LiMEaide v2.0.1 releases: remotely dump RAM of a Linux client
LiMEaide
LiMEaide is a python application designed to remotely dump RAM on a Linux client and create a volatility profile for later analysis on your localhost. I hope that this will simplify Linux digital forensics in a remote environment. In order to use LiMEaide all you need to do is feed a remote Linux client IP address, sit back, and consume your favourite caffeinated beverage.
How does it work?
- Make a remote connection with the specified client over SHH
- Transfer necessary build files to the remote machine
- Build the memory scrapping Loadable Kernel Module (LKM) LiME
- LKM will dump RAM
- Transfer RAM dump and RAM maps back to host
- Build a Volatility profile
LiMEaide has 3 primary modes of operation
- Remote – Initiates connection with SSH and transfers data over SFTP
- Socket – Initiates a connection with SSH but transfers the memory image over a TCP socket. This means that the image is NOT written to disk. Tools are still transferred over SFTP.
- Locally – Have a copy of LiMEiade on a flash drive or other device. Does not transfer any data to the client, maintain execution in its working directory. All transfers are completed with internal methods and no network sockets are opened.
Installation
sudo apt-get install python3-paramiko python3-termcolor
sudo pip3 install paramiko termcolor
LiME
In order to use LiME, you must download and move the source into the LiMEaide/tools directory. Make sure the LiME folder is named LiME. The full path should be as follows: NOTE: If you would like to build Volatility profiles, you must use my forked version of LiME. This provides debugging symbols used by dwarfdump.
LiMEaide/tools/LiME/
How to…
- Download LiME v1.7.8.1
- Extract into
LiMEaide/tools/ - Rename folder to
LiME
dwarfdump
In order to build a volatility profile, we need to be able to read the debugging symbols in the LKM. For this, we need to install dwarfdump. If you encounter any issues finding/installing dwarfdump see the volatility page here
sudo apt-get install dwarfdump
Usage
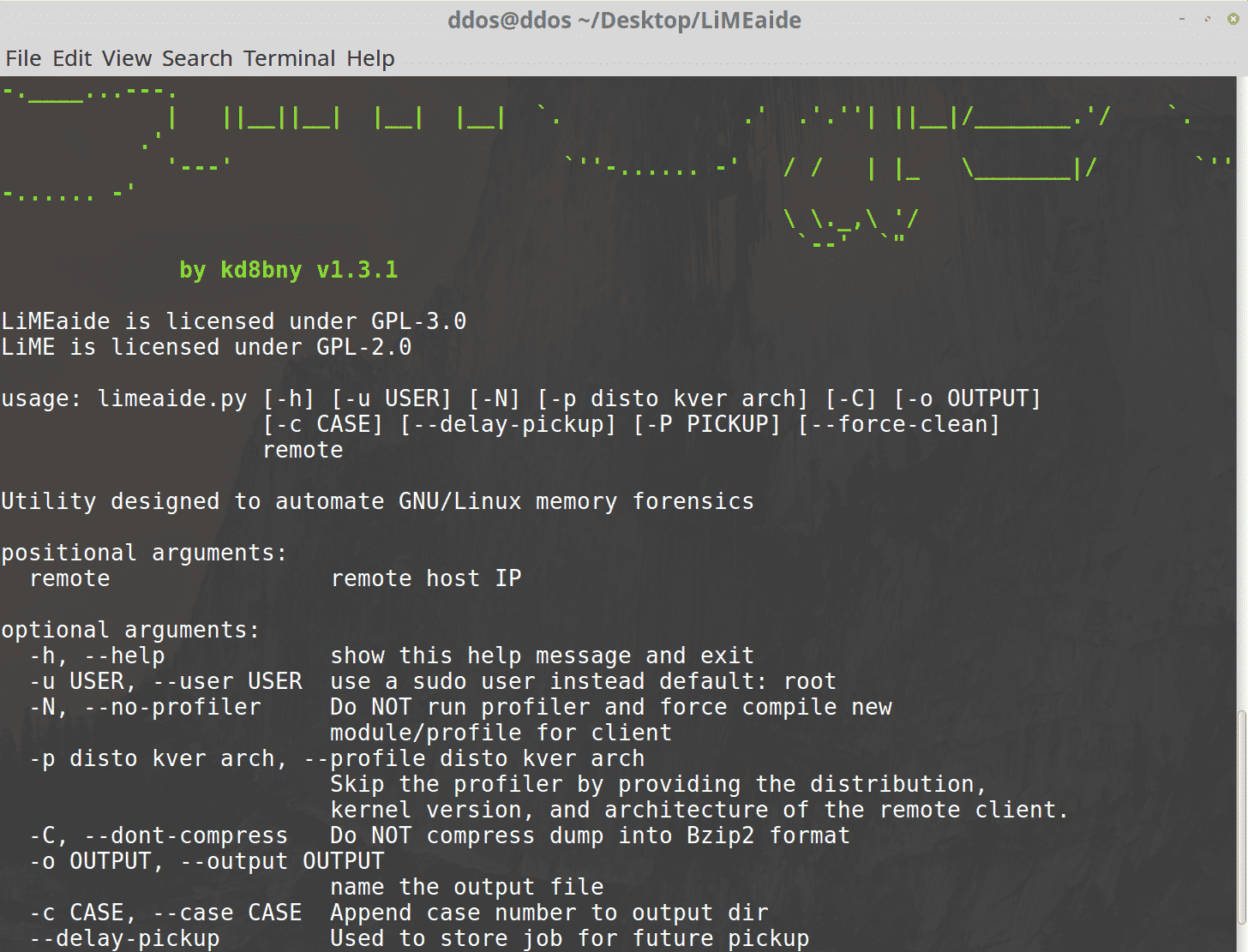
python3 limeaide.py <IP>
limeaide.py [OPTIONS] REMOTE_IP
-h, –help
Shows the help dialog
-u, –user : <user>
Execute memory grab as sudo user. This is useful when root privileges are not granted.-p, –profile : <distro> <kernel version> <arch>
Skip the profiler by providing the distribution, kernel version, and architecture of the remote client.-N, –no-profiler
Do NOT run profiler and force the creation of a new module/profile for the client.-C, –dont-compress
Do not compress memory file. By default memory is compressed on host. If you experience issues, toggle this flag. In my tests I see a ~60% reduction in file size–delay-pickup
Execute a job to create a RAM dump on target system that you will retrieve later. The stored job
is located in the scheduled_jobs/ dir that ends in .dat-P, –pickup <path to job file .dat>
Pick up a job you previously ran with the –delayed-pickup switch.
The file that follows this switch is located in the scheduled_jobs/ directory
and ends in .dat-o, –output : <name>
Change name of output file. Default is dump.bin-c, –case : <case num>
Append case number to front of output directory.–force-clean
If previous attempt failed then clean up client
Copyright (C) kd8bny
Source: https://github.com/kd8bny/






