SamuraiWTF 5.3 released: a web pen-testing environment
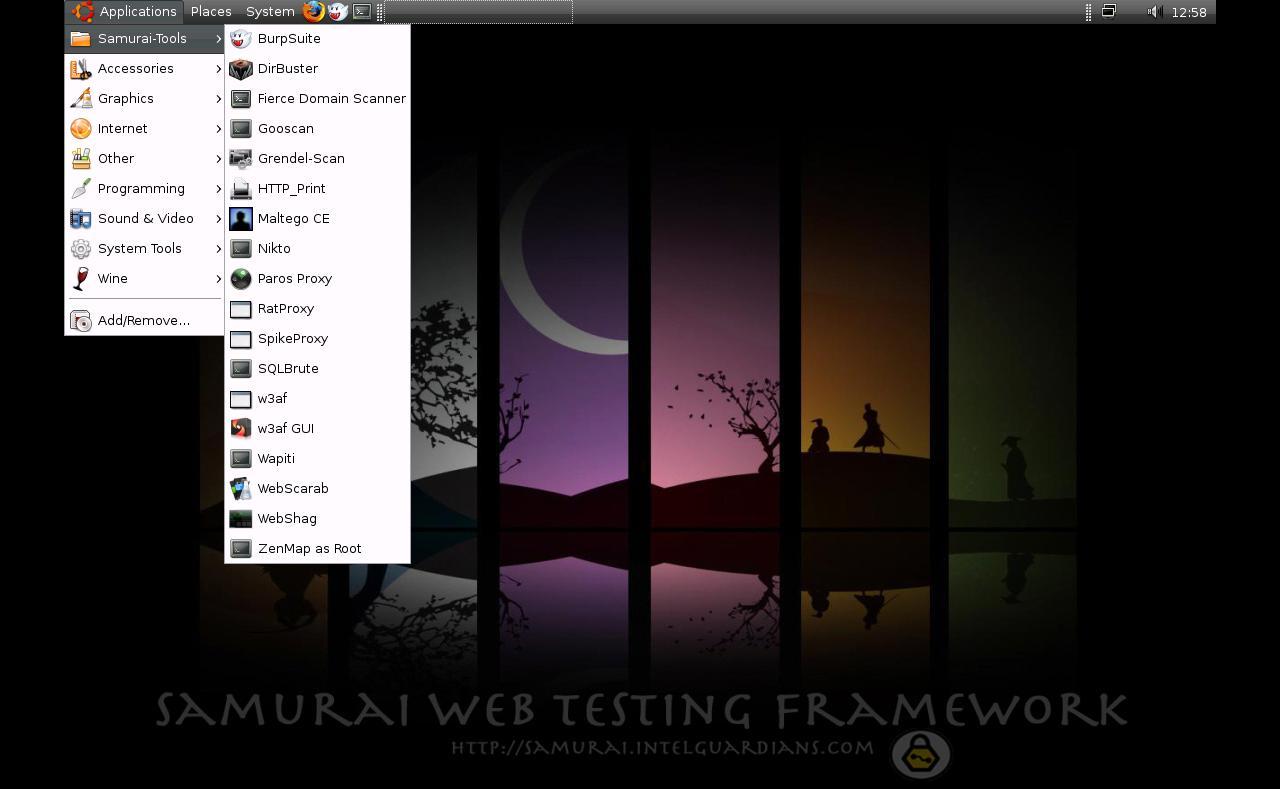
The Samurai Web Testing Framework (SamuraiWTF) is a live Linux environment that has been pre-configured to function as a web pen-testing environment. The CD contains the best of open-source and free tools that focus on testing and attacking websites. In developing this environment, we have based our tool selection on the tools we use in our security practice. We have included the tools used in all four steps of a web pen test.
Changelog v5.3
- Updated Node version by @JGillam in #171
- Hyperv and Ubuntu 20.04 by @JGillam in #174
- 5.3 Release by @secureideas in #181





