Invoke-LiveResponse: live response tool for targeted collection
Invoke-LiveResponse
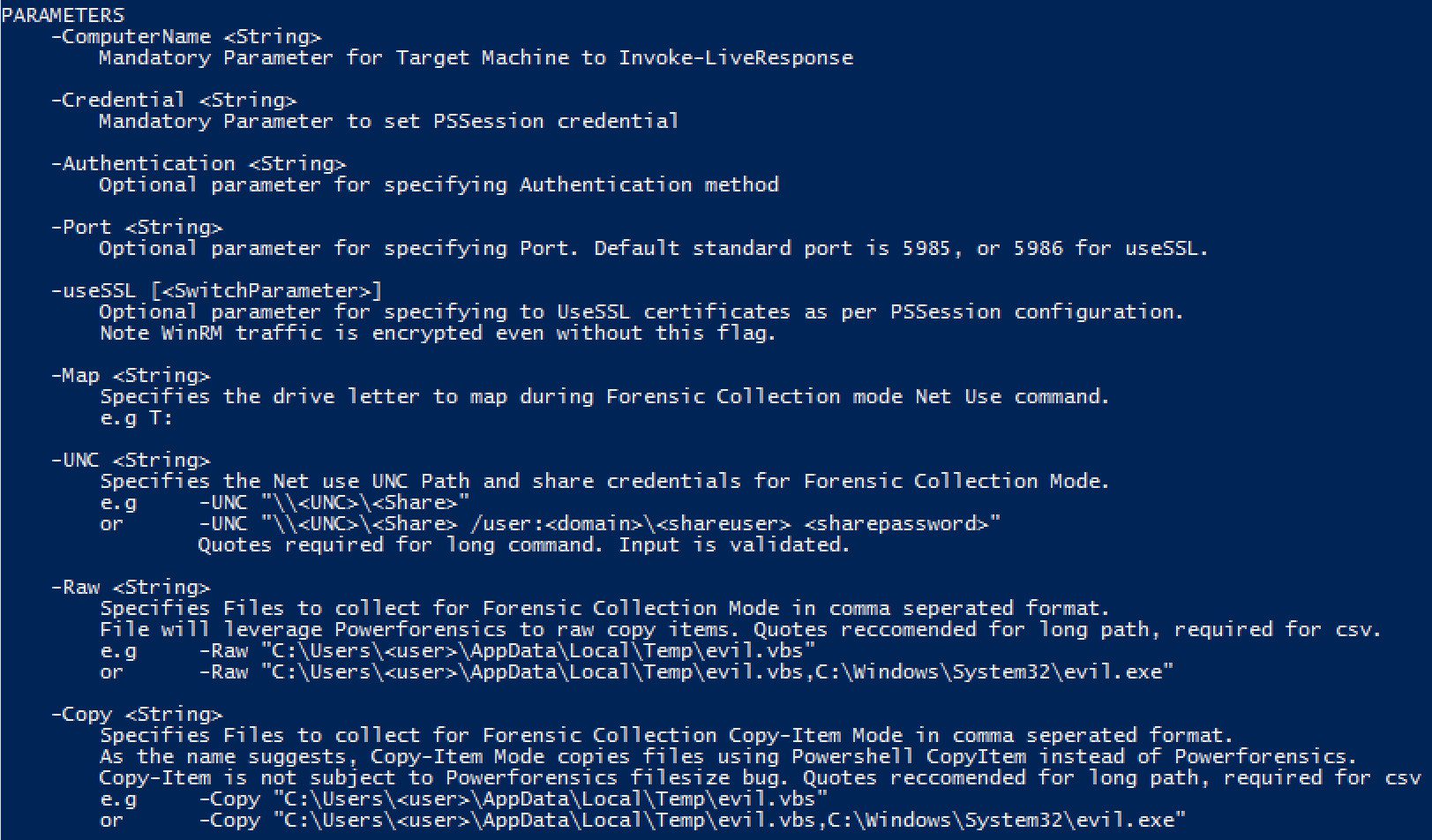
The current scope of Invoke-LiveResponse is a live response tool for targeted collection. There are two main modes of use in Invoke-LiveResponse and both are configured by a variety of command line switches.
ForensicCopy
- Reflectively loads Powerforensics onto the target machine to enable raw disk access.
- Leverages a scriptblock for each configured function of the script.
- Common forensic artefacts and custom file collections.
- WinPMem for memory support
- Depending on the selected switches, each selected capability is joined at runtime to build the scriptblock pushed out to the target machine.
Live Response
- Inspired by the Kansa Framework, LiveResponse mode will execute any Powershell scripts placed inside a content folder.
- Results consist of the standard out from the executed content, redirected from the collection machine to a local Results folder as ScriptName.txt.
- The benefit of this method is the ability to operationalize new capability easily by dropping in new content with the desired StdOut.
Other content
- Get-Powerforensics.ps1 – Installs Powerforensics to a user profile
- Get-Forensicating.ps1 – Installs Invoke-LiveResponse and Powerforensics to a user profile.
- Invoke-ForensicCopy.ps1 – Powershell function to leverage Powerforensics API for a raw copy with the best performance.
- Content – Contains some nice content from around the place, mainly from Kansa and SpectreOps ACE project. I’ll add more as I remember/find new things.
Installation
- Download Powershell-IR and rename to Invoke-LiveResponse into Powershell profile.
- Download Powerforensics into Powershell Profile
git clone https://github.com/mgreen27/Powershell-IR.git
Use
Import-Module Invoke-LiveResponse
Help: Get-Help Invoke-LiveResponse -detailed
Tutorial
Source: https://github.com/mgreen27/






