Besides functionality from these two previous scripts it incorporates some of its own and as such aims to be a comprehensive assistant for operations and utilities related to system enumeration, vulnerability identification, exploitation and privilege escalation.
Download
git clone https://github.com/NullArray/MIDA-Multitool.git
Usage
After a system has been successfully compromised MIDA should be downloaded to the host in question either with wget or git, after it has been unpacked/cloned the shell script needs to be made executable with chmod +x mida.sh
Upon doing so it can be run on the target host. The options available to the user are below.
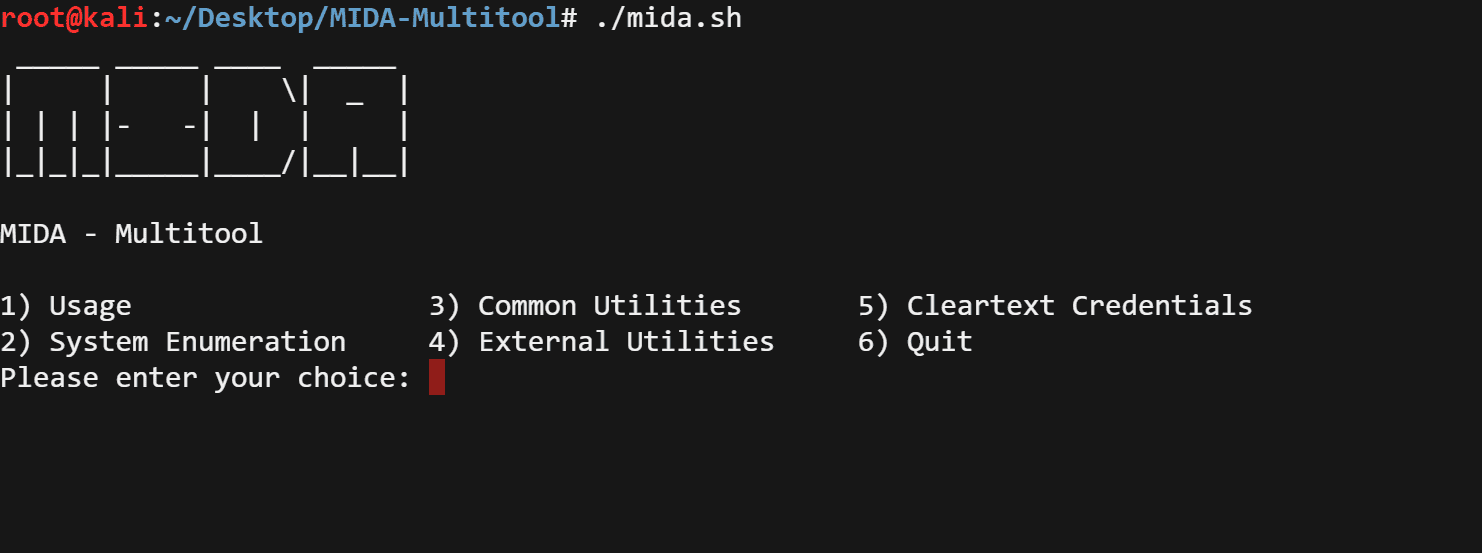
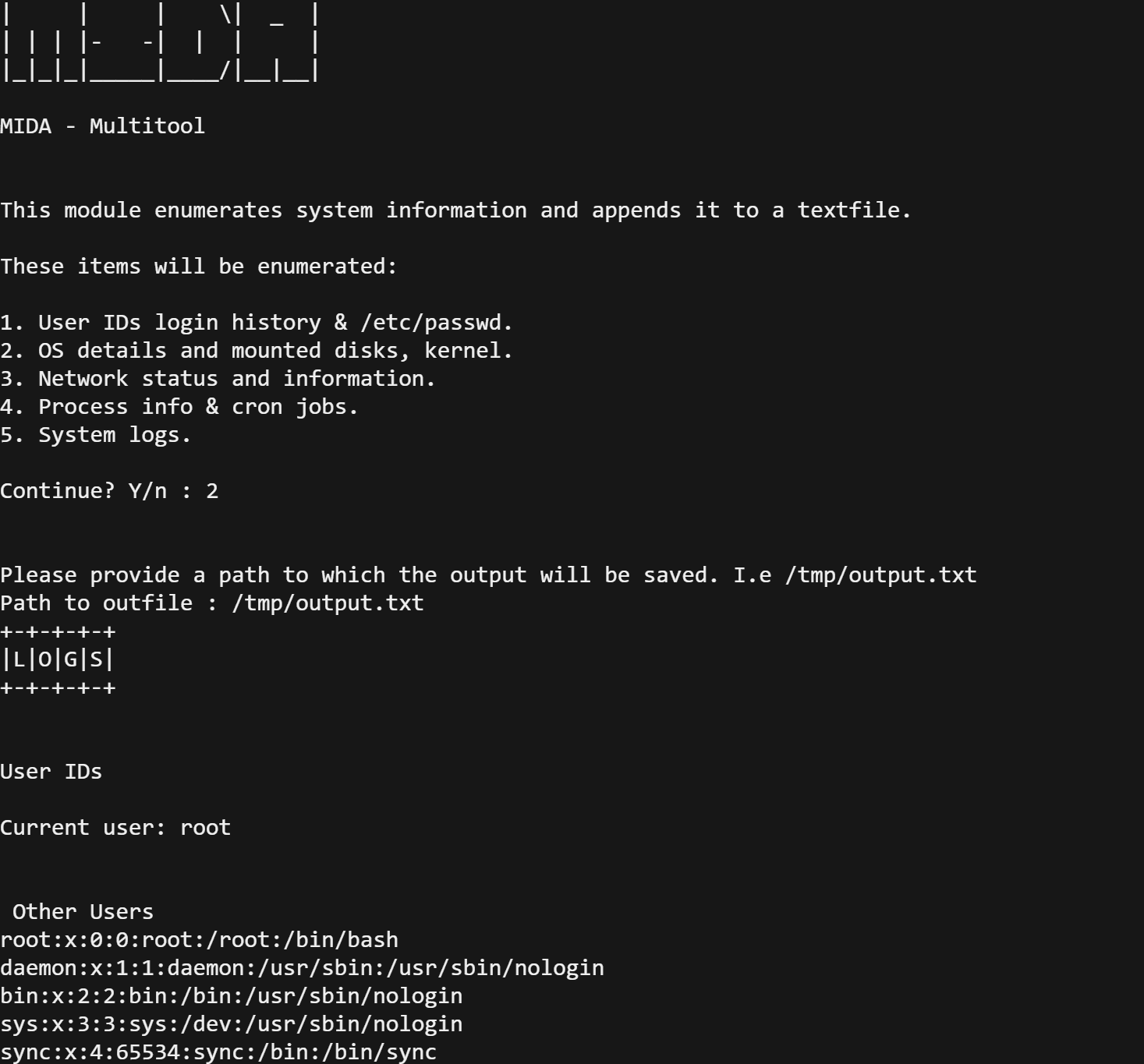
The ‘Usage’ option prints this informational message. The option ‘System Enumeration’ attempts to retrieve system information such as OS and kernel details, network status, processes, system logs and more. ‘Common Utilities’ checks for the existence of useful utilities such as telnet, netcat, tcpdump etc. ‘External Utilities’ opens a menu which lets you download external utilities that may prove to be helpful with further enumeration, vulnerability identification, and privilege escalation.
Finally the option ‘Cleartext Credentials’ searches for text and web application files that contain certain keywords in order to find potential cleartext passwords.
Scripts available for download with MIDA
Linux Priv Checker by SecuritySift
Linux Exploit Suggester by Jondonas
Unix Priv-Esc Check by Pentestmonkey
Source: https://github.com/NullArray/





