the-bastion v3.14 releases: securely connect to devices
The Bastion
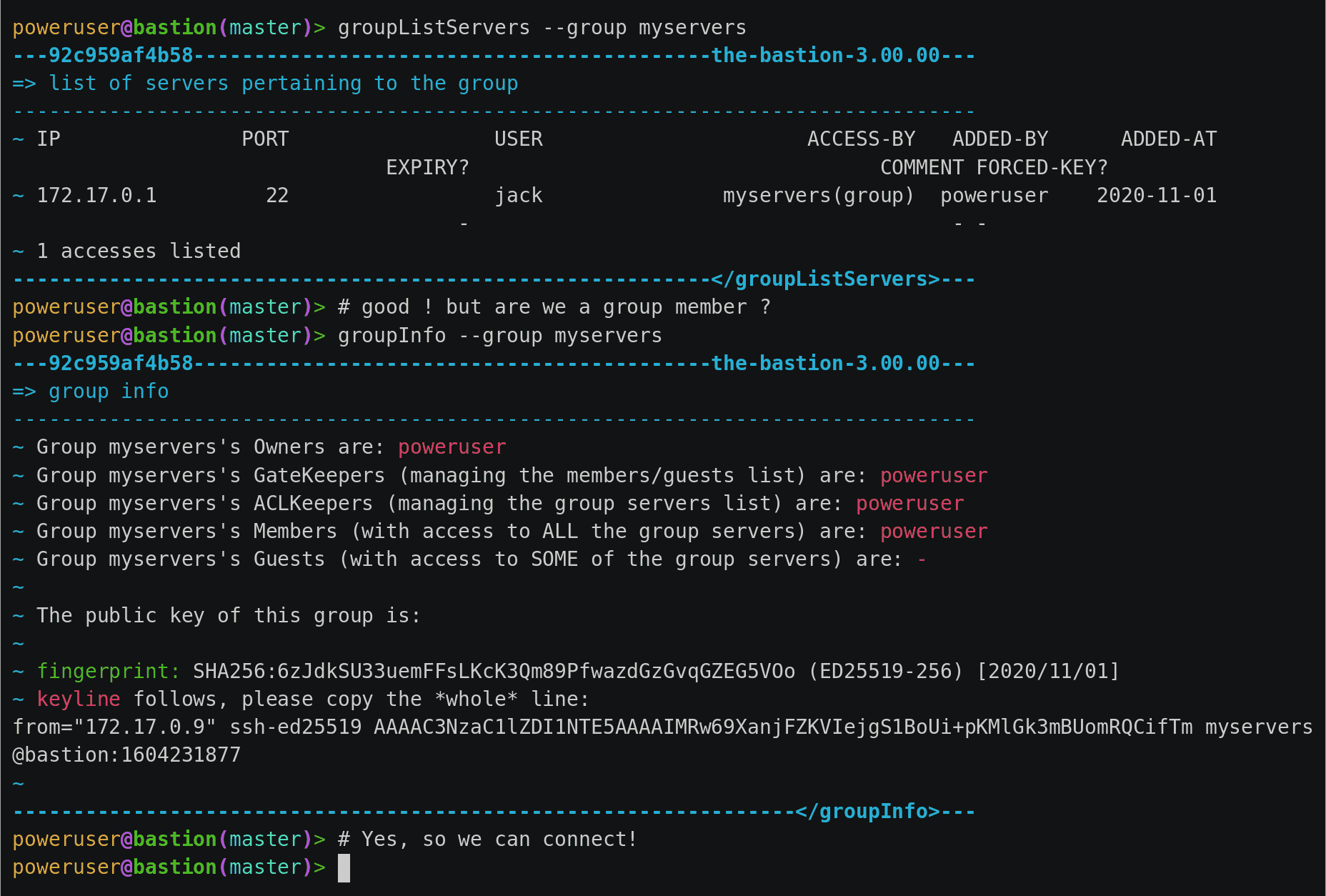
Bastions are a cluster of machines used as the unique entry point by operational teams (such as sysadmins, developers, database admins, …) to securely connect to devices (servers, virtual machines, cloud instances, network equipment, …), usually using ssh.
Bastions provides mechanisms for authentication, authorization, traceability, and auditability for the whole infrastructure.
Features
- Personal and group access schemes with group roles delegation to ensure teams autonomy without security trade-offs
- SSH protocol break between the ingress and egress connections (see other security measures)
- Self-reliance achieved through virtually no external dependencies (see other security measures)
- Interactive session recording (in standard ttyrec files)
- Non-interactive session recording (stdout and stderr through ttyrec)
- Extensive logging support through syslog for easy SIEM consumption
- Supports MOSH on the ingress connection side
- Supports scp passthrough, to upload and/or download files from/to remote servers
- Supports netconf SSH subsystem passthrough
- Supports Yubico PIV keys attestation checking and enforcement on the ingress connection side
- Supports realms, to create a trust between two bastions of possibly two different companies, splitting the authentication and authorization phases while still enforcing local policies
- Supports SSH password autologin on the egress side for legacy devices not supporting pubkey authentication, while still forcing proper pubkey authentication on the ingress side
- Supports telnet password autologin on the egress side for ancient devices not supporting SSH, while still forcing proper SSH pubkey authentication on the ingress side
- Supports HTTPS proxying with man-in-the-middle authentication and authorization handling, for ingress and egress password decoupling (mainly useful for network device APIs)
Changelog 3.14
💡 Highlights
This release fixes a possibly problematic behavior introduced in v3.13.00 when replacing sqlite logging of plugins output by ttyrec where the scp and sftp plugins, when downloading a file (from the remote server to the local machine through the bastion) would save the binary stream as part of the ttyrec file, possibly taking a lot of space when these plugins are often used.
Another, somehow niche, new feature is the support of so-called type8 and type9 hash types for egress passwords, mainly used by network devices. More information is available in the specific upgrade instructions link below.
📌 Changes
- feat: add type8 and type9 password hashes
- feat: add
stealth_stderr/stdoutttyrecsupport, enable it forscp&sftp
Install & Use
© Copyright 2021, OVHcloud