Stracciatella v0.6 releases: Powershell runspace from within C# with AMSI and Script Block Logging disabled
Stracciatella v0.6
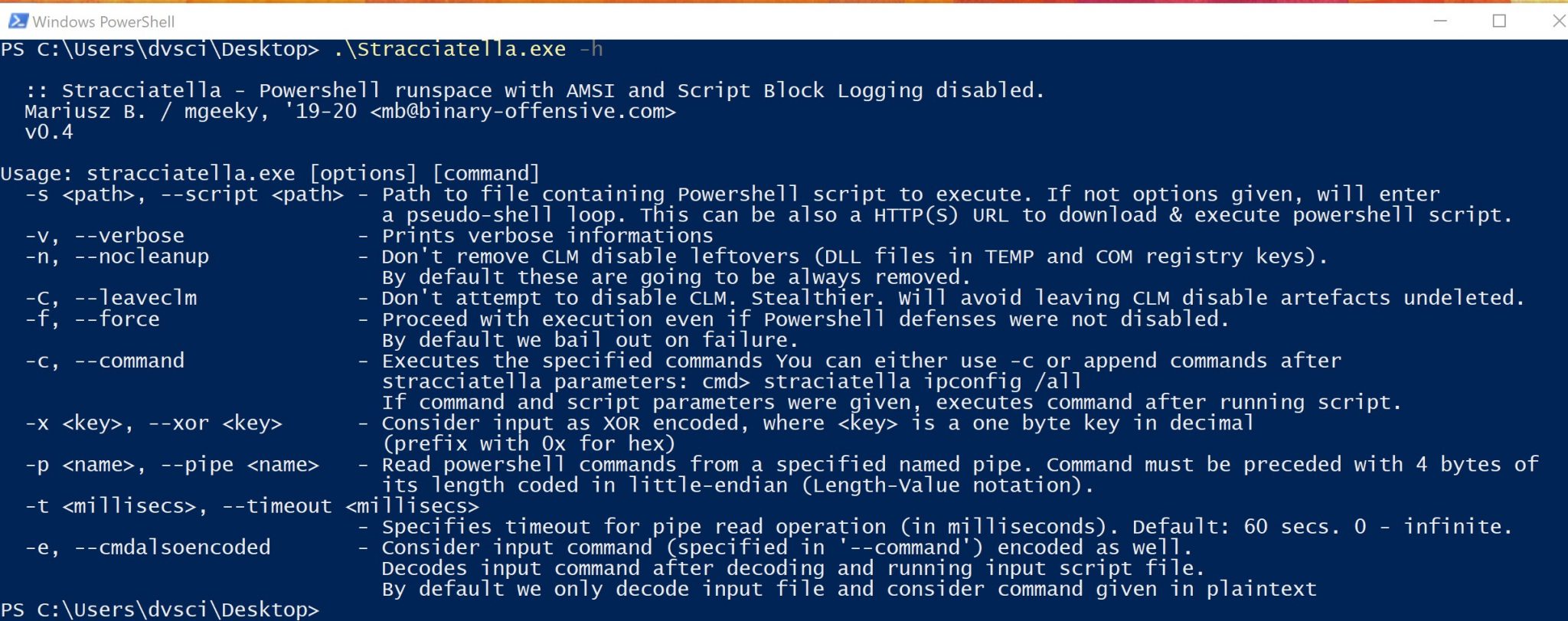
Powershell runspace from within C# (aka SharpPick technique) with AMSI and Script Block Logging disabled for your pleasure.
Nowadays, when Powershell got severely instrumented by use of techniques such as:
- AMSI
- Script Block Logging
- Transcript file
- Modules logging
- Constrained Language Mode
Advanced attackers must find ways to circumvent these efforts in order to deliver sophisticated adversarial simulation exercises. In order to help in these efforts, the following project was created.
This program builds on top of bypasses for specific techniques included in:
Which in turn was based on the following researches:
- Matt Graeber: https://github.com/mattifestation/PSReflect
- Matt Graeber: https://twitter.com/mattifestation/status/735261120487772160
- Avi Gimpel: https://www.cyberark.com/threat-research-blog/amsi-bypass-redux/
- Adam Chester: https://www.mdsec.co.uk/2018/06/exploring-powershell-amsi-and-logging-evasion/
- Ryan Cobb: https://cobbr.io/ScriptBlock-Logging-Bypass.html
- Ryan Cobb: https://cobbr.io/ScriptBlock-Warning-Event-Logging-Bypass.html
The SharpPick idea, meaning to launch powershell scripts from within C# assembly by the use of Runspaces is also not new and was firstly implemented by Lee Christensen (@tifkin_) in his:
Also, the source code borrows implementation of CustomPSHost from Lee.
This project inherits from the above researches and a great security community in order to provide a close-to-be-effective Powershell environment with defenses disabled on startup.
Now easily compiles with .NET 3.5, 4.0 whereas if compiled with .NET Framework 4.7.1+ and additional functionality is included that allows unloading DLLs constituting CLM bypass artifacts and attempts to delete them afterward (hardly working, to be honest).
Best mileage one gets with Stracciatella compiled with .NET 3.5.
OpSec
- This program provides functionality to decode passed parameters on the fly, using Xor single-byte decode
- Before launching any command, it makes sure to disable AMSI using two approaches
- Before launching any command, it makes sure to disable Script Block logging using two approaches
- This program does not patch any system library, system native code (think amsi.dll)
- Efforts were made to not store decoded script/commands excessively long, in order to protect itself from memory-dumping techniques governed by EDRs and AVs
- The resulting binary may be considered a bit too large, that’s because of Costura.Fody NuGet package is used which bundles System.Management.Automation.dll within resulting assembly
Changelog v0.6
- This release (hopefully) addresses two issues raised:
- fixes issue with
stracciatella-remote - refactored Script Block Logging bypass, which will hopefully restore that evasion
- fixes issue with
- Also the size was minimized by switching over to dnMerge from Costura.Fody and got rid of excessively big
System.Management.Automationdependency favoring Microsoft.PowerShell.5.ReferenceAssemblies instead. - This version also brings support for BOF.NET execution.
- Finally, it optimized the way Aggressor script internally works by minimizing impact of named-pipes RPC.
Download & Use
Copyright (C) 2019 mgeeky