RogueAP-Detector: Rogue Access Point Detector
RogueAP Detector
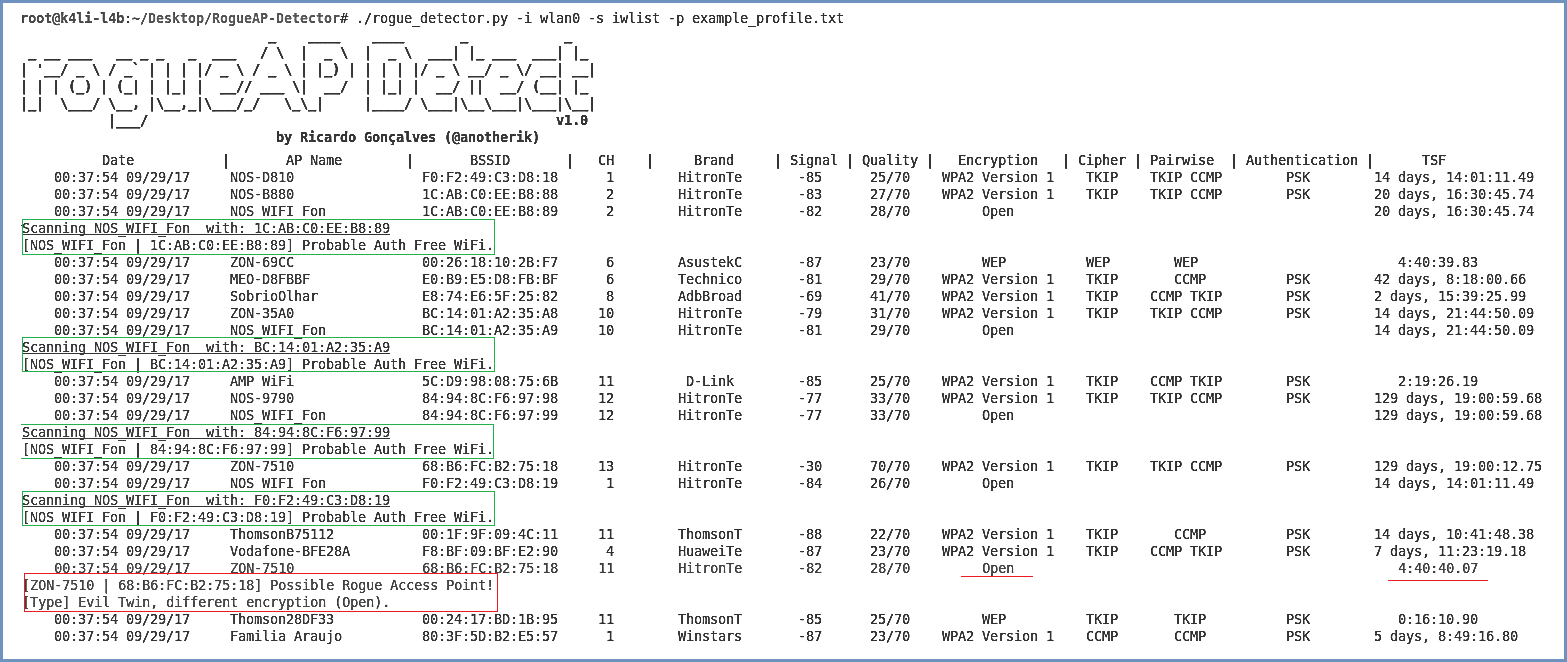
rogueAP Detector is an open source tool to detect Wi-Fi Rogue Access Points, covering the most commonly known attacks. This tool is a modular framework composed of Scanners, Detectors and Actuators, which are responsible for scanning for available APs, apply a set of heuristics to detect them and apply a defensive mechanism.
Modules
- Scanners: Methods to scan the network
- Detectors: Set of passive detectors to identify RogueAP types
- Actuators: Set of active detectors to identify RogueAP types
Install
git clone https://github.com/anotherik/RogueAP-Detector.git
./dependencies.sh
Use
./rogueAP_detector.py
Options
Examples:
- Scan for RAPs without a profile – (iwlist mode)
./rogueAP_detector.py -i iface -s iwlist - Scan for RAPs using a profile – (iwlist mode)
./rogueAP_detector.py -i iface -s iwlist -p example_profile.txt - Scan for RAPs using a profile – (scapy mode)
./rogueAP_detector.py -i iface -s scapy -p example_profile.txt - Scan for RAPs using a profile and karma detect active mode enabled – (iwlist mode)
./rogueAP_detector.py -i iface1 -im iface2 -s iwlist -p profile.txt -a - Create a RAP
./rogueAP_detector.py -im iface -h - Deauthenticate defensive mechanism mode
./rogueAP_detector.py -im iface -d - Deauthentication attacks detection
./rogueAP_detector.py -im iface -deauth_detect
Copyright (c) 2017 Ricardo Gonçalves
Source: https://github.com/anotherik/