portspoof: enhance OS security
Portspoof
The Portspoof program primary goal is to enhance your system’s security through a set of new camouflage techniques. As a result of applying them your attackers’ port scan result will become entirely mangled and to very significant extent meaningless.
Techniques used to achieve this:
- All configured TCP ports are always open
Instead of informing an attacker that a particular port is in a CLOSED or FILTERED state a system running Portspoof will return SYN+ACK for every connection attempt.
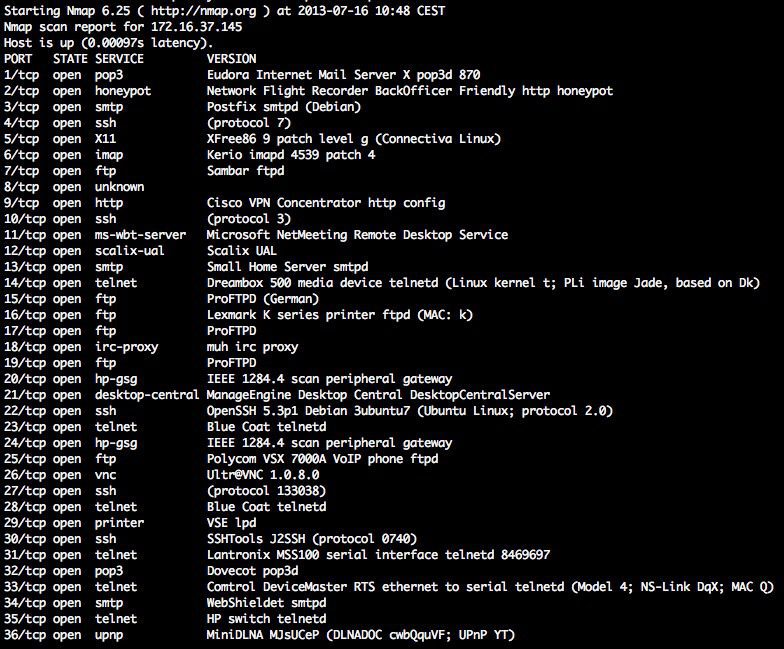
Result: As a result, it is impractical to use stealth (SYN, ACK, etc.) port scanning against your system since all ports are always reported as OPEN. With this approach, it is really difficult to determine if a valid software is listening on a particular port (check out the screenshots).
- Every open TCP port emulates a valid services
Portspoof has a huge dynamic service signature database, that will be used to generate responses to your offenders scanning software service probes.
Scanning software usually tries to determine a service that is running on an open port. This step is mandatory if one would want to identify port numbers on which you are running your services on a system behind the Portspoof. For this reason, Portspoof will respond to every service probe with a valid service signature, that is dynamically generated based on a service signature regular expression database.
Result: As a result, an attacker will not be able to determine which port numbers your system is truly using.
Reverse exploitation with Portspoof:
Portspoof can be used as an ‘Exploitation Framework Frontend’, that turns your system into a responsive and aggressive machine. In practice, this usually means exploiting your attackers’ tools and exploits.
At the moment there are few example exploits in the configuration file (portspoof.conf). One of them exploits Nmap 6.25 default script.
Overview:
Portspoof is meant to be a lightweight, fast, portable and secure addition to any firewall system or security system. The general goal of the program is to make the reconnaissance phase slow and bothersome for your attackers as much as it is only possible. This is quite a change to the standard 5s Nmap scan, that will give a full view of your systems running services.
By using all of the above-mentioned techniques together:
- your attackers will have a tough time while trying to identify all of your listening services.
- the only way to determine if a service is emulated is through a protocol probe (imagine probing protocols for 65k open ports!).
- it takes more than 8 hours and 200MB of sent data in order to get all of the service banners for your system ( nmap -sV -p – equivalent).
Features
The most important features that Portspoof has:
– Portspoof is a userland software and does not require root privileges!
– Binds to just one tcp port per a running instance
– Easily customizable through your iptables rules
– Marginal CPU/memory usage (multithreaded)
– More than 9000 dynamic service signatures are supported!
Nmap port scan results for TCP ports 1:65353 (only one service is real):
Install
git clone https://github.com/drk1wi/portspoof.git
cd portspoof
./configure
make && make install
Use
More…
Copyright (C) 2012 Piotr Duszyński <piotr[at]duszynski.eu>
Source: https://github.com/drk1wi/






