevated PowerShell window:
ntdsutil
activate instance ntds
ifm
create full **output path**
Step 2: Recover NTLM hashes from this output
To recover the NTLM hashes from the AD IFM data, the Powershell module DSInternals is required.
Once installed, use the SYSTEM hive in the IFM data to recover the hashes in the format usernme:hash and save them to the file ad_ntlm_hashes.txt
$bootKey = Get-BootKey -SystemHivePath ‘.\registry\SYSTEM‘
Get-ADDBAccount -All -DBPath ‘.\Active Directory\ntds.dit‘ -BootKey $bootKey | Format-Custom -View HashcatNT | Out-File ad_ntlm_hashes.txt -Encoding ASCII
Step 3: Download the latest HIBP hash file
The file can be downloaded from here
The latest version of the hash file contains around 551 million hashes.
Tutorial
Copyright (C) 2020
Source: https://github.com/PaperMtn/






