Speakeasy v1.5.11 releases: emulate Windows kernel and user mode malware
Speakeasy
Speakeasy is a portable, modular, binary emulator designed to emulate Windows kernel and user mode malware.
Instead of attempting to perform dynamic analysis using an entire virtualized operating system, Speakeasy will emulate specific components of Windows. Specifically, by emulating operating system APIs, objects, running processes/threads, filesystems, and networks it should be possible to present an environment where samples can fully “execute”. Samples can be easily emulated in a container or in cloud services which allow for the great scalability of many samples to be simultaneously analyzed. Currently, Speakeasy supports both user mode and kernel mode Windows applications.
Before emulating, entry points are identified within the binary. For example, exported functions are all identified and emulated sequentially. Additionally, dynamic entry points (e.g. new threads, registered callbacks, IRP handlers) that are discovered at runtime are also emulated. The goal here is to have as much code coverage as possible during emulation. Events are logged on a per-entry-point basis so that functionality can be attributed to specific functions or exports.
Speakeasy is currently written entirely in Python 3 and relies on the Unicorn emulation engine in order to emulate CPU instructions. The CPU emulation engine can be swapped out and there are plans to support other engines in the future.
APIs are emulated in Python code in order to handle their expected inputs and outputs in order to keep malware on their “happy path”. These APIs and their structure should be consistent with the API documentation provided by Microsoft.
Changelog v1.5.11
- Many API handler improvements and additions.
- Many bug fixes.
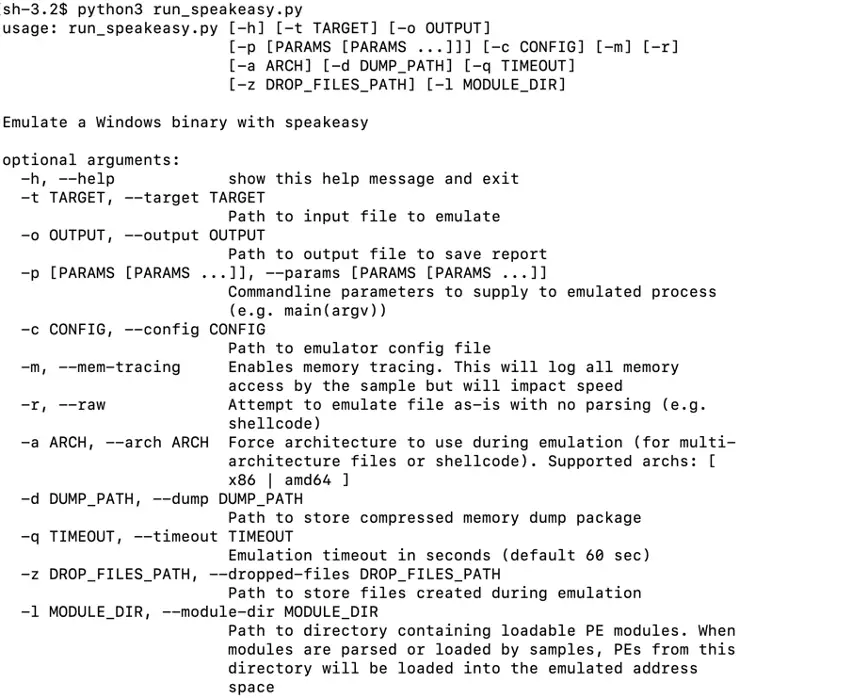
Download & Use
Copyright (c) 2020-present, FireEye, Inc.