moneta: live usermode memory analysis tool
Moneta
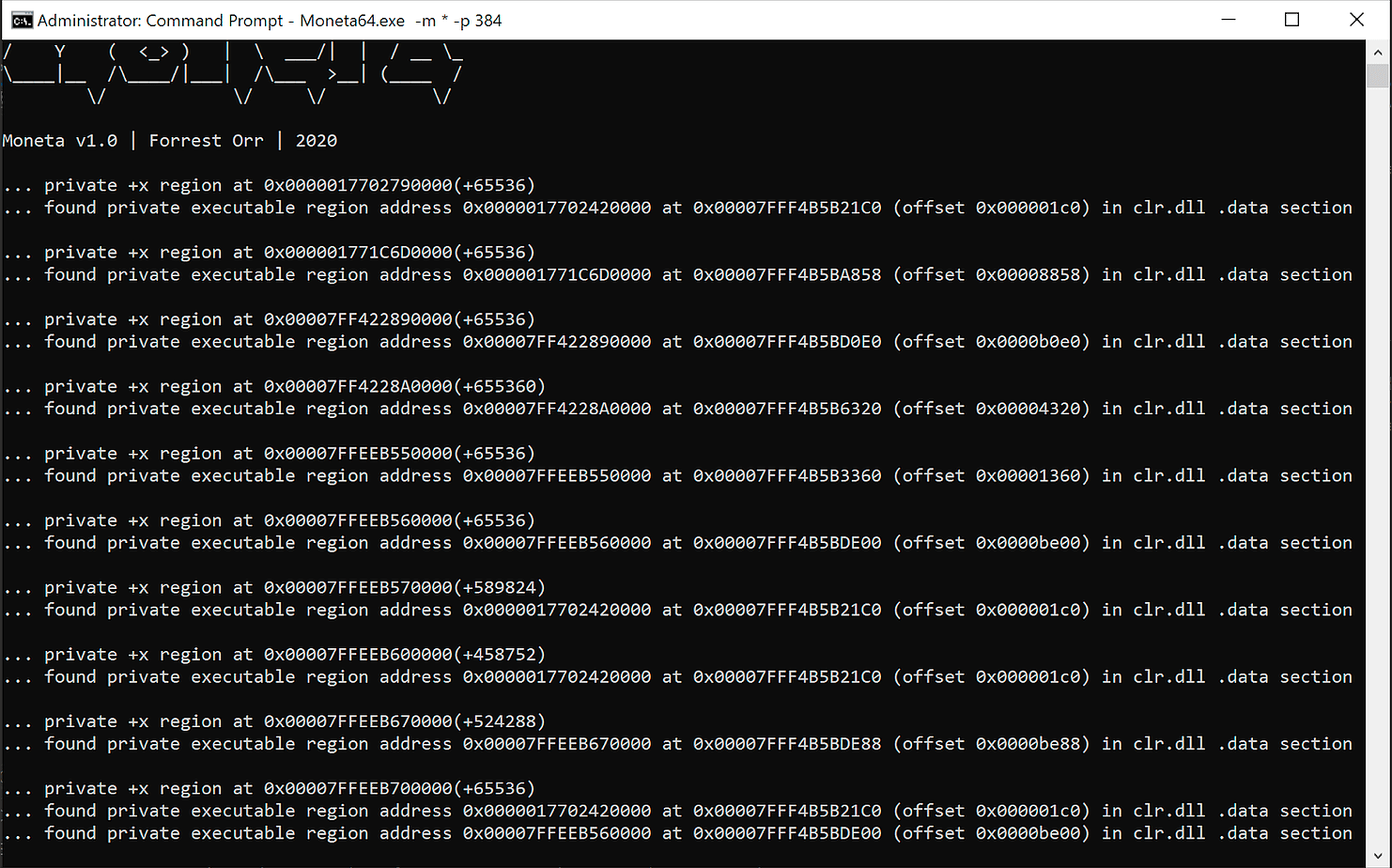
Moneta is a live usermode memory analysis tool for Windows with the capability to detect malware IOCs.
With fileless malware becoming ubiquitous in the Red Teaming world, dynamic code is a feature of virtually every single “malware” presently in use. Interestingly, the takeaway concept from this analysis seems to be that attempting to detect such memory is nearly impossible with IOCs alone when the malware writer understands the landscape he is operating in and takes care to camouflage his tradecraft in one of the many existing abnormalities in Windows. Prime among these being some of the false positives discussed previously, such as the OS-enacted DLL hollowing of User32.dll in Wow64 processes, or the +RWX subregions within CLR image memory. There were far too many such abnormalities to discuss within the scope of this text alone, and the list of existing filters for Moneta remains far from comprehensive.
Moneta provides a useful way for attackers to identify such abnormalities and customize their dynamic code to best leverage them for stealth. Similarly, it provides a valuable way for defenders to identify/dump malware from memory and also to identify the false positives they may be interested in using to fine-tune their own memory detection algorithms.
Moneta focuses primarily on three areas for its IOCs. The first is the presence of dynamic/unknown code, which it defines as follows:
-
Private or mapped memory with executable permissions.
-
Modified code within mapped images.
-
PEB image bases or threads with start addresses in non-image memory regions.
-
Unmodified code within unsigned mapped images (this is a soft indicator for hunting, not a malware IOC).
Secondly, Moneta focuses on suspicious characteristics of the mapped PE image regions themselves:
-
Inconsistent executable permissions between a PE section in memory and its counterpart on disk. For example a PE with a section which is +RX in memory but marked for +R in its PE header on disk.
-
Mapped images in memory with modified PE headers.
-
Mapped images in memory whose FILE_OBJECT attributes cannot be queried (this is an indication of phantom DLL hollowing).
Thirdly, Moneta looks at IOCs related to the process itself:
-
The process contains a mapped image whose base address does not have a corresponding entry in the PEB.
-
The process contains a mapped image whose base address corresponds to an entry in the PEB but whose name or path (as derived from its FILE_OBJECT) do not match those in the PEB entry.
Download
Copyright (C) 2020 forrest-orr





