ThreatPursuit-VM: Threat Pursuit Virtual Machine
ThreatPursuit-VM
Threat Pursuit Virtual Machine (VM): A fully customizable, open-sourced Windows-based distribution focused on threat intelligence analysis and hunting designed for intel and malware analysts as well as threat hunters to get up and running quickly.
Instructions
Standard install
- Create and configure a new Windows Virtual Machine
- Ensure VM is updated completely. You may have to check for updates, reboot, and check again until no more remain
- Take a snapshot of your machine!
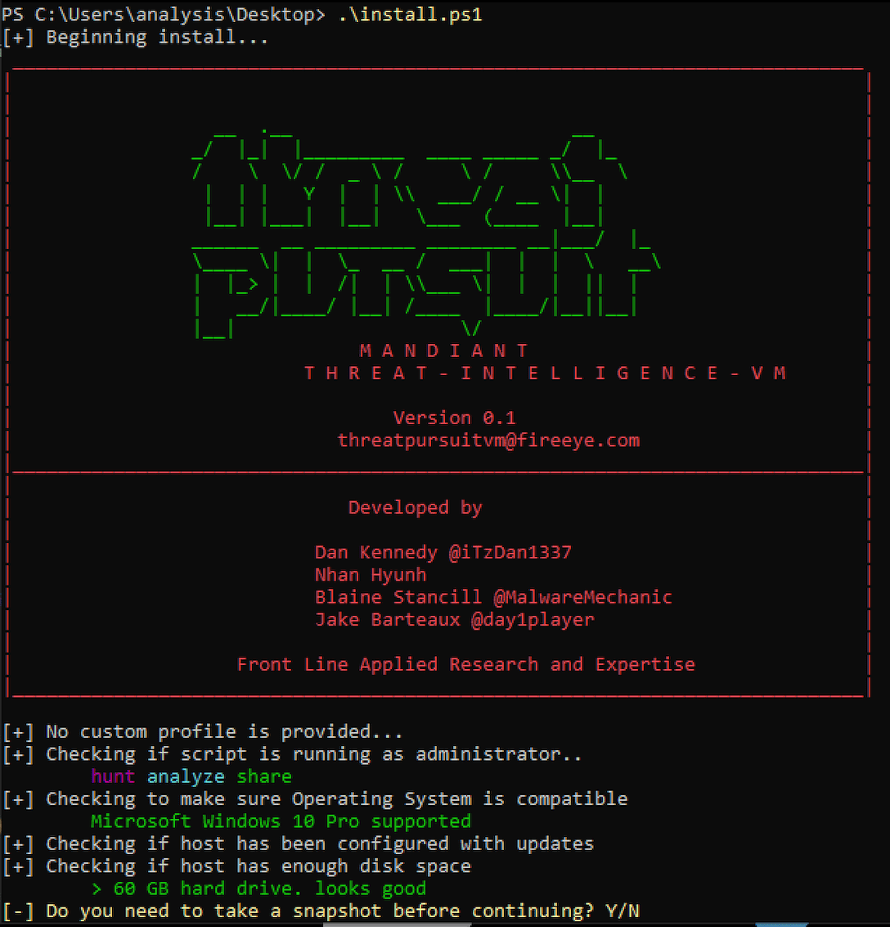
- Download and copy install.ps1 on your newly configured machine.
- Open PowerShell as an Administrator
- Unblock the install file by running Unblock-File .\install.ps1
- Enable script execution by running Set-ExecutionPolicy Unrestricted -f
- Finally, execute the installer script as follows: .\install.ps1 You can also pass your password as an argument: .\install.ps1 -password The script will set up the Boxstarter environment and proceed to download and install the ThreatPursuit VM environment. You will be prompted for the administrator password in order to automate host restarts during installation. If you do not have a password set, hitting enter when prompted will also work.
Installed Tools
Development, Analytics, and Machine Learning
- Shogun
- Tensorflow
- Pytorch
- Rstudio
- RTools
- Darwin
- Keras
- Apache Spark
- Elasticsearch
- Kibana
- Apache Zeppelin
- Jupyter Notebook
- MITRE Caret
- Python (x64)
Visualisation
- Constellation
- Neo4J
- CMAP
Triage, Modelling & Hunting
- MISP
- OpenCTI
- Maltego
- Splunk
- Microsoft MSTIC Jupyter and Python Security Tools
- MITRE ATT&CK Navigator
- Coretex Analyzer
- Greynoise API and GNQL
- threatcrowd API
- threatcmd
- ViperMonkey
- Threat Hunters Playbook
- MITRE TRAM
- SIGMA
- YETI
- Azure Zentinel
- AMITT Framework
Adversarial Emulation
- MITRE Calderra
- Red Canary ATOMIC Red Team
- Mordor Re-play Adversarial Techniques
- MITRE Caltack Plugin
- APTSimulator
- FlightSim
Information Gathering
- Maltego
- nmap
- intelmq
- dnsrecon
- orbit
- FOCA
Utilities and Links
- CyberChef
- KeepPass
- FLOSS
- peview
- VLC
- AutoIt3
- Chrome
- OpenVPN
- Sublime
- Notepad++
- Docker Desktop
- HxD
- Sysinternals
- Putty