SECMON: web-based tool for the automation of infosec watching and vulnerability management
SECMON – Infosec Watching Tool
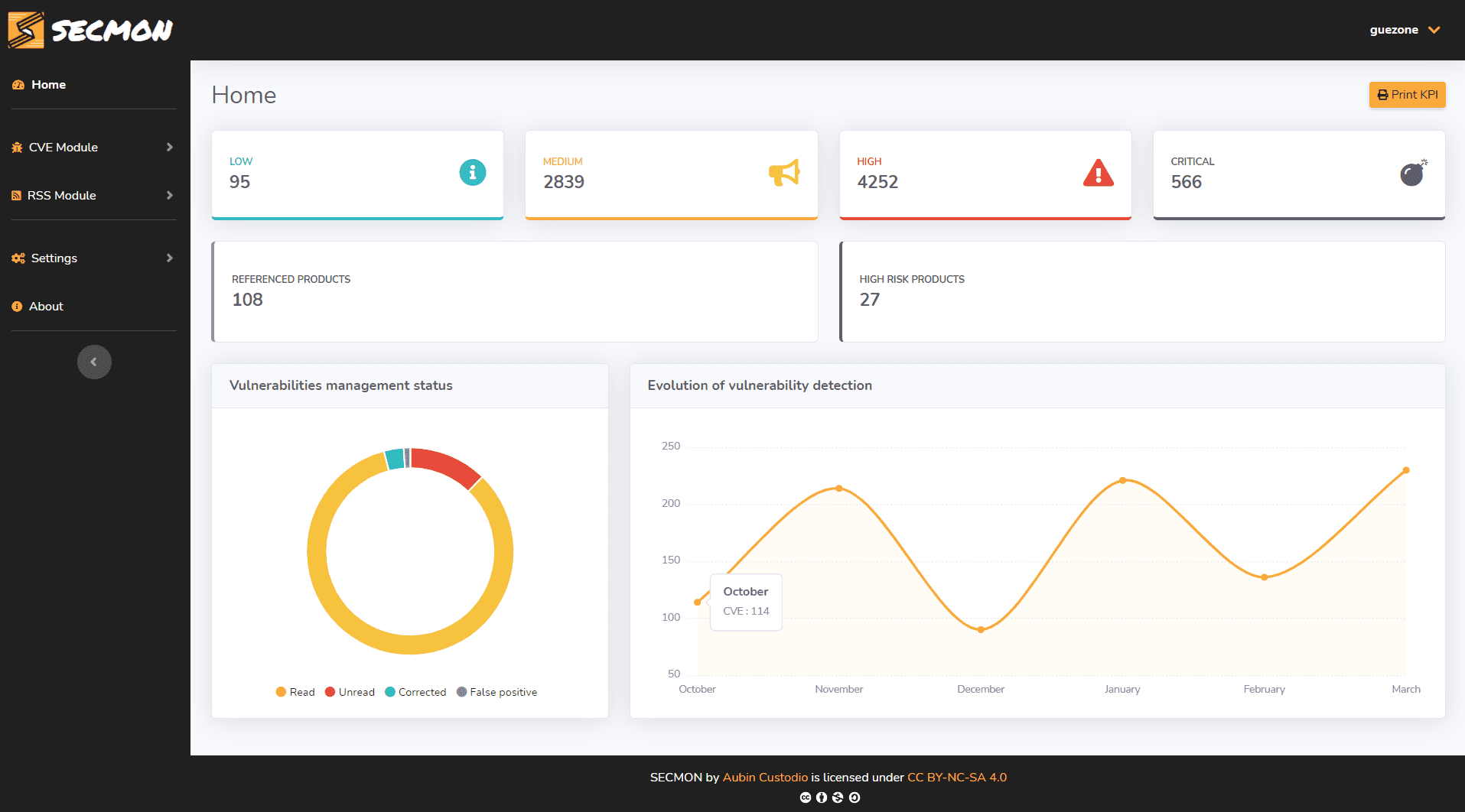
SECMON is a web-based tool for the automation of infosec watching and vulnerability management with a web interface.
Features
- Mail alerting when a new CVE is published and which concerns your product list
- Mail alerting when “cyber-security” news is published: new threats, recent attacks, events, etc.
- Visualize the high-security risk products present on your IT infrastructure
- Download CVE Excel report by date range
- Display top cybersecurity subject (Light cyber landscape)
- Logs easy to integrate into a SIEM (verified on Splunk and Graylog)
- View the latest CVE and latest news related to cybersecurity are published
- Assign a buffer of management status of a CVE
- Search all the details of a CVE
- Check if there is an exploit on Github or Exploit-DB concerning a CVE
- Search for vulnerabilities for a specified product
- Manage your product list: search/add/delete a product, display your referenced product list
- Monitor the sources used by pollers
Email alerts can be sent in English or French. SECMON web UI now supports multi-user accounts.
CVE is polled using two methods of collection/correspondence:
- Keyword-based: allows you to be proactive on the retrieval of CVE by leaving a little bit of precision (no version check, just word matching) on the affected products (ex: “VMWare”, “Apache”).
- CPE based (Common Platform Enumeration) : allows the retrieval of CVE that only concern the product version entered (e.g. “Windows 10 1909”, “Apache 2.4.38”)