OffensiveNotion v1.5 releases: platform for offensive operations
OffensiveNotion: a platform for offensive operations
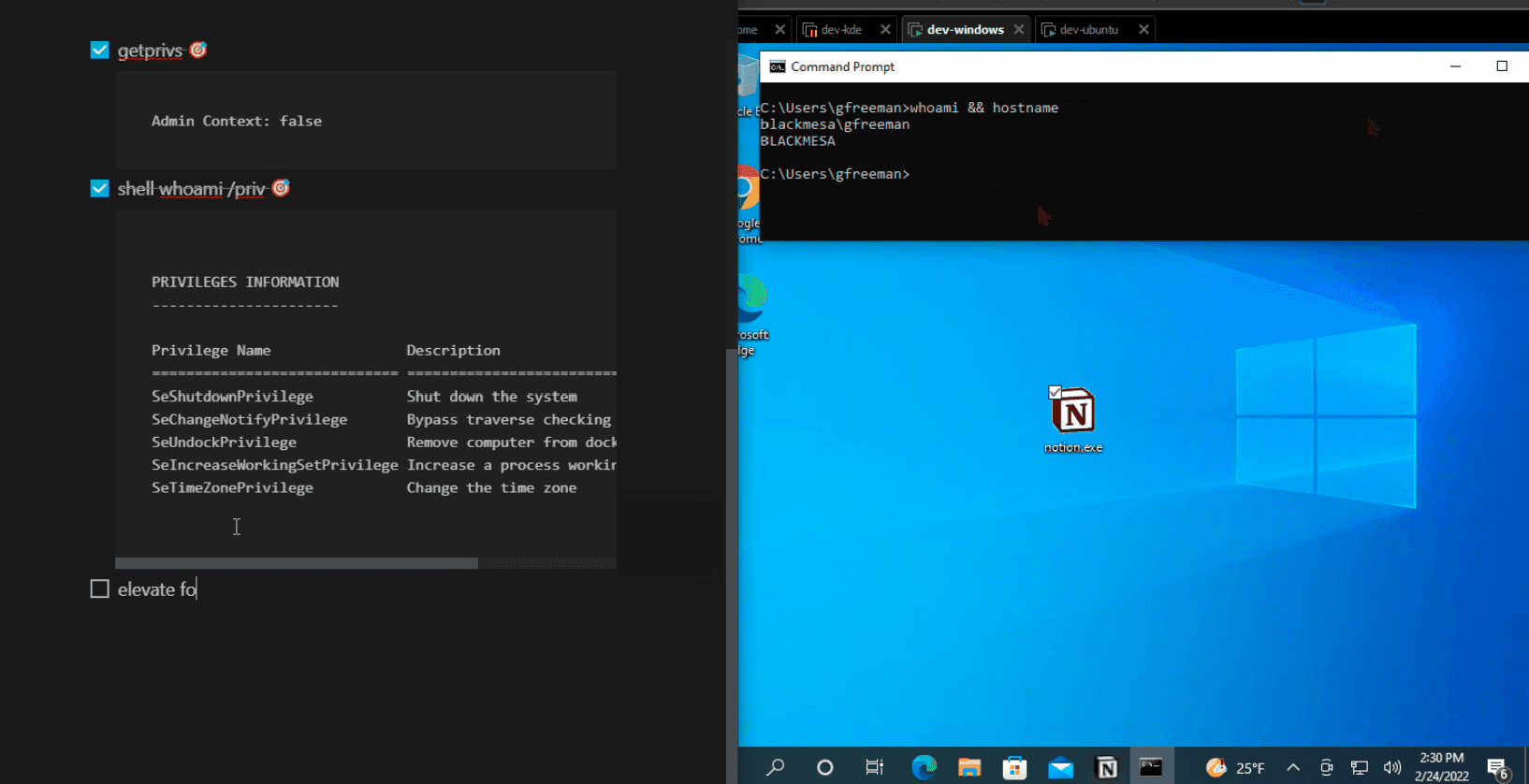
OffensiveNotion combines the capabilities of a post-exploitation agent with the power and comfort of the Notion notetaking application. The agent sends data to and receives commands from your Notion page. Your C2 traffic blends right in as the agent receives instructions and posts results via the Notion developer API. And when your blue team looks for evidence of shenanigans, none will be the wiser.
Feature
- 📡 A full-featured C2 platform built on the Notion notetaking app.
- 🚧 Easy setup: set up your Notion developer API account, drop the Agent to the target, run, and enjoy!
- 🖥️ Cross-platform agent built-in Rust that compiles for Linux and Windows with the same code base. Includes a Python setup/controller script to simplify the process.
- ☢️ A range of capabilities including port-scanning, privilege escalation, asynchronous command execution, file download, and shellcode injection, all controlled from the comfort of a Notion page!
- 📜 Document as you go! The agent identifies special syntax to run commands, so feel free to use the rest of the Notion page to document your operation.
- 🕵️♀️ Stealth! C2 comms ride over the Notion API natively. Your C2 traffic looks like someone is using Notion for its intended purpose.
Changelog v1.5
This release is centered around one big new feature: execute-assembly!
With the amazing work of Yamakadi on CLROxide, it became eminently possible to add this feature to ON, so here we are!
Install & Use
Copyright (c) 2022 mttaggart & HuskyHacks





