SKA: implement a very simple and fast karma attack
SKA allows you to implement a very simple and fast karma attack.
In information security, KARMA is an attack that exploits a behaviour of some Wi-Fi devices, combined with the lack of access point authentication in numerous WiFi protocols. It is a variant of the evil twin attack. Details of the attack were first published in 2004 by Dino dai Zovi and Shaun Macaulay.
Vulnerable client devices broadcast a “preferred network list” (PNL), which contains the SSIDs of access points to which they have previously connected and are willing to automatically reconnect without user intervention.[3][1] These broadcasts are not encrypted and hence may be received by any WiFi access point in range.[4][5] The KARMA attack consists in an access point receiving this list and then giving itself an SSID from the PNL, thus becoming an evil twin of an access point already trusted by the client.
Once that has been done, if the client receives the malicious access point’s signal more strongly than that of the genuine access point (for example, if the genuine access point is nowhere nearby), and if the client does not attempt to authenticate the access point, then the attack should succeed. If the attack succeeds, then the malicious access point becomes a man in the middle (MITM), which positions it to deploy other attacks against the victim device.
What distinguishes KARMA from a plain evil twin attack is the use of the PNL, which allows the attacker to know, rather than simply to guess, which SSIDs (if any) the client will automatically attempt to connect to
You can sniff probe requests to choice the fake AP name or, if you want, you could insert manually the name of the AP (evil twin attack).
When the target has connected to your WLAN you could active the HTTP redirection and perform a MITM attack.
Details
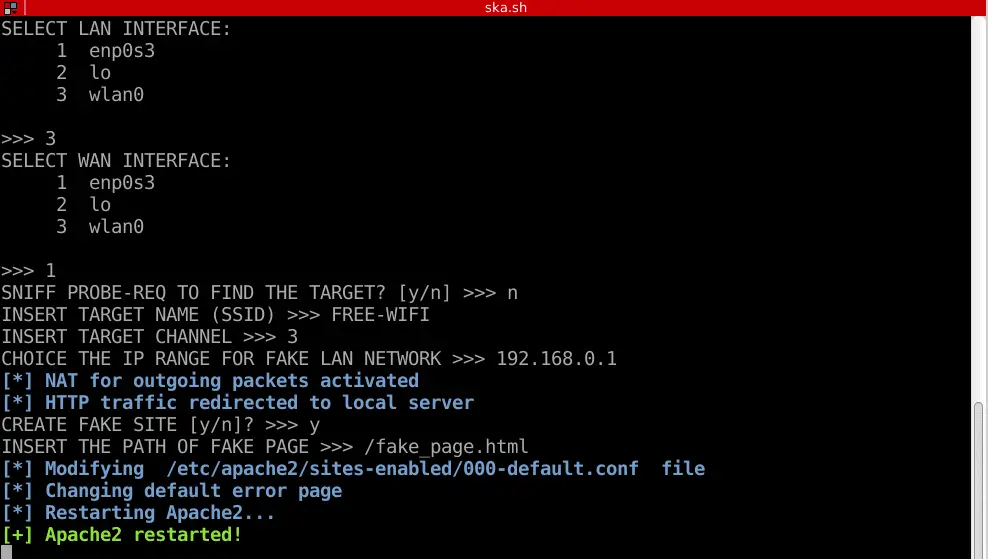
The script implements these steps:
- selection of NICs for the attack (one for LAN and one for WAN)
- the capture of probe-requests to choice the fake AP name (tcpdump)
- activation of fake AP (hostapd and dnsmasq)
- the new AP has a DHCP server which provides a valid IP to the target and prevents possible alerts on the victim devices
- activation of HTTP redirection (iptables)
- only HTTP requests are redirected to a fake site, while the HTTPS traffic continues to route normally
- activation of Apache server for hosting the phishing site
- at the end of the attack, the script cleans all changes and restores Apache configuration
Download
git clone https://github.com/Leviathan36/SKA.git
FAQ
SKA alerts you if there are some problems with NetworkManager demon or Apache configuration file. Anyway, you could find the answers to your problems in the links below:
- resolve Network Manager conflict 1
section: “Resolve airmon-ng and Network Manager Conflict”
- resolve Network Manager conflict 2
- disable dnsmasq
In summary
- Disable DNS line in your NetworkManager configuration file (look into /etc/NetworkManager/):
#dns=dnsmasq
- Insert the MAC of your wireless adapter between the unmanaged devices to allow hostapd works properly:
unmanaged-devices=mac:XX:XX:XX:XX:XX:XX
Disclaimer:
The author assumes no liability and are not responsible for any misuse or damage caused by this program.
Kaboom is distributed in the hope that it will be useful, but WITHOUT ANY WARRANTY; without even the implied warranty of MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the GNU General Public License for more details.
Copyright (C) 2019 Leviathan36
Source: https://github.com/Leviathan36/