sslscan v2.1.1 releases: tests SSL/TLS enabled services to discover supported cipher suites
sslscan tests SSL/TLS-enabled services to discover supported cipher suites. This is a fork of ioerror’s version of sslscan. Changes are as follows:
- Highlight SSLv2 and SSLv3 ciphers in output.
- Highlight CBC ciphers on SSLv3 (POODLE).
- Highlight 3DES and RC4 ciphers in output.
- Highlight PFS+GCM ciphers as good in output.
- Highlight NULL (0 bit), weak (<40 bit) and medium (40 < n <= 56) ciphers in output.
- Highlight anonymous (ADH and AECDH) ciphers in output (purple).
- Hide certificate information by default (display with
--get-certificate). - Hide rejected ciphers by default (display with
--failed). - Added TLSv1.1 and TLSv1.2 support (merged from twwbond/sslscan).
- Compiles if OpenSSL does not support SSLv2 ciphers (merged from digineo/sslscan).
- Supports IPv6 hostnames (can be forced with
--ipv6). - Check for TLS compression (CRIME, disable with
--no-compression). - Disable cipher suite checking
--no-ciphersuites. - Disable coloured output
--no-colour. - Removed undocumented -p output option.
- Added check for OpenSSL HeartBleed (CVE-2014-0160, disable with
--no-heartbleed). - Flag certificates signed with MD5 or SHA-1, or with short (<2048 bit) RSA keys.
- Support scanning RDP servers with
--rdp(credit skettler). - Added option to specify socket timeout.
- Added option for static compilation (credit dmke).
- Added
--sleepoption to pause between requests. - Disable output for anything than specified checks
--no-preferred. - Determine the list of CAs acceptable for client certificates
--show-client-cas. - Experimental build support on OSX (credit MikeSchroll).
- Flag some self-signed SSL certificates.
- Experimental Windows support (credit jtesta).
- Display EC curve names and DHE key lengths with OpenSSL >= 1.0.2
--no-cipher-details. - Flag weak DHE keys with OpenSSL >= 1.0.2
--cipher-details. - Flag expired certificates.
- Flag TLSv1.0 ciphers in output as weak.
- Experimental OSX support (static building only).
- Support for scanning PostgreSQL servers (credit nuxi).
- Check for TLS Fallback SCSV support.
- Added StartTLS support for LDAP
--starttls-ldap. - Added SNI support
--sni-name(credit Ken). - Support STARTTLS for MySQL (credit bk2017).
Changelog v2.1.1
- Work around a couple of dodgy TLS implementations.
Installation
- Windows
Pre-build cross-compiled Windows binaries are available here. - Linux
apt-get install build-essential git zlib1g-dev
apt-get build-dep openssl
git clone https://github.com/rbsec/sslscan.git
cd sslscan
make
make install
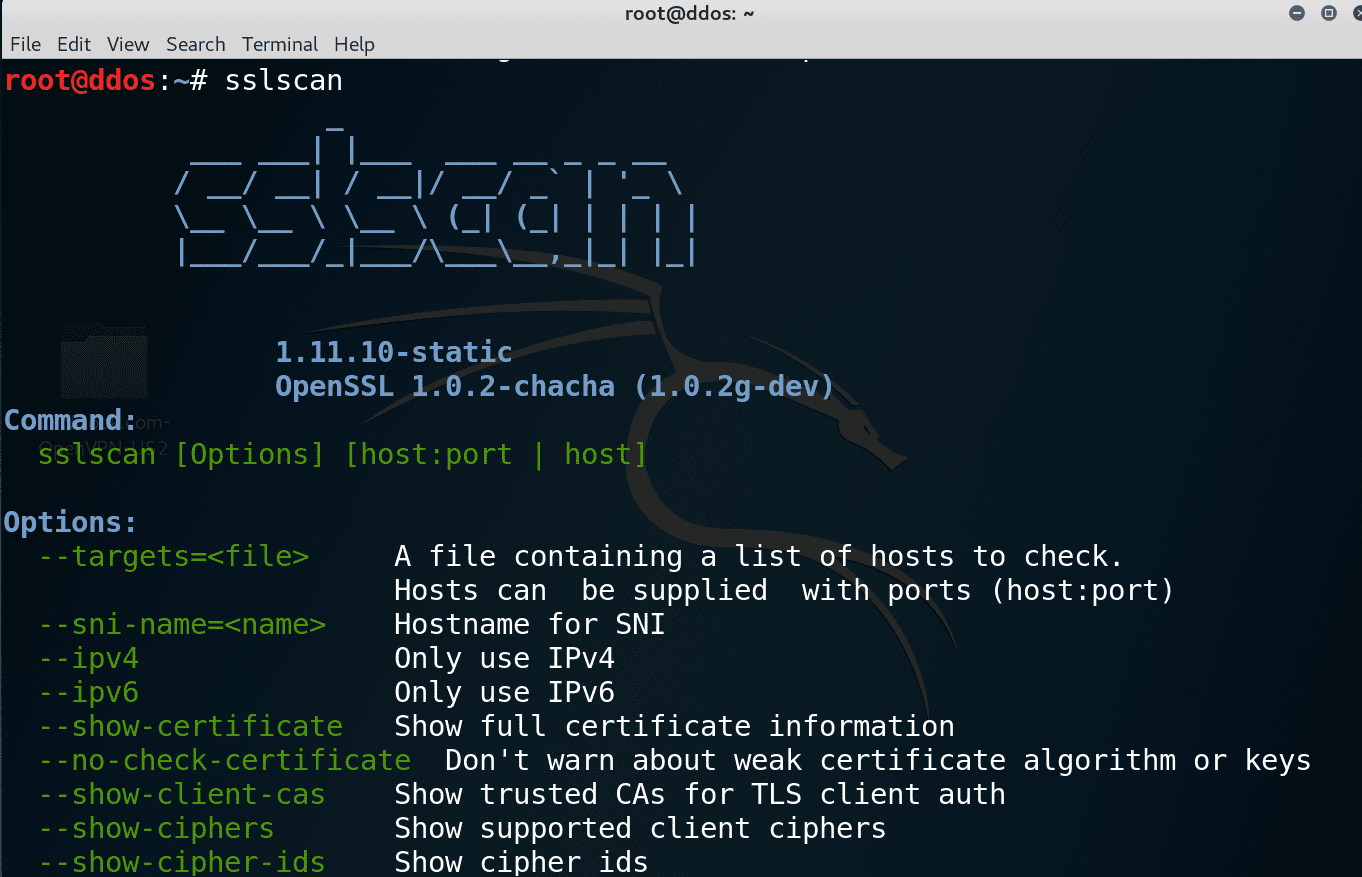
Use
Source: https://github.com/rbsec/






