pr0cks: transparent proxy to forward all TCP and DNS traffic through a SOCKS/SOCKS5/HTTP(CONNECT) proxy
pr0cks
python script to transparently forward all TCP and DNS traffic through socks (like ssh -D option) or HTTPS (CONNECT) proxy using iptables -j REDIRECT target. Only works on Linux for now.
Features:
- set up a local transparent proxy compatible with socks4 socks5 and HTTP CONNECT proxies allowing to forward any TCP traffic transparently using iptables
- set up a local transparent DNS proxy translating UDP port 53 requests to TCP allowing DNS traffic to go through a proxy without UDP support (like ssh -D option)
- DNS caching mechanism to speed up the DNS resolutions through pr0cks
Download
git clone https://github.com/n1nj4sec/pr0cks.git
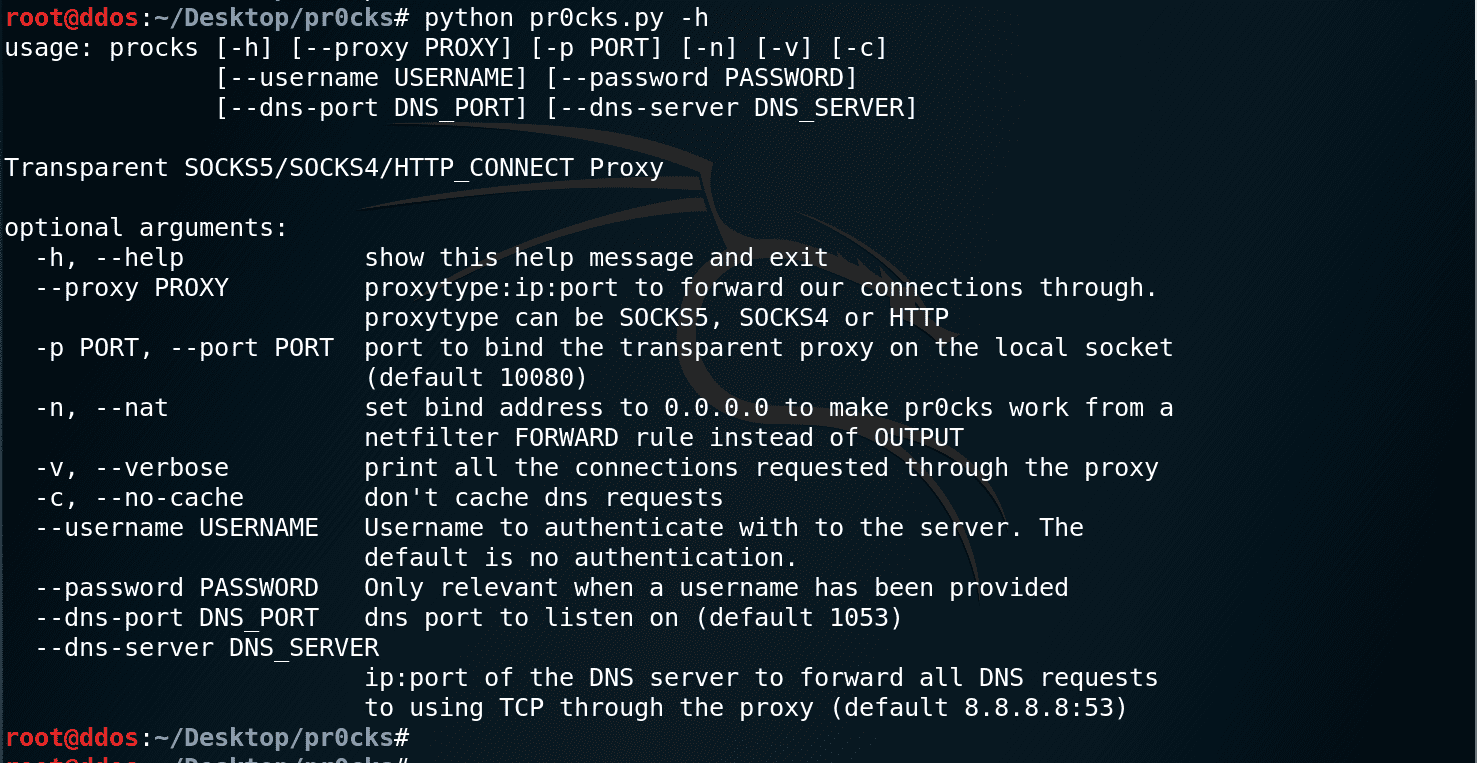
Usage
All your TCP traffic and DNS traffic should now pass through the ssh server kinda like if you had set up a tun VPN through ssh but without admin rights on the server! #help
Example: let’s rock
As an example, we will use the socks5 proxy of openssh (the option -D)
$ ssh -D 1080 user@sshserver
then you can add some iptables rules :
$ iptables -t nat -A OUTPUT ! -d <my_ssh_server_IP>/32 -o eth0 -p tcp -m tcp -j REDIRECT –to-ports 10080
$ iptables -t nat -A OUTPUT -o eth0 -p udp -m udp –dport 53 -j REDIRECT –to-ports 1053
then start pr0cks :
$ python pr0cks.py –proxy SOCKS5:127.0.0.1:1080
Copyright (C) 2015 n1nj4sec
Source: https://github.com/n1nj4sec/





