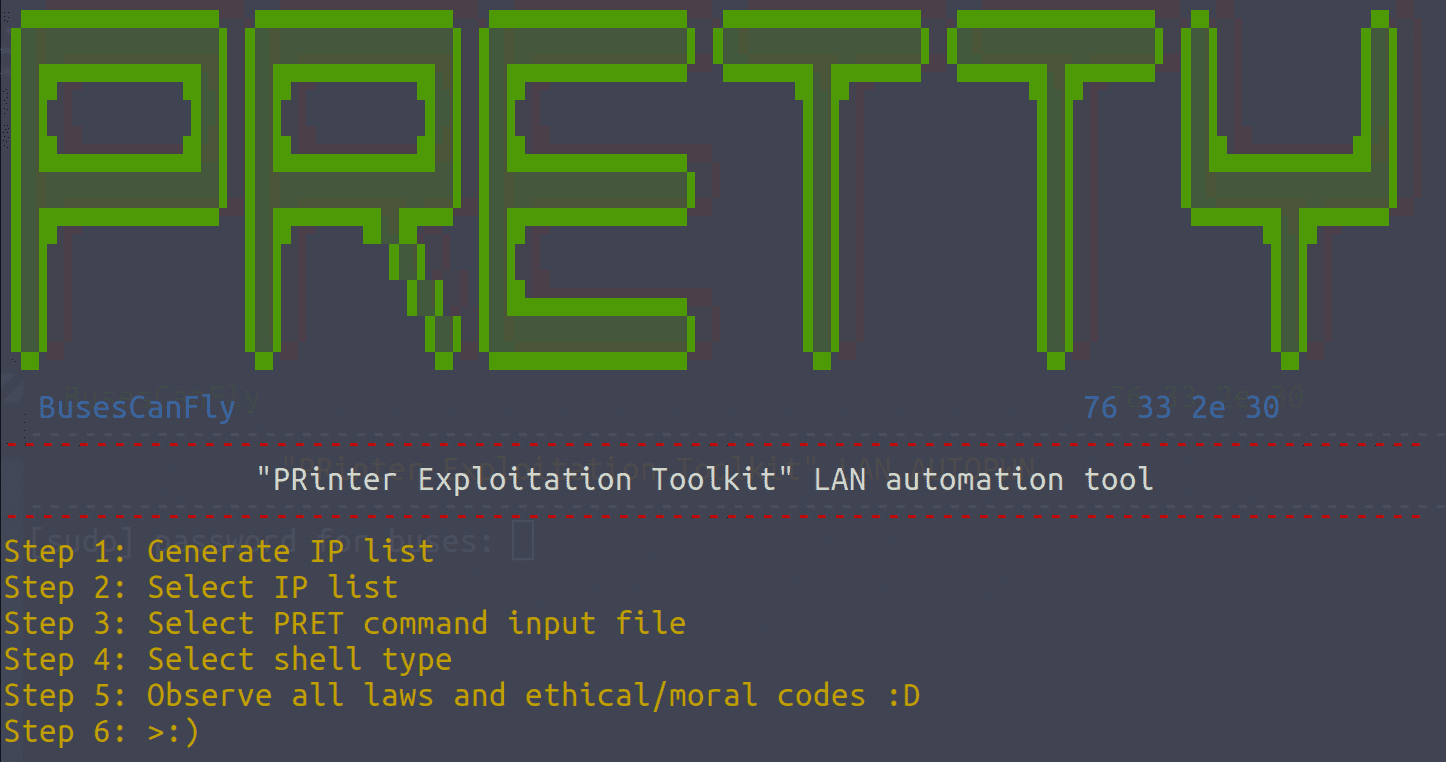
PRETty: PRinter Exploitation Toolkit LAN automation tool
PRETty
“PRinter Exploitation Toolkit” LAN automation tool
PRETty is useful when a large number of printers are present on a network. Instead of scanning, logging, and manually running PRET against each individual printer, PRETty will automatically discover and run chosen PRET payloads against all printers on the target network.
Additionally, PRETty can be used to automate command/payload delivery to any given list of printers.
- PRETty automatically scans the LAN for HP/Brother/Kyocera printers and creates an IP list for itself
- However, you can place custom IP lists in PRETty/IP/
- PRETty comes with pre-made command list files for PRET located in PRETty/commands/
- However, you can place additional command list files in PRETty/commands/
Installation
- Install PRET and all required dependencies
- Install requirements: sudo pip install -U argparse termcolor and sudo apt -y install arp-scan tshark
- Navigate to where you installed PRET: cd PRET
- Install PRETty into PRET: git clone https://github.com/BusesCanFly/PRETty
- Navigate to PRETty: cd PRETty
- Make PRETty executable: chmod +x PRETty.py
- One line variant (from PRET folder): sudo apt -y install arp-scan tshark && sudo pip install -U argparse termcolor && git clone https://github.com/BusesCanFly/PRETty && cd PRETty && chmod +x PRETty.py
- One line variant w/ PRET installation: sudo apt -y install imagemagick ghostscript arp-scan tshark && sudo pip install -U argparse termcolor colorama pysnmp && git clone https://github.com/RUB-NDS/PRET && cd PRET && git clone https://github.com/BusesCanFly/PRETty && cd PRETty && chmod +x PRETty.py
Use
./PRETty.py
Copyright (C) 2018 BusesCanFly
Source: https://github.com/BusesCanFly/






