PE Tools – Portable executable (PE) manipulation toolkit
PE Tools lets you actively research PE files and processes. Process Viewer and PE files Editor, Dumper, Rebuilder, Comparator, Analyzer are included. PE Tools is an oldschool reverse engineering tool with a long history since 2002. PE Tools was initially inspired by LordPE (Yoda).
Features
PE Editor
- PE and DOS Headers Editor
- PE Sections Editor
- PE Directory Viewer and Editor
- Export Directory Editor
- Import Directory Editor
- Resource Directory Viewer
- Exception Directory Viewer
- Relocation Directory Viewer
- Debug Directory Viewer
- TLS Directory Editor
- Load Config Directory Editor
- Bound Directory Editor
File Location Calculator (FLC)
- Virtual Address
- Relative Virtual Address
- Raw File Offset
PE Files Comparator
- Side-by-side comparison of headers and characteristics of two PE files
Process Viewer and Manager
- Show basic process information
- Show process modules
PE Dumper
- Running process dumper
- Full Dump
- Partial Dump
- Region Dump
PE Rebuilder
- Dump Fixer
- Relocation Wiper
- Resource Directory Rebuilder
- PE file Validation
- Imports Binder
- ImageBase Changer
PE Sniffer
- Signature analysis of PE files
- Packer detection
HEX Editor
- HEX Editor available in:
- Section Editor via section context menu
- Every Data Directory in Directory Editor
Use
Entropy View
- Entropy Viewer available in:
- Main PE Editor dialogue
- Section Editor via section context menu
- File Compare dialog for both compared files
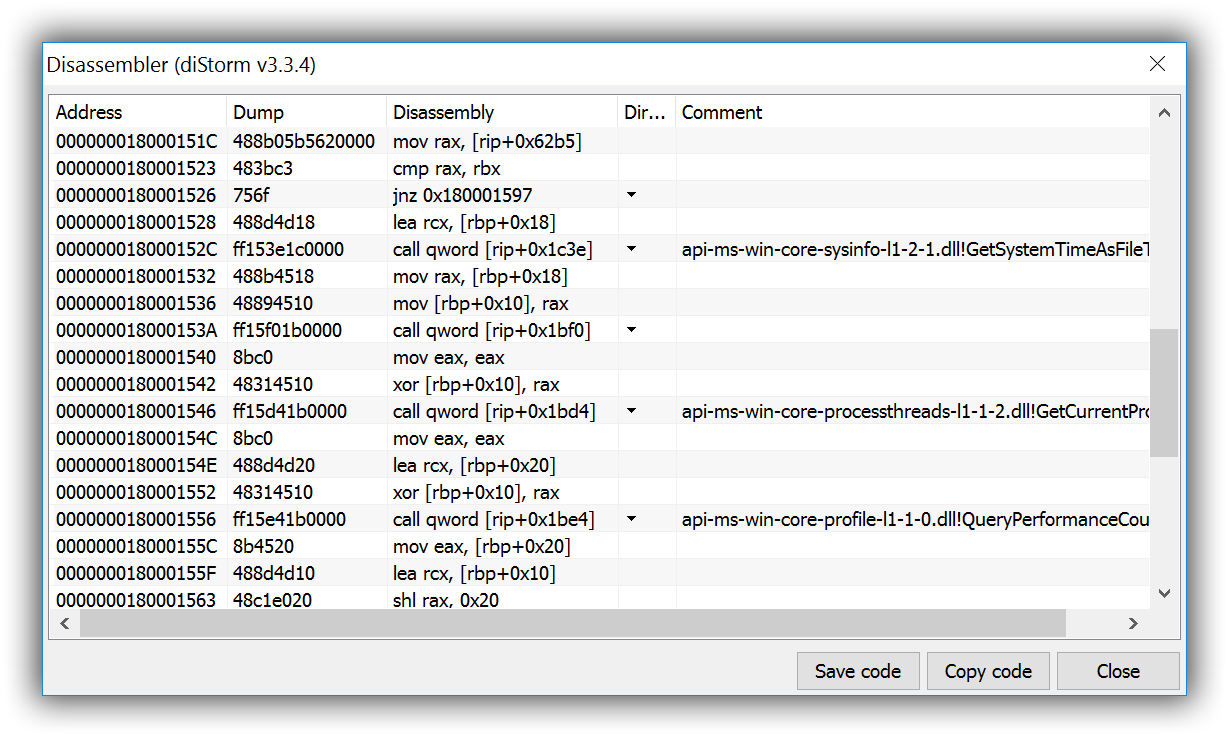
64-bit Disassembler
- diStorm v3.3.4
- Shows jmp / call direction
Load Config Directory Editor
- IMAGE_LOAD_CONFIG_DIRECTORY support
- Additional Load Config Directory values and size support (non-standard sizes)
High-DPI display modes support
- 192 DPI supported
DPImodes supported and tested: 96, 120, 144, 192- Graphics redrawn:
- Main Application Icon
- Logo
- Toolbar icons
Copyright (c) 2017 PE Tools
Source: https://github.com/petoolse/